SOC 2 Audit Timeline: Typical Timelines From Prep to Report


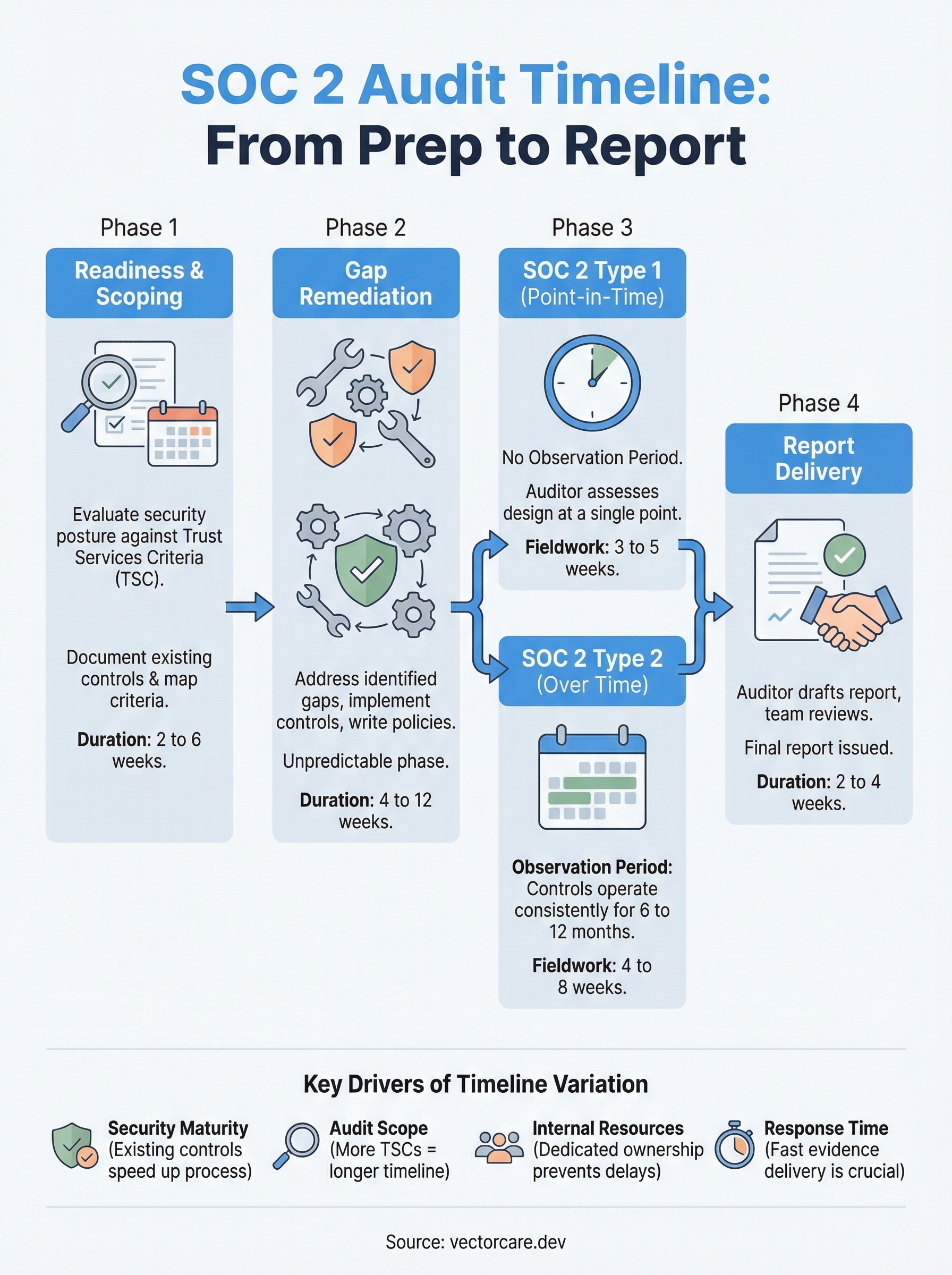
Most healthcare vendors hear "SOC 2 audit" and immediately think about the cost. But what catches teams off guard more often is the time. The full SOC 2 audit timeline, from initial scoping to holding a finished report, typically runs anywhere from 6 to 18 months, depending on your starting point, the type of report you're pursuing, and how many gaps need fixing along the way.
