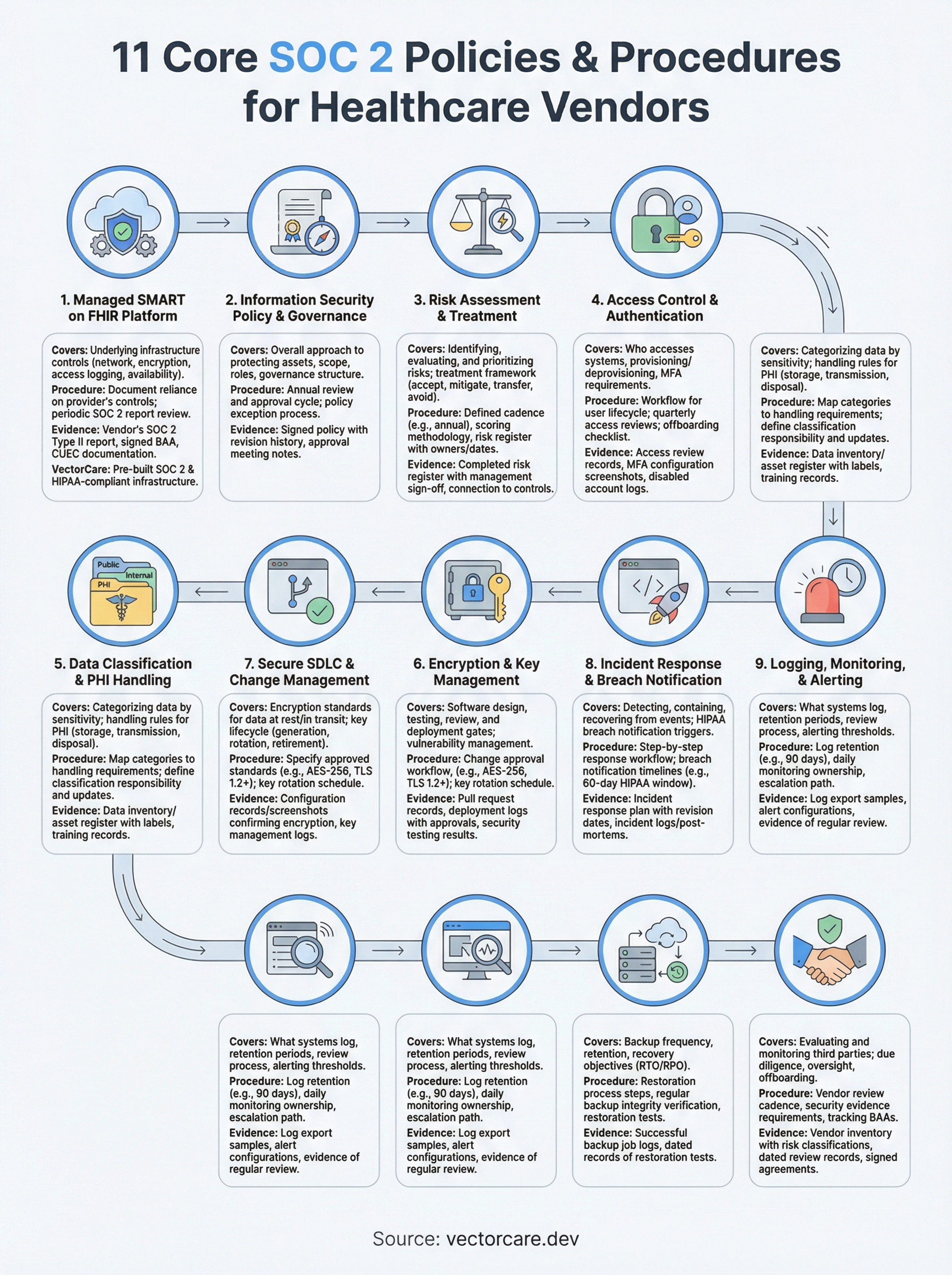
11 SOC 2 Policies And Procedures You Need For Compliance


Getting SOC 2 certified isn't just a checkbox exercise, for healthcare vendors trying to land contracts with health systems, it's often a hard requirement before anyone will even take a meeting. But when you start pulling together your SOC 2 policies and procedures, the scope of documentation can feel overwhelming fast. What exactly do auditors expect? Which policies are non-negotiable, and how detailed do they need to be?
