SOC 2 Audit Definition: What It Covers And Why It Matters


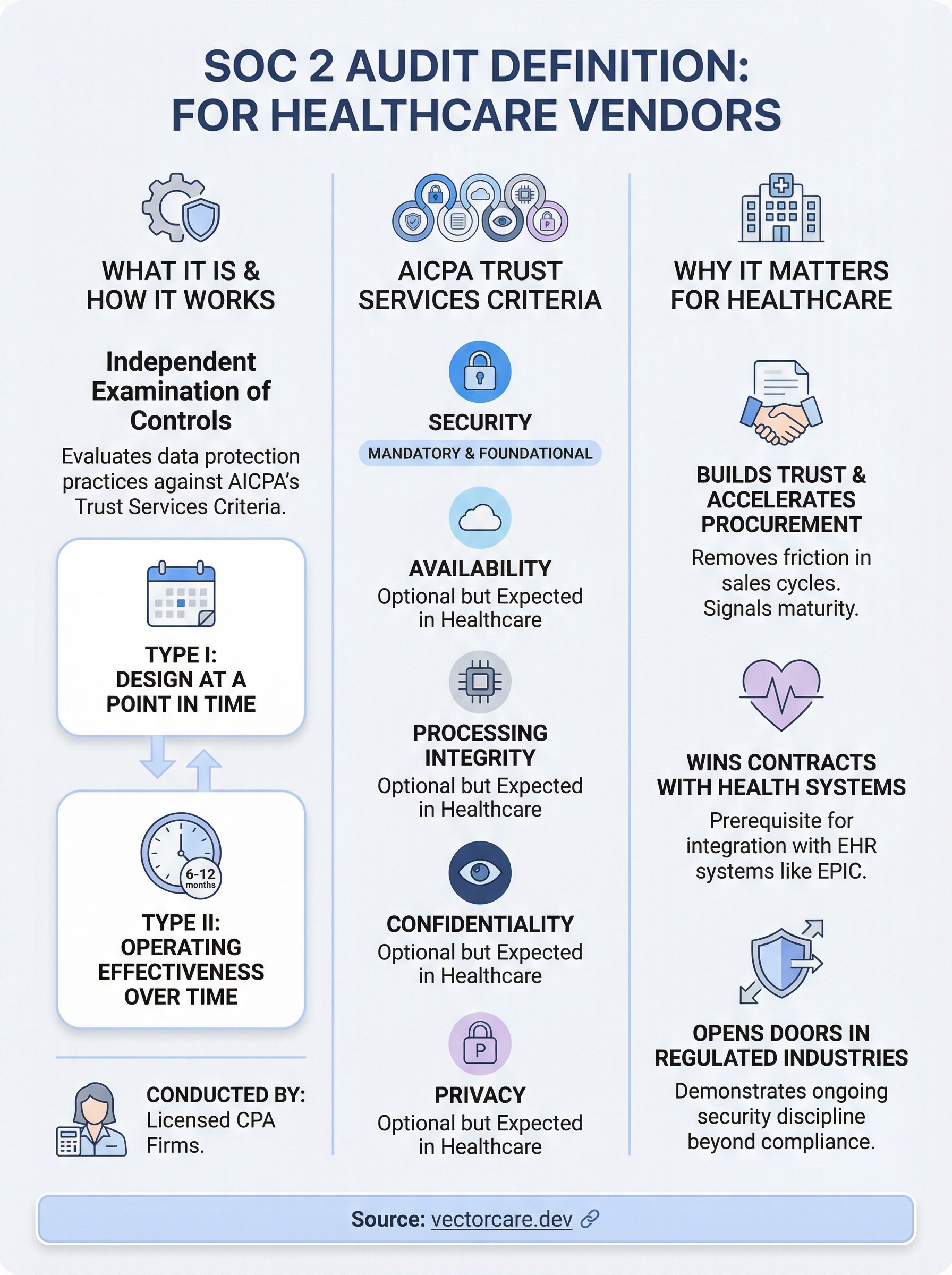
A SOC 2 audit definition starts simple enough: it's an independent examination of how a service organization protects customer data, conducted against the AICPA's Trust Services Criteria. But the reality behind those words carries serious weight, especially for healthcare vendors trying to win contracts with health systems. If you can't prove your security posture through a recognized framework, most procurement conversations end before they begin.
