HIPAA Compliance Explained: Rules, Requirements, And Steps


Every healthcare vendor building toward EHR integration hits the same wall: HIPAA compliance explained in terms that actually make sense and translate into action. HIPAA isn't optional, and it isn't vague, it's a structured set of federal rules that dictate how protected health information (PHI) must be handled, stored, and transmitted. Get it wrong, and you're looking at fines, lost contracts, and a reputation that's nearly impossible to rebuild.
This article breaks down the three core HIPAA rules, Privacy, Security, and Breach Notification, along with who must comply, what the requirements look like in practice, and the concrete steps to get there. Whether you're a digital health startup, a clinical decision support vendor, or a remote patient monitoring company, understanding these rules is foundational to doing business with health systems.
At VectorCare, we built our no-code SMART on FHIR platform with HIPAA and SOC2 compliance baked in from the start, because healthcare vendors integrating with EPIC shouldn't have to become compliance engineers on top of everything else. But compliance is still your responsibility to understand, regardless of the tools you use. So let's walk through exactly what HIPAA requires, why each rule exists, and how to stay on the right side of enforcement.
Why HIPAA compliance matters
HIPAA compliance matters because health data is uniquely sensitive, and federal law enforces that sensitivity with significant financial consequences. The Health Insurance Portability and Accountability Act was signed in 1996, and its scope expanded substantially through the HITECH Act in 2009. If you're a healthcare vendor, understanding HIPAA compliance explained in full isn't just useful background; it's a prerequisite for operating in this market.
The financial penalties are real and tiered
The Office for Civil Rights (OCR) at the U.S. Department of Health and Human Services (HHS) enforces HIPAA violations across four penalty tiers based on culpability and knowledge. At the lowest tier, violations an organization wasn't aware of carry fines starting at $141 per violation. At the highest tier, willful neglect that remains uncorrected can reach $2,134,831 per violation category per year. OCR has issued settlements to health systems, insurers, and vendors alike, so these numbers are not hypothetical.
A single unaddressed security gap can push your organization into a higher penalty tier, even if you didn't know the gap existed.
Ignorance doesn't protect you. Reasonable diligence is the standard, not perfection, but inaction reads as negligence to OCR investigators. If your organization handles protected health information in any form, you're expected to know the rules and apply them consistently.
Health systems use compliance as a contract filter
Beyond penalties, HIPAA compliance functions as a market access filter. Health systems run formal vendor risk assessments before signing contracts, and your compliance posture is a core part of that evaluation. If you can't demonstrate proper safeguards, signed Business Associate Agreements, and documented policies, you don't move past procurement.
For vendors selling into hospital systems, academic medical centers, or large physician groups, your compliance documentation carries as much weight as your product demo. Buyers in those organizations hold personal liability for the vendors they onboard, and they won't sign with a vendor who can't show documented proof of compliance.
Reputation damage outlasts the fine
Fines get paid and regulatory reviews eventually close. Reputation damage from a data breach is harder to recover from. When patient data is compromised, health system partners, existing clients, and prospects all update their risk assessments around your organization. Healthcare is a relationship-driven industry where trust accumulates slowly.
A breach investigation, even one that ends with a modest fine, puts your sales pipeline on pause while procurement teams wait for resolution. For early-stage vendors, that delay can be existential. For growth-stage vendors, it breaks momentum at exactly the wrong time.
Building compliance early scales with your business
Starting compliance work early means you're not rebuilding your data handling practices every time you add a new health system client. Organizations that invest in proper policies, documented risk analysis, and security controls from the beginning find that each new partnership adds operational load, but not structural chaos.
Your compliance framework becomes a repeatable process, not a scramble before each contract deadline. Vendors who embed HIPAA requirements into their product architecture and operational workflows are the ones who win more health system contracts without stretching their teams every time a new opportunity appears.
What PHI and ePHI mean in practice
Protected health information, or PHI, is any information that can identify a specific individual and relates to their past, present, or future health condition, healthcare services they've received, or payment for those services. The definition is broader than most people expect. HIPAA doesn't just protect medical records sitting in a hospital database; it covers any combination of data that could link a person to their health status or care history.