The short answer: you need clearly documented, enforceable policies across every Trust Services Criteria that applies to your organization. That means covering everything from access control and incident response to risk management and vendor oversight, each backed by procedures your team actually follows, not just PDFs collecting dust in a shared drive. Auditors will test whether your day-to-day operations match what's on paper, so getting this right from the start saves you months of remediation later.
At VectorCare, we built SOC 2 compliance directly into our platform because we know healthcare vendors can't afford to treat security as an afterthought. Every SMART on FHIR app deployed through our no-code platform runs on SOC 2 and HIPAA-compliant infrastructure, so our customers can focus on winning health system contracts instead of wrestling with audit prep. That experience gives us a practical perspective on what these policies look like in action, not just in theory.
This article breaks down the 11 core SOC 2 policies and procedures you need to have in place before your audit, with guidance on what each one covers and how to document it effectively. Whether you're pursuing SOC 2 for the first time or tightening up existing controls, this list will give you a clear, actionable framework to work from.
1. Run SOC 2 controls on a managed SMART on FHIR platform
Starting your SOC 2 policies and procedures work on a managed, compliant infrastructure gives you a real head start. When your SMART on FHIR platform already handles foundational controls, you spend less time building from scratch and more time documenting what actually exists.
What it covers
A managed SMART on FHIR platform handles the underlying infrastructure controls that auditors examine directly: network security, data encryption, access logging, and system availability. Instead of standing up these controls independently, you inherit them from your platform provider, which narrows your audit scope considerably.
Your responsibility shifts to documenting the controls your vendor manages and confirming they hold their own SOC 2 report, ideally a Type II, to back up every claim they make about their security posture.
Procedures to document
Write a formal procedure describing how your organization relies on your provider's controls and how you verify those controls stay active. This includes a periodic review cycle where you pull your vendor's latest report and confirm no relevant exceptions exist. Document who owns this review, what they check, and where they log the results.
If your platform provider cannot produce a current SOC 2 Type II report, that gap becomes your gap during an audit.
Evidence auditors ask for
Auditors will ask for specific documentation during fieldwork. Make sure you can produce:
- Your vendor's SOC 2 Type II report with your internal review notes attached
- A signed Business Associate Agreement if your app handles PHI
- Documentation of complementary user entity controls (CUECs) and evidence you operate your side of those controls, such as managing your own user provisioning
Common mistakes to avoid
The most common mistake is assuming your platform handles everything. Subcontracting infrastructure does not subcontract accountability. You still need to map what your vendor covers and what you cover, and that boundary must be explicit in your documentation.
Skipping the CUEC review is another failure that surfaces fast during fieldwork, because auditors specifically look for evidence that you understood and acted on those shared responsibilities.
Practical setup for healthcare vendors
VectorCare's platform ships with SOC 2 and HIPAA-compliant infrastructure built in, including managed logging, encrypted data handling, and access controls aligned to the Trust Services Criteria. You receive the vendor controls documentation as part of onboarding, which means your audit evidence package starts populated rather than empty on day one.
2. Information security policy and governance
Your information security policy is the foundation document that ties all other SOC 2 policies and procedures together. Auditors treat it as a governing statement of intent, and every other policy in your program should trace back to it.
What it covers
This policy defines your organization's overall approach to protecting information assets, including scope, roles, responsibilities, and the guiding principles behind your security decisions. It also establishes the governance structure that keeps your security program functioning, such as who owns it, who reviews it, and how often it gets updated.
Procedures to document
Write a procedure covering the annual review and approval cycle for your information security policy. Document who is responsible for initiating the review, who has sign-off authority, and where you store the approved version. Your procedure should also describe how policy exceptions get requested and approved, because auditors routinely ask whether you have a formal process for handling deviations.
Evidence auditors ask for
Be ready to produce your signed and dated information security policy, along with meeting notes or approval records showing your last review cycle completed on time. Version history demonstrating the document has been actively maintained also carries weight.
A policy with no revision history looks like it was written the week before the audit, and auditors notice that pattern.
Common mistakes to avoid
Many teams write a policy that is too vague to be enforceable. Statements like "we protect data appropriately" tell auditors nothing. Be specific about obligations, timelines, and owners.
Practical setup for healthcare vendors
VectorCare's onboarding documentation gives you a pre-structured governance framework aligned to the Trust Services Criteria, so you can adapt it to your organization rather than starting with a blank document.