SOC 2 audits evaluate five Trust Services Criteria: security, availability, processing integrity, confidentiality, and privacy. Each criterion maps to specific controls your organization must design, implement, and maintain. For healthcare vendors building integrations with EHR systems like EPIC, SOC 2 compliance isn't optional, it's table stakes. Health systems expect it, and without it, your product sits outside the clinical workflow where it needs to live. At VectorCare, we built SOC 2 compliance directly into our no-code SMART on FHIR platform because we know our customers can't afford gaps in their security credibility.
This article breaks down what a SOC 2 audit actually covers, walks through each of the five Trust Services Criteria, explains the difference between Type I and Type II reports, and clarifies why this standard matters for service organizations in healthcare. Whether you're preparing for your first audit or evaluating a vendor's SOC 2 report, you'll leave with a clear, working understanding of the entire framework.
What a SOC 2 audit is
A SOC 2 audit is an independent, third-party examination of a service organization's controls as they relate to the security, availability, processing integrity, confidentiality, and privacy of the data it handles. The American Institute of Certified Public Accountants (AICPA) developed the framework, and only licensed CPA firms are authorized to perform the audit and issue the resulting report. Unlike a certification you earn once and display indefinitely, a SOC 2 report reflects a specific point in time or a defined period, which means the work of maintaining compliance is continuous.
The AICPA and the Trust Services Criteria
The AICPA's Trust Services Criteria (TSC) is the formal standard against which auditors measure your controls. The framework specifically targets technology and cloud service providers that store, process, or transmit customer data. When you work through the full soc 2 audit definition, you recognize that the TSC isn't a checklist you complete once. It's a living set of requirements that your organization must embed into daily operations, not something you dust off before an annual review.
Security is the only criterion required in every SOC 2 audit. The remaining four criteria, Availability, Processing Integrity, Confidentiality, and Privacy, are optional but frequently expected by enterprise customers and health systems. Most service organizations include all five in their scope, particularly in healthcare, where demonstrating a broad security posture directly influences whether a health system puts you on a vendor shortlist. You choose the criteria based on what your customers care about and what your service actually touches.
The Security criterion is mandatory in every SOC 2 engagement; without it, there is no valid report.
Who conducts a SOC 2 audit
Only a licensed CPA firm with expertise in information security controls can conduct a SOC 2 audit. The auditor functions as an independent attestor, meaning they carry no financial relationship with your organization beyond the engagement fee. They review your documented policies, control evidence, and system configurations to determine whether your controls are suitably designed (Type I) or operating effectively over time (Type II).
Your internal team does not run the audit, but your people carry most of the preparation burden. You'll work closely with the auditor to define scope, gather evidence, walk through control narratives, and respond to findings. Selecting a qualified auditor with SaaS or healthcare experience is worth the extra effort, because they understand which controls carry the most weight for your specific risk profile and can flag gaps before they become findings.
What the audit actually examines
At its core, a SOC 2 audit examines whether your organization's controls match the commitments you make to customers. Auditors look at your policies and procedures, the technical controls protecting your systems, how you manage access and change, how you respond to incidents, and how your vendors handle data on your behalf. Every control needs documented evidence to support it, not just a verbal confirmation during a walkthrough.
For healthcare vendors building EHR integrations, auditors pay close attention to access management, encryption practices, audit logging, and incident response procedures. These controls map directly to how health systems evaluate vendor risk before granting access to their clinical environment. Showing a clean SOC 2 report signals that your security program has survived independent scrutiny, which removes one of the most common blockers in enterprise procurement conversations.
What a SOC 2 audit covers
The full soc 2 audit definition only makes sense once you understand what auditors actually examine during an engagement. The scope runs across five Trust Services Criteria, each representing a different dimension of how your organization handles customer data. Together, these criteria form the complete picture of your security posture that enterprise buyers and health systems expect to see before they sign a contract.
The Security criterion
Security sits at the center of every SOC 2 engagement. Auditors examine whether your organization has controls in place to protect customer data against unauthorized access, disclosure, and damage. This includes logical access controls, network firewalls, intrusion detection, encryption at rest and in transit, and your change management process. Every control needs documented evidence, not just a written policy that describes what you plan to do.