For vendors building integrations with EPIC EHR systems, SOC 2 compliance isn't optional. Health systems expect it. Procurement teams ask for it. And without a current report, your deal cycle stalls, or dies entirely. That's a problem when you're already juggling FHIR development, HIPAA requirements, and App Orchard submissions. At VectorCare, we handle SOC 2 and HIPAA compliance as part of our managed SMART on FHIR platform specifically so vendors don't lose months to infrastructure and audit prep before they can even compete for contracts.
But whether you're going through the process independently or leaning on a compliant platform, understanding what each phase actually involves, and how long it takes, helps you plan realistically. This article breaks down the SOC 2 audit timeline stage by stage: readiness assessment, gap remediation, the observation window, the audit itself, and final report delivery. You'll walk away with concrete timeframes and the context to set expectations with your team, your auditor, and the health systems waiting on your compliance documentation.
What a SOC 2 audit timeline includes
A SOC 2 audit isn't a single event you schedule and show up to. It's a multi-phase process that starts months before your auditor reviews a single control, and it ends only when your CPA firm delivers the final report. Understanding each phase is how you stop treating compliance as a surprise sprint and start treating it as a planned business activity. Each phase feeds directly into the next, which means delays in early stages compound across the full SOC 2 audit timeline.

The full SOC 2 audit timeline is built on distinct, sequential phases, and rushing any one of them tends to extend the total process, not shorten it.
Phase 1: Readiness Assessment and Scoping
The process begins with a readiness assessment, where you evaluate your current security posture against the SOC 2 Trust Services Criteria (TSC) defined by the American Institute of Certified Public Accountants (AICPA). At minimum, every SOC 2 audit covers the Security (Common Criteria) category. Depending on your customer commitments, you may also need to address Availability, Confidentiality, Processing Integrity, or Privacy criteria. The scoping decisions you make here drive the scope of every phase that follows.
During the assessment, your team documents existing controls, identifies which systems and processes fall inside the audit boundary, and maps which criteria you currently meet. This phase typically takes two to six weeks for organizations with basic documentation already in place. Teams starting from scratch with no formal policies often spend closer to eight weeks on readiness before they can move forward.
Phase 2: Gap Remediation
Once you know where your gaps are, you close them before an auditor ever reviews your controls. Remediation is consistently the most unpredictable part of the process. Common gaps include missing access control policies, absent vulnerability management procedures, weak vendor risk documentation, and incomplete audit logging, all of which take time to properly address.
Closing those gaps isn't just about writing policy documents. You need to implement the controls, run them long enough to produce usable evidence, and verify that evidence will hold up under auditor scrutiny. For most organizations, remediation runs between one and four months. If your organization has significant infrastructure gaps or needs to deploy new security tooling, budget toward the longer end of that range.
Phase 3: Observation Period and Audit Fieldwork
For a SOC 2 Type 2 report, your controls must operate effectively over a defined observation period of at least six months, though twelve months is common. During this window, controls need to function consistently and generate evidence at the frequency your auditor expects. For a SOC 2 Type 1, there is no observation period; the auditor assesses controls at a single point in time, which significantly shortens the overall process.
Fieldwork begins once the observation window closes. Your auditor requests evidence samples, interviews team members, and tests controls against the relevant Trust Services Criteria. Fieldwork for most mid-sized organizations runs four to eight weeks, depending on your audit scope and how quickly your internal team responds to evidence requests.
Phase 4: Report Delivery
After fieldwork wraps, your auditor drafts the report and your team reviews a preliminary version before the final document is issued. Report drafting and review typically takes two to four weeks. The finished SOC 2 report is the artifact you hand to health systems, procurement teams, and enterprise customers as documented proof of your security posture.
Most SOC 2 reports remain relevant and credible for twelve months after the report date, at which point health systems and partners typically expect a new report covering a more recent period. Planning your next audit cycle before the current report expires keeps you from re-entering a gap period where you can't satisfy compliance requests.