What counts as PHI
HIPAA identifies 18 specific identifiers that, when combined with health information, create protected health information. These include obvious elements like names, dates of birth, Social Security numbers, and phone numbers, but also less obvious ones like geographic data more specific than a state, full-face photographs, and any unique identifying number tied to a device or account. If your application collects or processes any of these alongside health-related data, you're handling PHI under federal law.
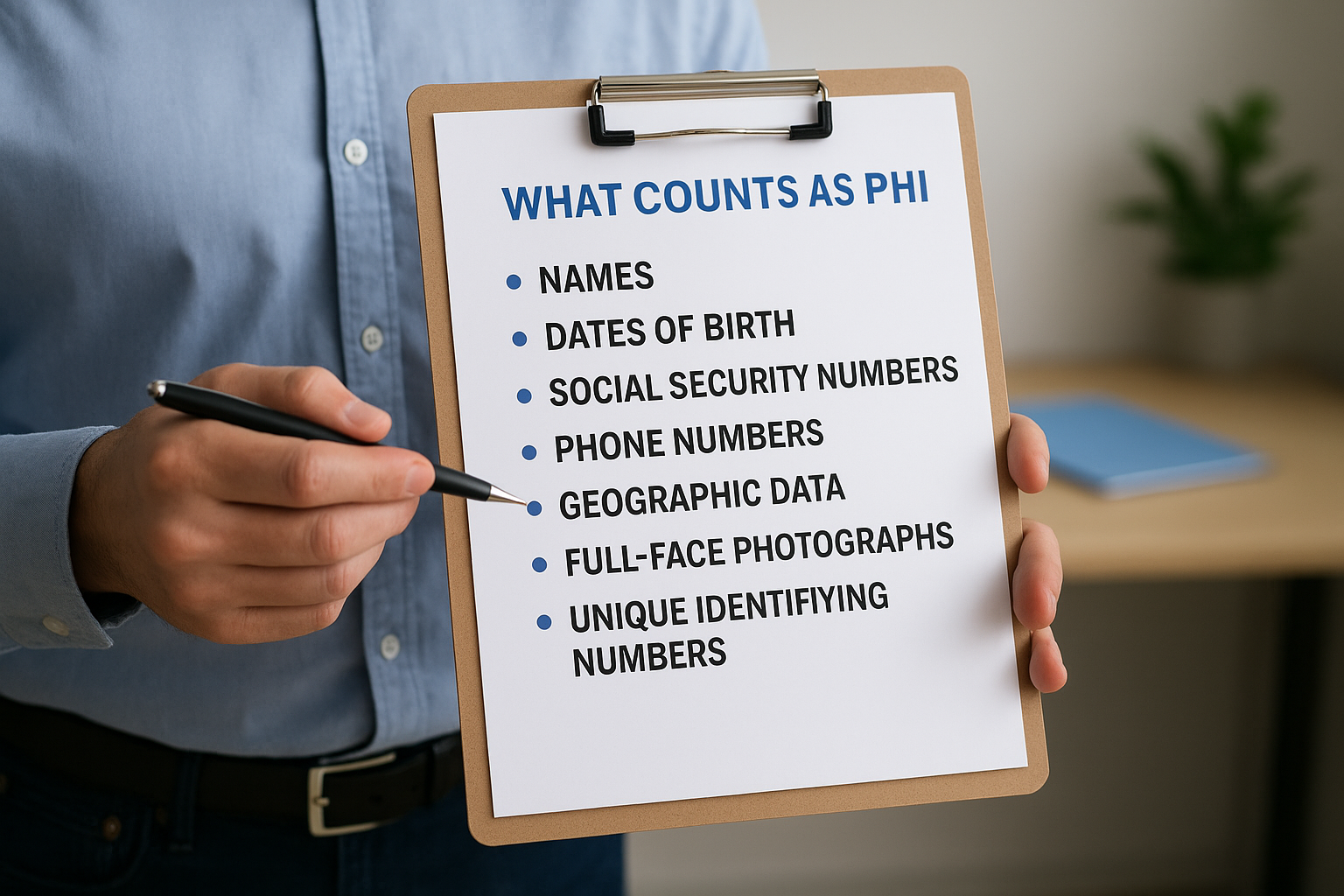
The threshold matters here. A patient's diagnosis alone isn't PHI if there's no way to connect it to a specific person. But the moment you attach a name, a date, a location, or a device identifier to that diagnosis, the combination becomes protected information that HIPAA governs. Most healthcare vendor applications cross that line quickly, often without the team realizing it.
