Consent Lifecycle Management: Stages, Best Practices, Tools


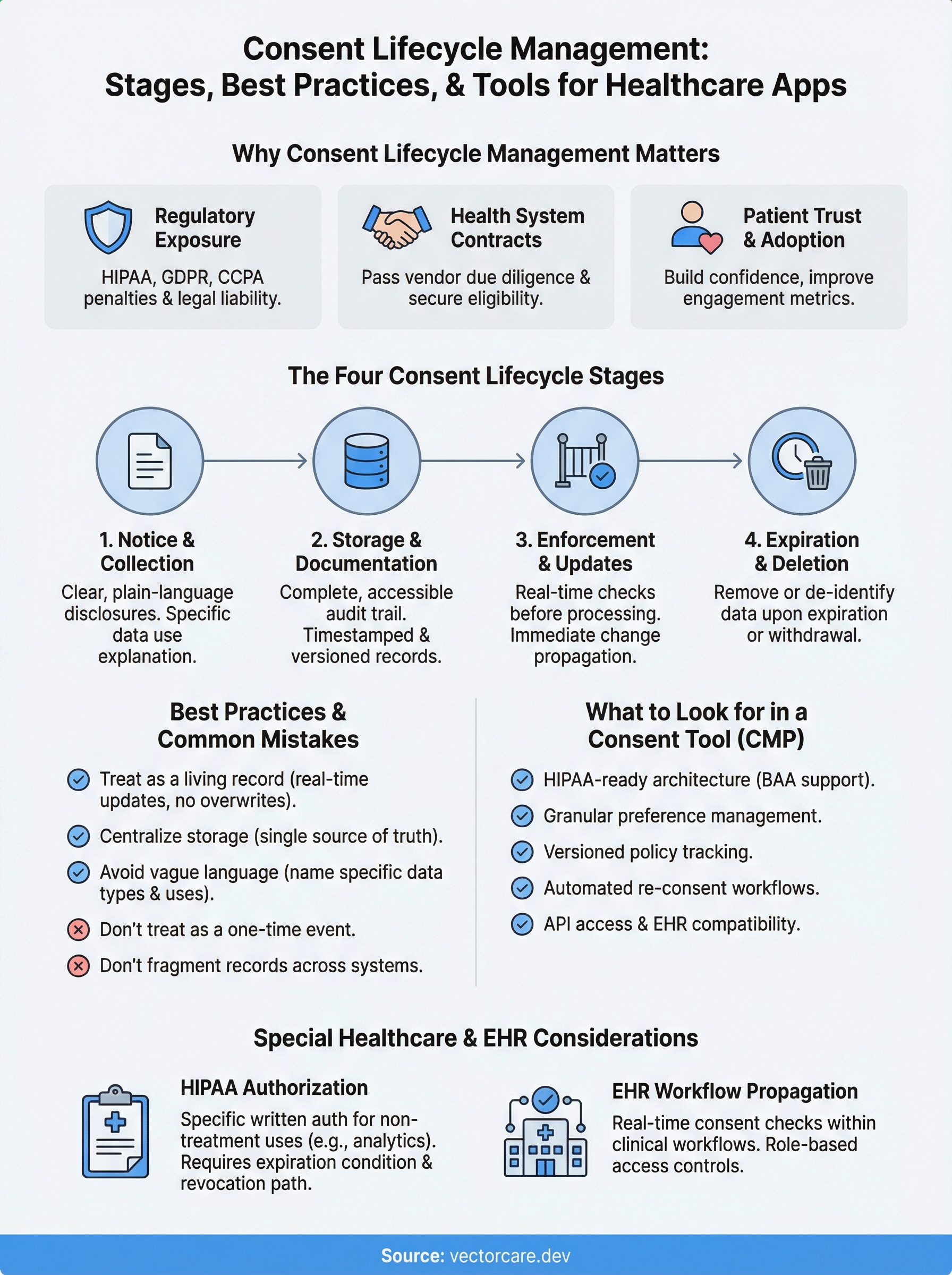
Every time a patient shares health data through an EHR-integrated application, consent is involved. Collecting that consent is only the starting point. Consent lifecycle management covers every stage from initial collection through storage, enforcement, updates, and eventual expiration, and getting any of those stages wrong puts healthcare vendors at risk of regulatory violations under HIPAA, GDPR, and CCPA.