Why SOC 2 timelines vary so much
The 6 to 18 month range cited for a typical SOC 2 audit timeline isn't arbitrary. It reflects genuine variation driven by real differences in starting conditions, report type, audit scope, and internal capacity. Two organizations in the same industry, pursuing the same report type, can finish months apart simply because of how prepared they were on day one. Understanding what drives that spread helps you build a realistic schedule rather than an optimistic one that falls apart in the middle of remediation.
The single biggest driver of timeline variation isn't your auditor's schedule. It's how much documented evidence your organization already has before the process starts.
Your current security maturity level
Organizations with mature, documented security programs move through readiness and remediation significantly faster than those building controls from scratch. If you already have formal access control policies, patch management procedures, and incident response documentation in place, your gap remediation phase might take four to six weeks. Starting without those foundational controls means budgeting two to four months for remediation before your observation period can even begin, and that delay pushes every subsequent phase further out.
Your existing tooling also matters. Teams that already use endpoint monitoring, log aggregation, and vulnerability scanning generate audit evidence automatically as a byproduct of normal operations. Teams that need to research, procure, and deploy those tools first add weeks to the process before they can even demonstrate consistent control operation to an auditor.
Audit scope and Trust Services Criteria selected
Choosing additional Trust Services Criteria beyond the Security category extends your timeline. Adding Availability, Confidentiality, or Privacy criteria means more controls to implement, more gaps to close, and more evidence to collect during your observation window. Most organizations pursuing SOC 2 for the first time limit scope to Security to reduce initial complexity and get a usable report in hand faster, then expand scope in subsequent audit cycles.
The complexity of your technical environment compounds this effect. Organizations with dozens of integrated systems and multiple cloud environments present a larger audit surface, which means more controls to document, test, and prove.
Internal resource availability
Dedicated compliance ownership shortens timelines considerably. When a specific person or small team drives the process full-time, evidence collection stays on schedule and auditor requests get answered within days. When compliance tasks compete with product development and customer work, response times slow, evidence collection falls behind, and your auditor waits. Most mid-sized vendors find that slow internal responses alone add four to eight weeks to the total process.
SOC 2 Type 1 timeline from prep to report
A SOC 2 Type 1 report covers your security controls at a single point in time. Your auditor evaluates whether your controls are designed appropriately on the day of assessment, not whether they operated consistently over months. That distinction removes the observation period from the equation entirely, which compresses the overall SOC 2 audit timeline for a Type 1 significantly compared to a Type 2. Most organizations complete the full process in three to six months, though your specific timeline depends on how much remediation work sits between your current state and audit-ready.
A Type 1 report is the fastest path to a credible SOC 2 report, which makes it the right starting point for most first-time vendors.
What drives the Type 1 timeline
The largest variable in a Type 1 process is how much remediation your readiness assessment surfaces. If your security posture is already documented and your core controls are in place, remediation might take four to six weeks. If you're building policies and implementing security tooling from scratch, expect eight to twelve weeks before your controls are strong enough to survive auditor scrutiny. Your auditor isn't reviewing evidence collected over time, but your controls still need to exist, be documented, and be demonstrably operational on assessment day.
Internal staffing also shapes how quickly you move. Dedicated ownership of the compliance workload keeps evidence collection and policy documentation on schedule. When compliance tasks share attention with product and customer priorities, the readiness phase stretches and pushes your audit date further out.
Phase-by-phase breakdown for Type 1
Each phase has a predictable range, and knowing those ranges helps you build a schedule your team can actually hit.
| Phase | Typical Duration |
|---|---|
| Readiness assessment and scoping | 2 to 6 weeks |
| Gap remediation | 4 to 12 weeks |
| Auditor fieldwork | 3 to 5 weeks |
| Report drafting and review | 2 to 4 weeks |
What to expect during fieldwork
Your auditor will request policy documents, system configuration screenshots, and access control records relevant to the Trust Services Criteria in your scope. For a Type 1, the evidence set is narrower than a Type 2 because there's no historical sample to pull. Responding to evidence requests within 48 hours keeps fieldwork on track and prevents the four to six week fieldwork window from quietly expanding while your auditor waits.
SOC 2 Type 2 timeline and observation period
A SOC 2 Type 2 report takes significantly longer than a Type 1 because it requires your controls to operate consistently over time, not just exist on a single day. The full SOC 2 audit timeline for a Type 2 typically runs 9 to 18 months, from initial readiness work through final report delivery. That range reflects the mandatory observation window layered on top of everything a Type 1 requires, and it's why vendors who start the process late often find themselves unable to satisfy health system contract requirements on their preferred timeline.
