What Is a Provider Directory? Purpose, Data, and Accuracy
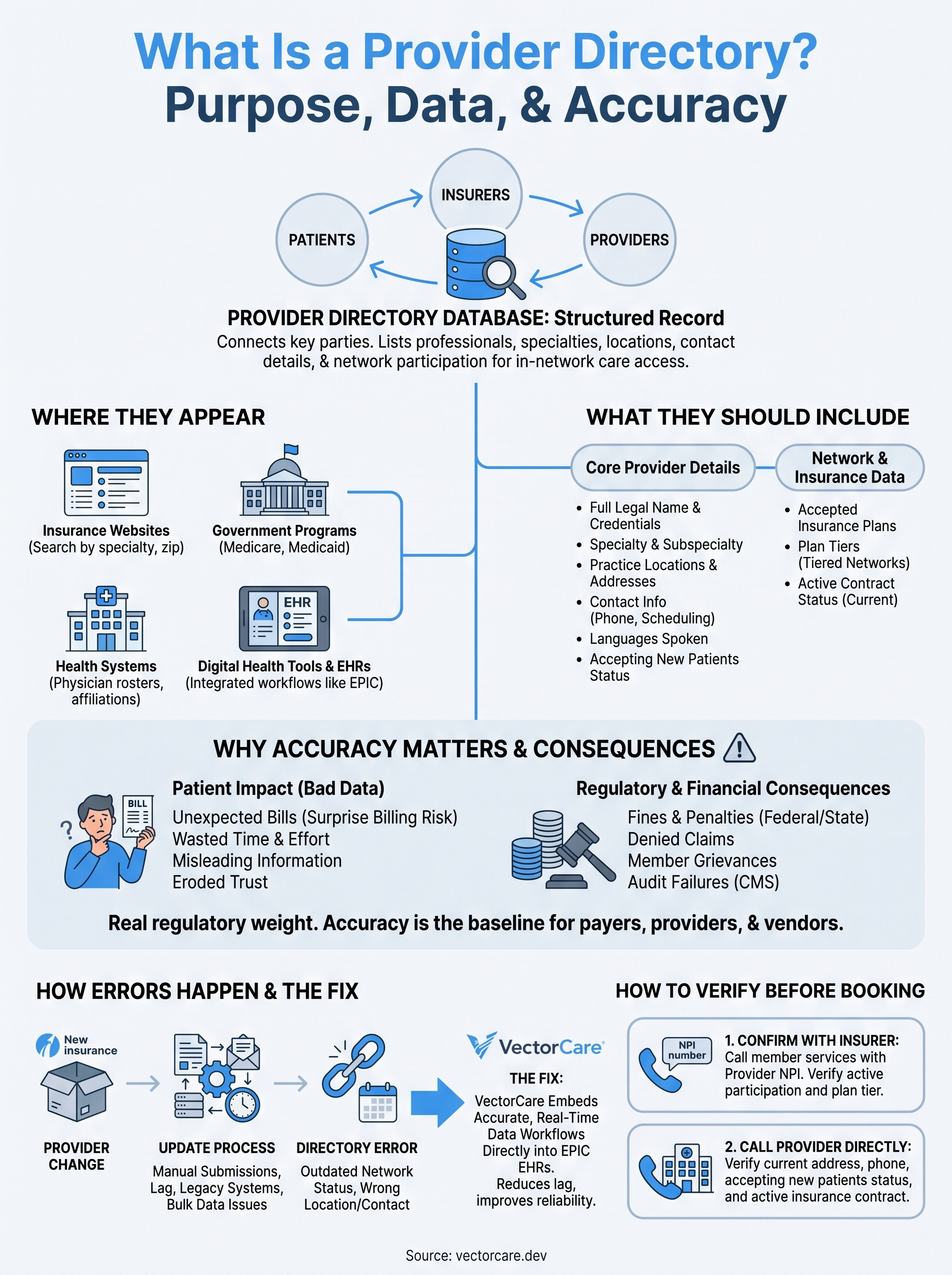
If you've ever searched for a doctor covered by your insurance plan, you've used a provider directory. At its core, understanding what is a provider directory means recognizing it as a structured database that lists medical professionals, their specialties, locations, contact details, and, critically, which insurance networks they participate in. Health plans, government programs, and health systems all maintain these directories so patients can find and access care from in-network providers.