What makes ePHI different
Electronic protected health information, or ePHI, is simply PHI that's stored, transmitted, or processed in electronic form. This distinction matters because the HIPAA Security Rule applies specifically to ePHI, while the Privacy Rule covers PHI in all formats, including paper and verbal communication. If your platform pulls patient data from an EHR, stores it in a database, or transmits it over an API, you're working with ePHI.
Every API call that returns patient data is, by definition, a transmission of ePHI and must be protected accordingly.
Understanding where ePHI flows through your system is the starting point for hipaa compliance explained in real operational terms. You can't secure what you haven't mapped. Before you build safeguards, you need to trace every point where patient data enters your application, where it gets stored, and where it leaves. That data flow map becomes the foundation for your risk analysis, your security controls, and your vendor agreements.
Who must comply with HIPAA
HIPAA applies to two distinct categories of organizations: covered entities and business associates. With hipaa compliance explained in full, the boundary between these two categories becomes clear, and where your organization falls determines exactly what obligations you carry. Getting that classification wrong is one of the most common mistakes vendors make when entering the healthcare market.
Covered entities: the direct handlers
Covered entities are the primary regulated parties under HIPAA. This category includes healthcare providers that transmit health information electronically, health plans including insurers and employer-sponsored plans, and healthcare clearinghouses that process non-standard health data into standard formats. If your organization falls into any of these groups, HIPAA's full set of rules applies to you directly by law.
The three types of covered entities break down as follows:
- Healthcare providers: Hospitals, physician practices, clinics, pharmacies, and any provider that submits claims or transmits PHI electronically
- Health plans: Individual and group insurance plans, HMOs, Medicare, Medicaid, and employer health benefit plans
- Healthcare clearinghouses: Entities that process health data from non-standard formats into HIPAA-compliant standard formats
Business associates: the vendor layer
If you're a digital health vendor, a remote patient monitoring company, or a clinical decision support tool, you almost certainly fall into the business associate category. A business associate is any vendor or subcontractor that creates, receives, maintains, or transmits PHI on behalf of a covered entity. This includes software platforms, data analytics companies, cloud hosting providers, and anyone else who touches patient data while performing services for a covered entity.
If your platform pulls data from an EHR or stores any patient information to deliver your service, you are a business associate under HIPAA, regardless of your company size.
Your business associate status comes with real obligations. You must sign a Business Associate Agreement (BAA) with each covered entity you serve, implement appropriate safeguards under the Security Rule, and report breaches to your covered entity partners. Subcontractors you use who also handle PHI become downstream business associates, and you're responsible for ensuring they sign BAAs and maintain their own compliance. The chain of accountability runs through your entire vendor stack, not just your direct relationship with the health system.