For healthcare vendors building integrations with EPIC and other EHR systems, consent isn't a checkbox exercise. It's an ongoing operational responsibility tied directly to patient trust and contract eligibility with health systems. The more clinical workflows your application touches, the more consent scenarios you need to track, across providers, data types, and jurisdictions. Managing this manually or through disconnected tools creates gaps that auditors and health systems will find.
This article breaks down the full consent lifecycle into its core stages, walks through best practices for each, and covers the tools (including consent management platforms) that can automate the heavy lifting. Whether you're preparing for your first EPIC integration or tightening compliance across existing deployments, you'll leave with a practical framework you can act on. At VectorCare, we build no-code SMART on FHIR applications for healthcare vendors integrating with EPIC, and compliance infrastructure like consent management is a critical part of what makes those integrations production-ready.
Why consent lifecycle management matters
Consent is not a one-time event tied to a signup form or a PDF disclosure. It's a continuous process that touches every data transaction your application performs. Consent lifecycle management gives your organization a structured way to track where every piece of consent came from, what it covers, when it expires, and whether it's been updated, so you can demonstrate compliance to regulators and health systems at any point in time without scrambling through disconnected records.
Regulatory exposure is real and costly
HIPAA, GDPR, and CCPA all impose specific obligations around how you collect, document, and honor patient and user consent. Under HIPAA, you need a signed authorization before using protected health information (PHI) for purposes outside treatment, payment, or healthcare operations. Under GDPR, you must prove that consent was freely given, specific, informed, and unambiguous, and you must honor withdrawal requests without undue delay. CCPA adds opt-out rights for data selling and requires that you retain consent records for at least 24 months.
Failing to document consent at any stage, not just at collection, can result in HIPAA penalties up to $1.9 million per violation category per year.
Getting any single stage wrong, whether it's missing a re-consent trigger after a policy update or failing to propagate a withdrawal across all downstream systems, creates direct legal liability. Regulators don't accept "we didn't know" as a defense, and health systems conducting vendor due diligence certainly won't either.
Health systems evaluate your consent posture before signing contracts
When a hospital or health network evaluates your application for deployment, their security and compliance teams will ask specific questions about how you handle patient data consent. They want to see that your application can enforce consent at the data level, generate audit trails, and respond to patient requests within required timeframes. Without structured processes to answer those questions confidently, you lose contracts to vendors who can.
EPIC-integrated applications face an additional layer of scrutiny because they operate inside clinical workflows and directly touch PHI. Health systems take on shared liability when they deploy your app, which means your consent infrastructure becomes their risk exposure. A weak answer during vendor review is often enough to end the conversation entirely, regardless of how strong your core product is.
Patient trust has direct business consequences
Patients increasingly understand their rights around health data. A poorly handled consent request, one that's vague, buried in legal text, or never revisited after changes, signals to patients that your organization treats their data as a formality rather than a responsibility. That perception affects adoption rates directly, which in turn affects the metrics health systems use to evaluate whether your application is worth keeping deployed after the initial contract term.
Strong consent practices, communicated clearly and enforced consistently, build the kind of patient confidence that translates into higher engagement and better clinical outcomes. Health systems notice that pattern. When your application demonstrates that patients trust it enough to use it actively, you become easier to renew and easier for the health system to recommend to peer institutions through channels like the EPIC App Orchard.
The consent lifecycle stages, from notice to deletion
Understanding the full sequence of consent lifecycle management helps you identify where your current processes have gaps. Most vendors think about consent only at the point of collection, but the lifecycle spans four distinct stages, each with its own compliance requirements and operational risks.

Stage 1: Notice and collection
Before any data transaction occurs, you need to give users a clear, plain-language explanation of what you're collecting, why you're collecting it, and what rights they have over that data. For healthcare applications, this means disclosures that align with HIPAA authorization requirements and, where applicable, GDPR's conditions for lawful processing. Your notice must be specific enough that a patient understands exactly what they're agreeing to, not a generic catch-all that lumps every data use into a single checkbox.