But provider directories aren't just a convenience tool for patients. They carry real regulatory weight. Federal and state laws require health plans to keep directory data accurate and up to date, and failure to do so can result in fines, member grievances, and denied claims that erode trust between payers, providers, and patients. For healthcare vendors building tools that surface or manage this data, accuracy isn't optional, it's the baseline.
This is where platforms like VectorCare come in. Vendors who need to embed provider data workflows directly into EPIC EHR systems, think referral routing, network verification, or care navigation, can use our no-code platform to build and deploy those integrations in weeks instead of months. Below, we'll break down exactly what a provider directory contains, why the data matters so much, and what accurate directory management looks like in practice.
What a provider directory is and where you'll find it
A provider directory is a searchable database that lists healthcare professionals available within a specific network. When someone asks what is a provider directory, the answer goes beyond a simple list of names. It's a structured record that connects patients, insurers, and providers through verified data, making it possible to confirm whether a specific doctor or facility is covered under your plan before you schedule an appointment.
The core definition
At its most basic level, a provider directory functions as the official reference point for who participates in a given healthcare network. Each entry ties a provider's identity, their specialties, credentials, and locations to specific insurance contracts or health system affiliations. Without this connection, patients can't determine if their visit will be covered, and payers can't accurately process claims or meet network adequacy requirements.
Regulators treat directory accuracy as a direct measure of whether a health plan delivers on its coverage promises to members.
Where provider directories appear
You'll run into provider directories in several places depending on how you access healthcare. Insurance plan websites publish directories so members can search by specialty, zip code, or provider name before seeking care. Government programs like Medicare Advantage and Medicaid managed care plans are legally required to maintain public-facing directories. Health systems also publish their own directories to help patients navigate which physicians are on staff, at which locations, and under what insurance arrangements.
Digital health tools have extended where directory data shows up. EHR systems like EPIC now surface provider information directly inside clinical workflows, so care teams can verify referral networks and insurance participation without leaving the platform. This integration reduces manual lookup steps and brings directory data closer to the point of care.
Who maintains these records
Health plans are the primary stewards of provider directory data, and federal law, particularly through CMS regulations under the ACA, holds them accountable for keeping it current. Providers share responsibility by notifying payers when their information changes. Health systems and vendor platforms that aggregate or display this data inherit a portion of that accuracy burden, which is why the workflows managing directory updates carry significant operational weight.
The main parties responsible for directory accuracy include:
- Health plans, which must verify and publish network data
- Providers, who must submit updates when their information changes
- Technology vendors, who build and maintain the tools that surface this data
What information a good directory should include
When you understand what is a provider directory, you also need to know what separates a useful one from an incomplete one. A well-structured directory entry gives patients and care teams enough verified data to make a confident decision before booking an appointment or initiating a referral. Missing or vague fields push users back to the phone or force them to guess, which defeats the purpose entirely.
Core provider details
Every directory entry should give you a clear picture of the individual provider. That means full legal name, primary specialty, and board certifications listed in plain language. You also need the provider's practice locations with street addresses, phone numbers, and whether they're currently accepting new patients.
The key fields a complete provider entry should cover include:
- Name and credentials (MD, DO, NP, PA, and relevant certifications)
- Specialty and subspecialty
- Practice locations and affiliated facilities
- Contact information and scheduling access
- Languages spoken
- Accepting new patients status
Network and insurance data
Beyond the provider's personal and professional details, network participation data is what ties the directory to its core function. Each entry must specify which insurance plans the provider accepts, which tier they fall under in tiered networks, and whether those contracts are currently active.
A directory entry without current network participation data is functionally useless for a patient trying to avoid surprise bills.
Claims processing and referral routing also depend on this data being correct, so this layer of information carries the highest operational risk when it's wrong or outdated.
Why provider directory accuracy matters
Once you understand what is a provider directory, accuracy becomes the most critical issue to address. Stale or incorrect entries directly break the chain between what your insurance plan promises and what you can actually access. When a directory lists a provider as in-network who has since left that plan, you could end up with an unexpected bill that the plan is legally required to protect you from under federal surprise billing rules.