Without strong Security criterion controls, the other four criteria carry little meaning for your auditor or your customers.
For healthcare vendors integrating with EPIC, the Security criterion maps directly to what health systems scrutinize during vendor risk assessments. Your ability to demonstrate multi-factor authentication, role-based access control, and a tested incident response plan tells a procurement team that your organization operates with real discipline, not just good intentions.
The four optional criteria
The remaining criteria are technically optional, but most enterprise customers include them in scope requirements when evaluating vendors. Here is what each one covers:

| Criterion | What auditors examine |
|---|---|
| Availability | Whether your systems are accessible and operational as promised in your service agreements |
| Processing Integrity | Whether data is processed completely, accurately, and on time without unauthorized modification |
| Confidentiality | Whether data designated as confidential is protected from unauthorized disclosure throughout its lifecycle |
| Privacy | Whether you collect, use, retain, and dispose of personal information in line with your stated privacy notice |
For healthcare vendors, Availability and Confidentiality are typically the criteria health system customers scrutinize most closely. Downtime inside a clinical workflow costs far more than revenue alone. Confidentiality controls also speak directly to how you handle protected health information before it reaches HIPAA-specific requirements. Including all five criteria in your SOC 2 scope signals a mature security program and removes friction from procurement conversations before they stall.
Why SOC 2 audits matter
Understanding the full soc 2 audit definition only takes you so far. What actually drives organizations to pursue one is the business pressure behind it. Enterprise customers and health systems run their own vendor risk programs, and a SOC 2 report is one of the first documents they request. Without it, your sales team will hit the same wall at the same point in every procurement conversation, regardless of how good your product is.
SOC 2 builds trust with enterprise buyers
Your customers cannot audit every vendor themselves. They rely on independent SOC 2 reports to confirm that your security controls have survived external scrutiny. When you hand over a clean Type II report, you remove a significant blocker from the deal cycle. The buyer doesn't need to send a detailed security questionnaire, schedule a technical review, or wait for legal to weigh in on every control gap. Your report answers those questions before they ask them.
A SOC 2 report is not just a compliance document; it's a sales asset that compresses enterprise procurement timelines.
Buyers who receive a SOC 2 report from you also gain confidence that your organization takes ongoing security seriously, not just at the moment of sale. That distinction matters in long-term vendor relationships, where a single breach can end a contract and damage your reputation across an entire market segment.
SOC 2 opens doors in regulated industries
Healthcare is one of the most security-conscious procurement environments in any industry. Health systems use vendor risk management frameworks that treat security documentation as a prerequisite, not a nice-to-have. If you're building an integration with an EHR system like EPIC, the security team at a prospective health system will ask for your SOC 2 report before your product ever reaches a clinical stakeholder. Arriving without one signals that your organization is not ready for enterprise-grade deployments.
Beyond healthcare, SOC 2 compliance also accelerates deals in financial services, legal technology, and any sector where data sensitivity drives procurement decisions. The organizations that require SOC 2 reports are typically the ones with the largest contracts and the longest customer lifetimes. Pursuing compliance early means your sales team can compete for those contracts instead of watching them go to vendors who already cleared the security bar. Skipping the audit to save time in year one often costs far more in missed revenue across the following years.
SOC 2 Type I vs Type II
When you dig into the full soc 2 audit definition, one distinction surfaces quickly: there are two report types, and they answer different questions. A Type I report tells your customers that your controls were suitably designed at a specific point in time. A Type II report tells them your controls actually operated effectively over a defined period, typically six to twelve months. The difference matters because enterprise buyers and health systems weigh these two reports very differently when evaluating a vendor.
Type I: Design at a Point in Time
A Type I audit examines whether your controls are suitably designed to meet the relevant Trust Services Criteria on the date the auditor reviews them. Your auditor looks at your policies, documented procedures, and system configurations and determines whether those controls could reasonably prevent the risks they target. No operating history is required, which makes Type I the faster path for organizations building a formal compliance program for the first time.
Type I reports give buyers a starting point, but most enterprise customers treat them as preliminary evidence rather than full assurance. They confirm your controls exist and are properly designed. They do not confirm your team actually followed those controls consistently over time. For that level of assurance, customers ask for a Type II report.