3. Risk assessment and risk treatment
A risk assessment is not optional when you are building out your SOC 2 policies and procedures program. Auditors look at this policy to confirm you have a systematic process for identifying threats before they cause damage, not after.

What it covers
This policy defines how your organization identifies, evaluates, and prioritizes risks to your information assets on a scheduled basis. It also establishes your treatment framework, meaning what you do once you know a risk exists: accept, mitigate, transfer, or avoid it.
Procedures to document
Write a procedure that specifies your risk assessment cadence, typically at minimum once per year, and how you conduct the assessment. Document the methodology you use to score risks, such as a likelihood-times-impact matrix, and who participates in the process. Your treatment decisions for each identified risk should be logged in a risk register that includes the assigned owner and a target remediation date.
A risk register with no remediation dates or owners tells auditors that nothing will actually get fixed.
Evidence auditors ask for
Auditors will request your completed risk register with dated entries, evidence of management review and sign-off, and documentation showing how identified risks connect to specific control activities in your environment.
Common mistakes to avoid
Running a risk assessment once and never updating it is the most common failure here. Stale risk registers signal to auditors that your program is not operating continuously, which is a core requirement of SOC 2.
Practical setup for healthcare vendors
VectorCare's managed platform reduces your residual risk surface significantly by handling infrastructure-level threats, which means your risk register starts with fewer critical gaps to remediate from day one.
4. Access control and authentication
Access control is one of the most scrutinized areas in any SOC 2 audit. Auditors want to see that your organization follows a least-privilege model, meaning users get access only to what their role requires, and that you enforce this consistently across every system in scope.
What it covers
This policy governs who can access your systems, how you grant and revoke that access, and what authentication mechanisms protect it. It covers user provisioning, role assignments, privileged access management, and your multi-factor authentication (MFA) requirements across all in-scope environments.
Procedures to document
Write a procedure that details your user provisioning and deprovisioning workflow, including how quickly you revoke access after an employee or contractor leaves. Document your process for quarterly access reviews, where a designated owner confirms that every active account still maps to a current, authorized user.
Access that lingers after an employee exits is one of the fastest findings auditors log, so your offboarding procedure needs a hard deadline and a paper trail.
Evidence auditors ask for
Auditors will ask for access review records showing who conducted them and when, screenshots or exports confirming MFA is enforced on production systems, and logs showing terminated accounts were disabled within your documented timeframe.
Common mistakes to avoid
Many vendors skip formal access reviews or run them inconsistently. Informal reviews with no recorded output give auditors nothing to test against.
Practical setup for healthcare vendors
Your SOC 2 policies and procedures for access control become simpler when your platform centralizes user management. VectorCare handles role-based access enforcement at the infrastructure layer, giving you a documented baseline to build your own access policy on top of.
5. Data classification and PHI handling
Data classification sits at the intersection of SOC 2 and HIPAA for most healthcare vendors, making it one of the most important policies in your entire SOC 2 policies and procedures program. Without a clear system for labeling and handling different types of data, you cannot enforce appropriate controls consistently across your environment.
What it covers
This policy defines how your organization categorizes data based on sensitivity, and what handling rules apply to each category. For healthcare vendors, this means explicitly identifying where Protected Health Information (PHI) lives in your systems and what restrictions govern how your team stores, transmits, and disposes of it.
Procedures to document
Write a procedure that maps your data categories to specific handling requirements, including PHI, internal-only data, and public information. Document who is responsible for classifying new data assets when they enter your environment, and how you update that classification when data moves between systems or changes sensitivity level.
If your team cannot tell you where PHI lives in your environment without hesitation, your classification procedure needs more work before an audit begins.
Evidence auditors ask for
You will need a current data inventory or asset register showing classification labels, along with records demonstrating your team received training on handling rules for each category.
Common mistakes to avoid
Treating all data as equally sensitive sounds cautious but actually obscures where your real risk lives and makes control enforcement harder to demonstrate to auditors.
Practical setup for healthcare vendors
VectorCare's platform isolates PHI within HIPAA-compliant infrastructure by default, giving you a clear boundary to reference when documenting your classification policy.
6. Encryption and key management
Encryption controls show auditors that your data stays protected whether it's sitting in a database or moving across a network. For healthcare vendors, this area of your SOC 2 policies and procedures program also overlaps directly with HIPAA technical safeguards, so getting it documented correctly covers two compliance obligations at once.