The HIPAA rules you need to know
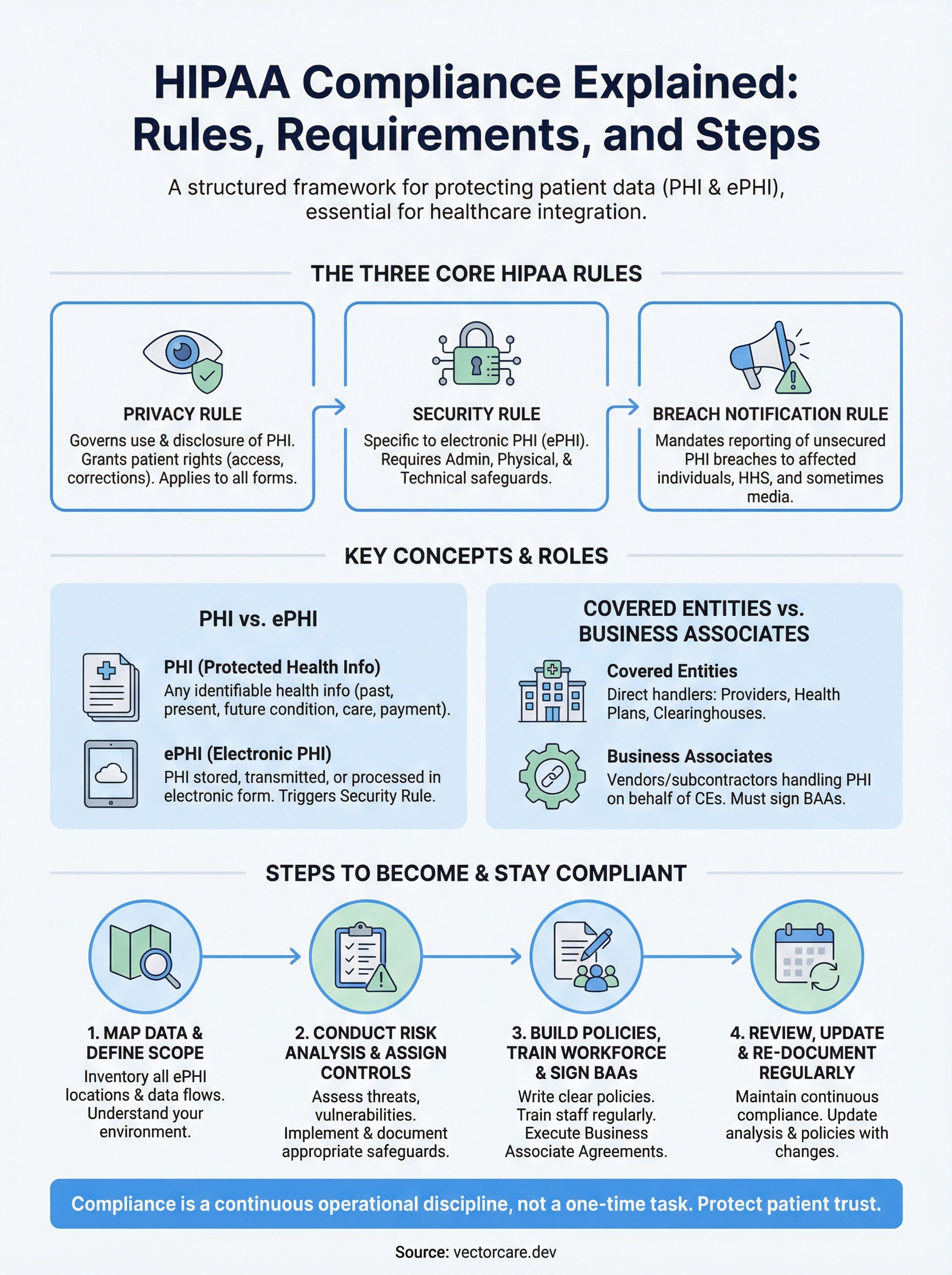
Three federal rules form the foundation of HIPAA compliance explained in full: the Privacy Rule, the Security Rule, and the Breach Notification Rule. Each rule carries distinct obligations and addresses a different dimension of how your organization must handle protected health information. Understanding all three is not optional if you're building products that connect to patient data.

The Privacy Rule
The Privacy Rule establishes baseline standards for how PHI can be used and disclosed. It applies to covered entities directly and extends to business associates through their BAAs. The rule also gives patients specific rights over their health information, including the right to access their own records, request corrections, and receive a notice of how their data is used.
For vendors, the Privacy Rule means you can only use or disclose PHI in ways your covered entity clients have authorized, or that the rule explicitly permits. Minimum necessary standard is the governing principle: you collect and use only the PHI required to perform your specific function. If your application pulls 20 data fields but only needs 8 to deliver your service, that gap is a compliance problem, not a minor inefficiency.