A Type I report is a useful first step, but a Type II report is what most health systems require before approving a vendor for clinical integration.
Type II: Operating Effectiveness Over Time
A Type II audit covers a defined observation period, most commonly six to twelve months. Your auditor tests whether your controls operated consistently and effectively throughout that window by reviewing control evidence from multiple points in time, not just a single snapshot. The resulting report gives buyers far stronger confidence that your security program is real and repeatable, not just well-documented on the day of the audit.
For healthcare vendors, a Type II report is typically the minimum standard health systems expect before granting access to their clinical environment. The observation period creates an audit trail that security and procurement teams can evaluate with confidence, which directly shortens the vendor approval process.
Which Type to Pursue First
Your choice depends on where you are in your compliance maturity. If you're building your first formal security program, a Type I report establishes a baseline and surfaces gaps before you commit to a full observation period. Most organizations then move into a Type II engagement within twelve months to satisfy enterprise customers. Starting with Type I and transitioning directly into Type II surveillance is the most efficient path for healthcare vendors trying to reduce friction in procurement cycles.
How to prepare for and run a SOC 2 audit
Preparing for a SOC 2 audit is less about scrambling before an auditor shows up and more about building a security program that runs consistently every day. The full soc 2 audit definition includes ongoing operational discipline, not just documented policies. Your goal before the audit begins is to close the gap between what your written controls say and what your team actually does.
Define your scope and select your criteria
Your first decision is scope. You need to determine which systems, services, and data flows fall inside your audit boundary. Auditors examine only what falls within scope, so defining it too narrowly leaves gaps that enterprise customers will catch later, and defining it too broadly adds unnecessary cost and preparation work. For healthcare vendors, include any system that touches patient data or connects to a health system network, even if the connection is indirect.
After setting scope, select the Trust Services Criteria your audit will cover. Most healthcare vendors include all five criteria because health system procurement teams expect it. Review your customer contracts and prior security questionnaires to confirm which criteria matter most to your buyers before finalizing your selection.
Build and document your controls
Once you know your scope and criteria, map each criterion to specific controls your organization will implement. Controls cover areas like access management, encryption, logging, incident response, and vendor management. Each control needs a written policy, a designated owner, and a process for generating evidence on a regular schedule. Undocumented controls do not exist from an auditor's perspective, regardless of how well your team executes them.
Start building your evidence library at least six months before your target audit window if you plan to pursue a Type II report.
Vendor management is one area many teams overlook during initial control mapping. If your vendors handle customer data on your behalf, you need to confirm they hold their own security certifications or agree to your security requirements in writing. Auditors will request evidence of your third-party risk management process, and gaps here frequently surface as findings in the final report.
Gather evidence and work with your auditor
The active audit phase requires your team to pull evidence for each control across the observation period. This includes access review logs, change management tickets, security training records, and incident response documentation. Your auditor will request samples and test whether the evidence matches your stated procedures.
Working closely with your auditor throughout the process saves time and reduces surprises. A qualified auditor will flag potential gaps early and give your team the chance to remediate before those gaps appear as formal findings in the final report. Treat the audit as a collaborative review rather than an inspection, and your first report will reflect a stronger result.
What to do next
Working through the soc 2 audit definition gives you a foundation, but the real work starts when you map these requirements to your actual systems and customer commitments. Start by reviewing your current controls against the five Trust Services Criteria, then identify which gaps carry the most risk in your next procurement conversation. Scope, evidence, and auditor selection are the three decisions that shape how quickly you reach a clean report.
For healthcare vendors building EPIC integrations, SOC 2 compliance is one piece of a larger technical picture. Your buyers expect HIPAA adherence, SMART on FHIR compliance, and a clean security record before they approve you for clinical deployment. If you're managing all of that alongside your core product, the overhead compounds fast. VectorCare handles SOC 2 compliance, HIPAA requirements, and EPIC integration infrastructure in a single managed platform. See how VectorCare accelerates your path to health system contracts and removes the security credibility barrier from your sales cycle.
The Future of Patient Logistics
Exploring the future of all things related to patient logistics, technology and how AI is going to re-shape the way we deliver care.