What it covers
This policy governs how your organization encrypts data at rest and in transit, including the specific algorithms and key lengths you require. It also defines your key management lifecycle, covering how encryption keys get generated, stored, rotated, and eventually retired without exposing protected data during any transition.
Procedures to document
Write a procedure that specifies your approved encryption standards, such as AES-256 for data at rest and TLS 1.2 or higher for data in transit, and document who is responsible for verifying these standards remain active across all in-scope systems. Your key management procedure should define rotation schedules and access restrictions, along with what happens to data protected by a compromised key.
Encryption configured correctly but documented nowhere still counts as a gap during an audit.
Evidence auditors ask for
Be ready to produce configuration records or screenshots confirming encryption is enabled on your databases and storage services, along with key management logs showing rotation events occurred on schedule.
Common mistakes to avoid
Many vendors enable encryption but never document the key custodian role, leaving auditors with no evidence that anyone is actually responsible for key security.
Practical setup for healthcare vendors
VectorCare manages encryption at the infrastructure layer by default, including key handling, which means your documentation effort focuses on confirming and inheriting controls rather than building them independently.
7. Secure SDLC and change management
Your software development lifecycle (SDLC) policy tells auditors that code changes go through a controlled, documented process before they reach production. Without it, any developer with access could push untested changes directly to live systems, creating both security and availability risks that are hard to defend during an audit.
What it covers
This policy governs how your organization designs, tests, reviews, and deploys software changes, including what gates a change must pass before production deployment. It also covers vulnerability management practices embedded in your development workflow, such as code reviews, dependency scanning, and penetration testing schedules.
Procedures to document
Write a procedure that defines your change approval workflow, including who can approve production deployments and what testing evidence must exist before approval is granted. Document your branch protection rules, peer review requirements, and how you track changes from initial request through final deployment in your version control system.
A change management procedure with no documented approval chain gives auditors no way to confirm that untested code cannot reach production.
Evidence auditors ask for
You will need pull request or merge request records showing peer reviews were completed, along with deployment logs that tie specific code changes to approval records. Auditors also ask for evidence that security testing occurred as part of your release process.
Common mistakes to avoid
Relying on informal verbal approvals with no written record is the most common gap here. Undocumented approvals fail the same as no approvals during fieldwork.
Practical setup for healthcare vendors
VectorCare manages infrastructure-level change controls within its platform, so your SOC 2 policies and procedures for SDLC can focus on your application layer rather than the underlying environment.
8. Incident response and breach notification
Your incident response policy defines how your organization detects, contains, and recovers from security events before they spiral into larger problems. For healthcare vendors, this policy also triggers HIPAA breach notification obligations, making it a critical part of your SOC 2 policies and procedures program.

What it covers
This policy governs how your team identifies and classifies security incidents, including what qualifies as a notifiable breach under HIPAA, and what response steps each severity level triggers. It also defines the communication chain your team follows from initial detection through post-incident review.
Procedures to document
Write a procedure that maps out your incident response workflow step by step, from detection and triage through containment, eradication, recovery, and the final lessons-learned review. Your procedure must include breach notification timelines, specifically the 60-day window HIPAA requires for notifying affected individuals and the Department of Health and Human Services.
If your breach notification timelines are not written down before an incident happens, you will almost certainly miss them under pressure.
Evidence auditors ask for
Auditors will request your incident response plan with revision dates, along with any incident logs or post-mortems from the prior audit period showing the process was actually followed.
Common mistakes to avoid
Many teams document a response process but never run a tabletop exercise to test whether it holds up under realistic conditions. Auditors increasingly ask for evidence of testing, not just documentation.
Practical setup for healthcare vendors
VectorCare's platform provides built-in monitoring and alerting at the infrastructure layer, giving your incident response team a faster starting point for detection and containment when an event occurs.
9. Logging, monitoring, and alerting
Continuous logging and alerting give auditors concrete evidence that your organization detects and responds to security events in real time rather than discovering them weeks after the fact.
What it covers
This policy defines what your systems log, how long you retain those logs, and who reviews them. It also covers your alerting thresholds and the tools your team uses to surface anomalies before they escalate into incidents that require formal reporting.
Procedures to document
Write a procedure specifying your log retention period (SOC 2 auditors typically want at least 90 days of readily accessible logs) and who owns the daily monitoring function. Document your alert escalation path so it is clear who receives notifications and how quickly they must respond to each severity level.
Logs that exist but are never reviewed give auditors no assurance that your monitoring program is actually operating continuously.