Most health systems that ask for SOC 2 documentation specifically want a Type 2 report, making it the standard your vendor business eventually needs to meet.
The observation period explained
The observation period is the stretch of time your auditor reviews when assessing whether your controls operated effectively. AICPA standards set the minimum observation period at six months, but most organizations run a twelve-month window because it signals a more mature, stable security program to customers and procurement teams. During this window, your controls need to run consistently and produce evidence at the frequency you've committed to, whether that's daily, weekly, or monthly.

Starting the observation period requires your controls to already be implemented and your policies to be finalized. Any control you add or significantly modify mid-period resets the clock for that specific control. That's why completing remediation before the window opens matters more in a Type 2 process than in a Type 1, and why rushing into the observation phase before remediation is complete tends to cost more time than it saves.
Phase-by-phase breakdown for Type 2
Each phase carries a predictable range, and the observation period is where most of your total timeline sits.
| Phase | Typical Duration |
|---|---|
| Readiness assessment and scoping | 2 to 6 weeks |
| Gap remediation | 4 to 12 weeks |
| Observation period | 6 to 12 months |
| Auditor fieldwork | 4 to 8 weeks |
| Report drafting and review | 2 to 4 weeks |
Choosing your observation period length
Your observation period length is a deliberate decision, not a default. A six-month window gets you a usable report faster, but many enterprise health systems and large hospital networks treat a twelve-month report as the more credible benchmark. If you're pursuing contracts with large IDNs or academic medical centers, starting with a twelve-month observation window positions your report to hold up under more rigorous procurement scrutiny from day one.
How to build a realistic SOC 2 project plan
Building a project plan that actually holds up requires working backward from a fixed deadline, not forward from a hopeful start date. Most vendors get into trouble by picking an audit date first and then discovering mid-process that they underestimated remediation time. Before you schedule anything with an auditor, map out your full SOC 2 audit timeline using the phase durations covered above, add buffer for the phases most likely to slip, and then set your target report date based on what the math actually supports.
A project plan built backward from a deadline forces you to confront resource gaps early, when you still have time to address them.
Start with your target report date
Your target report date is usually driven by an external forcing function, a contract requirement from a health system, a procurement deadline, or a partnership that requires a current SOC 2 report. Work backward from that date through each phase: report review, fieldwork, observation period (if you're pursuing Type 2), remediation, and readiness assessment. If the math puts your readiness assessment start date in the past, your target date is not realistic and you need to either renegotiate the deadline or scope down to a Type 1 report to compress the timeline.

Build in explicit buffer at the remediation and fieldwork phases specifically. Both phases consistently run longer than initial estimates suggest, and padding them by two to three weeks per phase protects your report date without requiring heroics from your team.
Assign clear ownership for each phase
A project plan without named owners is a wishlist. Every phase needs a single accountable person responsible for driving it to completion, collecting evidence, and responding to requests. That person doesn't need to do all the work themselves, but they need to own the outcome.
Document the following for each phase in a shared project tracker:
- Owner name and backup contact if the primary owner is unavailable
- Start date and deadline for the phase
- Key deliverables required before the phase closes
- Auditor or external dependencies that could create wait time
Keeping this tracker visible to your leadership team creates accountability and surfaces scheduling conflicts before they delay your report date. Update it weekly during active phases so small delays get addressed before they compound into larger ones.
Common delays and how to avoid them
Most SOC 2 audit timeline overruns don't come from auditor problems or external surprises. They come from predictable internal bottlenecks that were visible weeks earlier but never addressed. Recognizing the patterns that reliably slow down compliance programs lets you intervene before a two-week slip quietly becomes a two-month one.
The delays that kill SOC 2 timelines are almost always internal, not external.
Incomplete or inconsistent policy documentation
Missing policy documentation is one of the most consistent reasons audits stall. Auditors expect policies to exist, be current, and map directly to the controls you're claiming. Teams often draft policies during readiness, then fail to get them formally approved and distributed before fieldwork begins. When fieldwork arrives and your auditor requests policy evidence, you're back in documentation mode during a phase that's supposed to be about demonstrating operational controls.