The patient impact of bad data
Patients rely on directory data to make real decisions about where to seek care. If a listed provider is no longer accepting new patients, has moved locations, or dropped from your network, you lose time and money pursuing care that doesn't match your expectations. Studies consistently show that a significant share of provider directory entries contain at least one error, which means the tool patients trust most often misleads them.
Common errors that affect patients include:
- Wrong address or phone number, leading to failed appointment attempts
- Incorrect network status, causing unexpected out-of-pocket costs
- Outdated "accepting new patients" flag, wasting scheduling effort
The CMS has cited inaccurate provider directories as one of the top compliance issues in Medicare Advantage audits.
Regulatory and financial consequences
Health plans face direct financial penalties when their directories fall below federal or state accuracy thresholds. CMS and state insurance regulators conduct audits, and plans that fail must remediate the data and can face significant fines.
Beyond regulatory risk, inaccurate directories generate member grievances, drive up call center volume, and damage a plan's standing with both members and contracted providers. That combination of compliance exposure and operational cost makes directory accuracy a business-critical function, not just a technical one.
How directories get updated and why errors happen
Understanding what is a provider directory also means understanding how it stays current, or fails to. The update process involves multiple parties exchanging data through a combination of manual submissions, automated feeds, and periodic outreach campaigns. Each handoff point in that chain is an opportunity for information to get lost, delayed, or entered incorrectly, which directly affects what you see when you search for an in-network provider.
The update process
Health plans rely on providers and their administrative staff to report changes like new locations, dropped insurance contracts, or updated accepting-new-patients status. Plans typically collect this data through credentialing portals, attestation surveys, and periodic phone verification. Some health systems feed directory data through automated FHIR-based integrations, but many providers still submit changes manually, which creates lag between when something changes and when the directory reflects it.

A provider can leave a network, move offices, or stop accepting patients months before that change appears in any public directory.
Where errors enter the system
Credentialing timelines are one of the biggest sources of directory errors. When a provider joins or leaves a practice group, that change often requires separate notifications to multiple payers, and not all of them get sent on time. Mergers, acquisitions, and group practice reorganizations create bulk data problems that overwhelm manual update workflows.
Technology gaps compound the issue. Many payers still use legacy database systems that don't sync in real time with provider submissions, leaving you with a directory that reflects network data from weeks or months ago rather than the actual current state of the network.
How to check a directory entry before booking
Before you schedule an appointment, verify the directory entry directly rather than assuming the listing reflects current reality. Knowing what is a provider directory means recognizing it as a starting point, not a guarantee. Errors are common enough that a quick two-step check can save you from an unexpected bill or a wasted trip.
Confirm network status with your insurer
Call your insurance plan's member services line and ask them to confirm that the specific provider is actively participating in your network. Give the representative the provider's National Provider Identifier (NPI), which you can look up through the CMS NPI Registry, to make sure they pull the exact record you need.
Written confirmation through your insurer's secure member portal creates a record you can reference if a billing dispute comes up later.
Request that the representative also confirm the provider's tier in your plan if you have a tiered network, since tier placement affects your out-of-pocket cost, not just whether the provider participates at all.
Call the provider's office directly
After confirming network status with your insurer, contact the provider's office to verify the address, phone number, and current patient availability. Practice staff typically know about recent contract changes before any directory reflects them, making this call your most reliable real-time data source.
Ask the office staff these questions directly:
- Is your insurance plan currently active at this specific location?
- Is the provider accepting new patients?
- What is the correct address and direct scheduling number?
Next steps
Understanding what is a provider directory gives you a clearer picture of how healthcare networks function and where data failures create real problems for patients, payers, and vendors alike. A directory is only as valuable as its accuracy and completeness, which means every party in the chain, from health plans to technology platforms, carries responsibility for keeping it reliable.
If you're a healthcare vendor building tools that surface provider data, network verification, or referral routing inside clinical workflows, the stakes are even higher. Your integration needs to reflect real-time, accurate directory data to deliver actual value to health systems and their care teams. Building and maintaining those workflows through legacy engineering methods takes too long and costs too much.
VectorCare helps you build and deploy SMART on FHIR apps directly inside EPIC in weeks, not months, so your product reaches the clinical point of care faster and with less overhead.