Evidence auditors ask for
Be ready to produce log export samples showing the types of events captured, along with alert configuration records and evidence of regular review, such as ticketing system entries tied to specific alert triggers within your audit period.
Common mistakes to avoid
Many vendors configure logging but never define a formal review cadence, leaving audit fieldwork with no evidence that anyone acted on the data being collected. Alert fatigue from poorly tuned thresholds is equally problematic, because unchecked noise trains your team to ignore genuine threats over time.
Practical setup for healthcare vendors
VectorCare builds infrastructure-level logging and monitoring directly into its platform, giving your SOC 2 policies and procedures program a ready-made evidence base that significantly reduces the setup work your team needs to complete before an audit begins.
10. Backup and disaster recovery
Your backup and disaster recovery policy tells auditors that your organization can restore operations after data loss or a system failure without putting your customers' data at permanent risk. For healthcare vendors, downtime is not just a business problem; it directly affects patient care workflows, which raises the stakes on this section of your SOC 2 policies and procedures program significantly.
What it covers
This policy defines your backup frequency, retention periods, and recovery objectives for all systems that fall within your audit scope. It also establishes your recovery time objective (RTO) and recovery point objective (RPO), which are the maximum tolerable downtime and acceptable data loss thresholds your organization commits to meeting.
Procedures to document
Write a procedure that specifies how often backups run, where they are stored, and how you verify backup integrity on a regular schedule. Your procedure must also describe the step-by-step restoration process, including who initiates recovery, what systems restore first, and how you confirm data integrity after a restore completes.
A backup procedure with no documented restoration test means auditors have no evidence your backups actually work when it matters.
Evidence auditors ask for
Auditors will request backup job logs showing successful completion across the audit period, along with dated records of restoration tests confirming your RTO and RPO commitments are achievable in practice.
Common mistakes to avoid
Running backups without ever testing restoration is the most common failure here. Untested backups carry no assurance value during fieldwork.
Practical setup for healthcare vendors
VectorCare manages automated backups and infrastructure-level recovery controls within its platform, giving your team a documented baseline that reduces the gap between your policy commitments and your actual recovery capabilities.
11. Vendor management and third-party risk
Your vendor management policy ensures that the security risks introduced by third-party tools, subprocessors, and service providers stay within your acceptable boundaries. Auditors treat this as a direct extension of your SOC 2 policies and procedures program because a weak vendor can undermine controls you have spent months building internally.
What it covers
This policy defines how your organization evaluates and monitors third parties that access, process, or store data on your behalf. It covers initial due diligence before onboarding, ongoing oversight during the relationship, and offboarding procedures when a vendor relationship ends.
Procedures to document
Write a procedure that specifies your vendor review cadence and what security evidence you require from each vendor before approval. Document how you track the status of signed Business Associate Agreements for any vendor touching PHI, and who owns follow-up when a vendor's SOC 2 report lapses.
A vendor without a current SOC 2 report or BAA creates an audit finding that traces directly back to your program, not theirs.
Evidence auditors ask for
Auditors will request your vendor inventory list with risk classifications, along with dated records of security reviews and executed agreements for in-scope vendors.
Common mistakes to avoid
Many teams onboard vendors quickly and never schedule a follow-up review, leaving outdated assessments in the register for years. Auditors test whether your oversight is continuous, not one-time.
Practical setup for healthcare vendors
VectorCare enters every engagement with a signed BAA and current SOC 2 documentation, so your vendor register starts with a compliant entry rather than a gap you need to close before fieldwork begins.
Next steps for an audit-ready program
Your SOC 2 policies and procedures program becomes audit-ready when every policy on this list has a clear owner, a documented procedure behind it, and real evidence your team follows it consistently. Start by mapping which controls you own versus which your infrastructure provider manages, because that boundary determines how much documentation work sits with your team. Prioritize the policies with the longest evidence collection timelines first, specifically access reviews, risk assessments, and backup restoration tests, since those take months to accumulate the records auditors want to see.
For healthcare vendors building on EPIC integrations, the fastest path to a compliant foundation is choosing a platform that handles the hardest infrastructure controls before your audit prep even begins. VectorCare ships with SOC 2 and HIPAA-compliant infrastructure built in, so your team starts with fewer gaps to close. See how VectorCare reduces your compliance burden from day one.
The Future of Patient Logistics
Exploring the future of all things related to patient logistics, technology and how AI is going to re-shape the way we deliver care.