Fix this by treating policy approval as a hard milestone, not a background task. Assign a completion date during your project plan, get formal sign-off from the right stakeholders, and confirm that policies are distributed and accessible before you open your observation window.
Slow responses to evidence requests
Auditor evidence requests during fieldwork have a way of arriving all at once, and slow response times extend fieldwork considerably. If your internal team takes a week to respond to each request, a four-week fieldwork window stretches to six or seven weeks with no additional work actually happening.
Assign a single point of contact responsible for managing all auditor communication during fieldwork. That person should acknowledge each request within 24 hours, even if the full evidence package takes longer to assemble. This alone keeps fieldwork on track and prevents your auditor's schedule from moving to other clients while they wait for you.
Scope changes after the observation period starts
Modifying or adding controls mid-observation resets the clock for the affected controls. Teams sometimes discover during the observation period that a control isn't generating consistent evidence, then adjust the control rather than address the evidence collection process. The adjustment looks like a fix but creates a documentation problem that your auditor will flag.
Conduct a control-by-control readiness check before your observation period opens. Confirm each control is generating evidence at the right frequency and that the evidence is retrievable. Catching gaps before the window starts is far less disruptive than addressing them after it's already running.
SOC 2 timeline FAQs and quick benchmarks
The questions below come up in nearly every compliance conversation, and the answers tend to surprise vendors who assumed the SOC 2 audit timeline was more predictable than it actually is. Use these benchmarks as calibration points, not guarantees, since your actual timeline depends on your starting state.
The fastest timeline is only achievable if your policies, tooling, and internal ownership are already in place before you engage an auditor.
How long does a first-time SOC 2 audit take?
First-time SOC 2 audits take longer than renewals because you're building controls and documentation from scratch rather than maintaining existing ones. For a Type 1, most first-time organizations land between four and seven months from readiness assessment start to report delivery. For a Type 2, budget nine to fifteen months when you factor in the observation period on top of remediation. Organizations with a designated compliance owner and existing security tooling consistently finish toward the shorter end of those ranges.
What is the minimum time needed to get a SOC 2 report?
A Type 1 report is the fastest path. If your security controls are already implemented, your policies are documented, and your team responds quickly to auditor requests, completing a Type 1 in ten to twelve weeks is achievable. That said, most organizations need at least four to six weeks of remediation before controls are audit-ready, which pushes the realistic minimum closer to three to four months total. For a Type 2, the six-month minimum observation period makes anything under eight months extremely difficult regardless of how prepared you are at the start.
Quick SOC 2 timeline benchmarks by scenario
These benchmarks give you a practical starting point for planning conversations with your auditor and your leadership team.
| Scenario | Estimated Total Timeline |
|---|---|
| Type 1, mature security program | 3 to 4 months |
| Type 1, building controls from scratch | 5 to 7 months |
| Type 2, six-month observation, prepared org | 9 to 12 months |
| Type 2, twelve-month observation, prepared org | 14 to 18 months |
| Type 2, twelve-month observation, starting from scratch | 16 to 20 months |
How often do you need to renew your SOC 2 report?
Most health systems and enterprise customers expect a current report covering the previous twelve months. That means your next audit cycle should start before your current report expires, not after. Building a continuous compliance program, where evidence collection runs year-round, removes the crunch that comes with treating SOC 2 as a one-time project.
Plan your next SOC 2 audit
The soc 2 audit timeline is longer than most vendors expect, and starting late is the most common reason compliance becomes a contract blocker rather than a competitive advantage. Every phase covered in this article, from readiness assessment through final report delivery, has a predictable duration. Use those ranges to build your project plan, assign clear ownership, and lock in your target report date before your next health system conversation.
For vendors integrating with EPIC EHR systems, SOC 2 compliance sits alongside HIPAA and SMART on FHIR requirements as table stakes for closing contracts. Handling all three simultaneously strains most vendor teams. VectorCare's managed platform includes SOC 2 and HIPAA compliance built in, so your team focuses on your core product instead of infrastructure and audit prep. If that approach fits your situation, explore how VectorCare handles compliance for EPIC integrations before your next procurement deadline arrives.
The Future of Patient Logistics
Exploring the future of all things related to patient logistics, technology and how AI is going to re-shape the way we deliver care.