The Security Rule
The Security Rule focuses entirely on ePHI and requires covered entities and business associates to implement physical, administrative, and technical safeguards to protect electronic patient data. Unlike the Privacy Rule, which covers all forms of PHI, the Security Rule is specific to electronic systems: your databases, APIs, cloud infrastructure, and any device that processes or stores patient records.
The Security Rule doesn't prescribe a fixed list of controls; it requires safeguards that are reasonable and appropriate for your organization's size, complexity, and risk profile.
This flexibility is intentional but demanding. You must assess your own risks and document the controls you've selected based on that assessment. A startup serving two health systems has different obligations than an enterprise platform serving hundreds, but both face the same standard of documented, justified decision-making.
The Breach Notification Rule
The Breach Notification Rule requires covered entities and business associates to notify affected individuals, HHS, and in some cases the media, when unsecured PHI is improperly accessed, disclosed, or used. As a business associate, your obligation is to notify your covered entity partner within 60 days of discovering a breach, at which point the covered entity takes over notification responsibilities.
Whether an incident triggers notification often depends on a four-factor risk assessment that examines the nature of the data involved, who accessed it, whether it was actually viewed, and whether the risk to patients has been mitigated.
Security Rule safeguards: admin, physical, technical
The Security Rule organizes its requirements into three safeguard categories: administrative, physical, and technical. With hipaa compliance explained across these three layers, the intent becomes clear: protecting ePHI requires coordinated controls across your people, your facilities, and your systems. Each category contains a mix of required specifications you must implement and addressable specifications you must either implement or document a justified reason for not implementing.
Administrative safeguards
Administrative safeguards are the policy and process layer of your security program. They govern how your organization assigns responsibility for security, trains staff, manages access to systems, and responds to security incidents. Required elements include designating a Security Officer, conducting a formal workforce training program, and implementing a sanctions policy for employees who violate your security policies.
Administrative safeguards carry the most weight in OCR audits because they document the intentionality behind every other control you've put in place.
You also need a contingency plan that covers data backup, disaster recovery, and emergency access procedures. Workforce clearance procedures and termination protocols belong here too. The goal is ensuring that the people inside your organization handle ePHI with consistent, documented accountability at every stage of the employment lifecycle.
Physical safeguards
Physical safeguards cover access to the spaces and devices where ePHI exists. For software vendors operating in cloud environments, this category often feels abstract, but it still applies. Your workstation security policies, device disposal procedures, and media reuse controls all fall under physical safeguards. If your team members access patient data on laptops or mobile devices, you need written policies governing how those devices are secured, stored, and decommissioned.
Facility access controls apply even when your infrastructure lives in a third-party data center. You need to verify that your hosting provider maintains physical security controls for the servers running your application, and you need documentation proving it. That's part of what a well-structured Business Associate Agreement with your cloud provider should address.
Technical safeguards
Technical safeguards are the system-level controls that protect ePHI as it moves through and rests inside your application. Required controls include access controls that assign unique user IDs, audit controls that log who accessed what data and when, integrity controls that detect unauthorized changes to ePHI, and transmission security that encrypts data in transit. Encryption of data at rest is addressable rather than required, but skipping it without documented justification creates serious audit exposure.
Core requirements: risk analysis, policies, BAAs
With hipaa compliance explained across the Privacy, Security, and Breach Notification Rules, three operational requirements tie everything together in practice: a formal risk analysis, written policies and procedures, and signed Business Associate Agreements. These aren't optional documentation exercises. They are the concrete deliverables that OCR expects to see during an audit and that health system procurement teams ask for before they sign a contract with you.
Risk analysis
Your risk analysis is the starting point for every security decision your organization makes about ePHI. HIPAA requires you to identify all the places where ePHI exists in your environment, assess the likelihood and impact of potential threats to that data, and document the controls you've chosen to address each identified risk. This isn't a one-time task. You must repeat the analysis when your environment changes: when you add new infrastructure, onboard new subcontractors, or expand your data flows.
A risk analysis that sits in a folder and never gets updated is treated the same as no risk analysis at all during an OCR investigation.
The output of your risk analysis feeds directly into your security control decisions. If you identify a high-probability threat to your API layer, your control selection for transmission security should reflect that priority. Document your reasoning at every step so that your decisions are defensible if you face regulatory scrutiny.
Written policies and procedures
Written policies translate your security controls into operational expectations for your team. HIPAA requires covered entities and business associates to maintain documented policies covering access management, incident response, workforce training, device security, and data disposal, among other areas. These policies must be reviewed and updated periodically, not filed away after initial creation.
Your procedures sit underneath your policies and describe exactly how each requirement gets executed day to day. If your policy says you revoke access when an employee leaves, your procedure should document the specific steps, timelines, and responsible roles that make that happen consistently.
Business Associate Agreements
A Business Associate Agreement (BAA) is a legally binding contract that documents each party's HIPAA obligations when PHI changes hands. Before you receive any PHI from a covered entity, you need a signed BAA in place. Your BAA must specify permitted uses of PHI, breach notification timelines, and your obligation to flow down requirements to any subcontractors who handle the data on your behalf. No BAA means no compliant business relationship, regardless of how strong your technical controls are.
Steps to become and stay HIPAA compliant
With hipaa compliance explained across its core rules and requirements, you need a practical sequence to turn that knowledge into a functioning compliance program. Compliance isn't a single milestone you reach and move on from. It's an operational discipline that your organization maintains, adjusts, and documents continuously as your product and partnerships evolve.

Map your data and define your scope
Your first step is building a complete inventory of every location where ePHI exists in your environment: databases, APIs, third-party integrations, developer tools, and internal communication channels. Until you know where patient data lives and how it moves through your system, every other compliance decision rests on an incomplete foundation. Document your data flows visually so your team shares a common understanding of the scope before you start assessing risk.
Conduct your risk analysis and assign controls
Once your data map is in place, run a formal risk analysis that evaluates threats and vulnerabilities across each ePHI location. Score each risk by likelihood and potential impact, then select security controls that address your highest-priority gaps. Document your control selection reasoning at every step so you can demonstrate to OCR or a health system procurement team exactly why you made each decision. Assign a named owner to each control so accountability doesn't get lost as your team grows.
A documented risk analysis with clear ownership is the single most important artifact you can produce to demonstrate compliance readiness.
Build your policy library and train your workforce
Your written policies and procedures need to cover access management, incident response, device security, workforce training, and data disposal at a minimum. Write each policy in plain language your team will actually follow. Training shouldn't be a one-time checkbox: your workforce needs regular, documented training sessions that reflect your current policies and the actual risks in your environment.
Sign BAAs and validate your vendor stack
Before you receive PHI from any covered entity, put a signed Business Associate Agreement in place. Then audit your own vendor stack to identify every subcontractor that touches ePHI, cloud infrastructure, logging tools, analytics platforms, and require them to sign BAAs as well. Your compliance obligations flow downstream, and a gap in a subcontractor's security posture becomes your exposure.
Review, update, and re-document on a schedule
Set a recurring review cadence of at least once per year, or any time your infrastructure, team, or data flows change significantly. Outdated policies and stale risk analyses are treated as compliance failures, not technicalities. Build the review cycle into your operational calendar so it happens consistently rather than only when a new health system contract triggers a scramble.
Final takeaway
HIPAA compliance explained at its core comes down to one operating principle: protect patient data with documented, consistent, and repeatable controls across every layer of your organization. The Privacy, Security, and Breach Notification Rules aren't independent checklists; they're an integrated framework that only works when all three are active at once. Your risk analysis feeds your policy decisions, your policies govern your workforce behavior, and your BAAs extend that accountability to every vendor in your stack.
Compliance isn't a pre-launch task you complete and archive. It's a continuous discipline that grows with your product and your partnerships. The vendors who win more health system contracts are the ones who treat compliance as a built-in operational advantage, not a last-minute requirement. If you're building toward EPIC EHR integration and want a platform with HIPAA and SOC2 compliance already in place, explore what VectorCare's no-code SMART on FHIR platform can do for your deployment timeline.
The Future of Patient Logistics
Exploring the future of all things related to patient logistics, technology and how AI is going to re-shape the way we deliver care.