Stage 2: Storage and documentation
Once a user gives consent, your system needs to capture and store a complete record of that event: what they agreed to, when they agreed to it, which version of your privacy policy was in effect, and through which channel consent was obtained. Without this structured audit trail, you cannot demonstrate compliance to a regulator or health system.
A consent record with no timestamp, no policy version, and no channel attribution is legally worthless if you ever need to prove what a patient agreed to.
That documentation needs to stay accessible and queryable, not buried in a log file. When a health system asks you to produce consent records for a specific patient during a compliance review, you need to surface that data within the required response window, not spend days reconstructing it manually.
Stage 3: Enforcement and updates
Storing consent means nothing if your application doesn't actively enforce it at every data transaction. Your systems need to check consent status before processing or sharing any data, and they need to propagate changes immediately when a user updates or withdraws consent. Delays in propagation create direct regulatory exposure under GDPR's withdrawal requirements and HIPAA's minimum necessary standard.
When you update your privacy policy or change how you use data, you need a re-consent workflow that notifies affected users, captures their updated decision, and records the new consent event separately from the original.
Stage 4: Expiration and deletion
Consent doesn't last forever. Some records expire on a fixed schedule, and others become invalid when your stated data use purpose changes. When consent expires or is withdrawn, your deletion workflow needs to remove or de-identify the relevant data across every system that received it, including third-party integrations and analytics pipelines you may have overlooked during initial setup.
Best practices and common mistakes to avoid
Solid consent lifecycle management doesn't happen automatically. It requires deliberate decisions at every stage about how you collect, store, enforce, and retire consent. Most compliance failures aren't caused by vendors ignoring the rules entirely. They come from gaps between process design and actual execution, particularly when consent records live in multiple systems or when re-consent workflows never trigger the way they were designed to.
Treat consent as a living record, not a one-time event
The most common mistake is treating consent as something you collect once and file away. Your consent records need to update in real time as patients withdraw, modify, or renew their authorizations. Every change should generate a new timestamped event in your audit trail, linked to the specific policy version in effect at the time of that change. If your system overwrites the original consent record when a patient makes an update, you lose the legal evidence you need to reconstruct the full consent history during a compliance review.
An audit trail that shows only the most recent consent record cannot prove what a patient agreed to at the time you first processed their data.
Centralize consent storage from the start
Vendors frequently spread consent records across multiple systems: one for their core application, another for their analytics pipeline, and a third for third-party integrations. That fragmentation makes it nearly impossible to respond to deletion or access requests within required regulatory timeframes. You need a single source of truth for consent status that every component of your system reads from before processing any data. When a patient withdraws consent, one update in that central record should propagate automatically to every downstream system without manual intervention across separate databases.
Building centralized consent storage from day one is significantly cheaper than retrofitting it later. Once your application is live and multiple health systems depend on it, untangling a fragmented consent architecture becomes a major engineering effort that can delay contract renewals and trigger compliance reviews you weren't prepared for.
Avoid vague language in your notices
Your consent notices need to name specific data types and use cases rather than relying on broad phrases like "we may use your information to improve our services." Patients and regulators scrutinize that language during disputes, and vague disclosures rarely hold up as evidence of informed consent. Write your notices at a clear reading level and explicitly state which data your application accesses. At minimum, your notices should address:
- Which EHR data fields your application reads or writes
- Whether any data leaves your system for third-party processing
- How long you retain that data and under what conditions you delete it
- What rights patients have and how to exercise them
Tools that automate consent and preference management
Managing consent lifecycle management manually across multiple health systems, data types, and regulatory frameworks is not realistic at scale. The right tools handle the repetitive enforcement work automatically, so your team can focus on building product instead of auditing spreadsheets. Most vendors fall into one of two categories: consent management platforms (CMPs) built for broad data privacy use cases, and more specialized tools designed for healthcare-specific regulatory environments.
Consent management platforms
CMPs are software solutions that centralize consent collection, storage, enforcement, and reporting into a single system. Platforms like OneTrust, Usercentrics, and TrustArc handle the core technical requirements: presenting compliant consent banners, capturing granular preference records, issuing re-consent workflows when policies change, and generating audit reports on demand.
A CMP that integrates directly with your data pipeline catches consent violations before they happen, rather than surfacing them during a compliance review.
Most enterprise-grade CMPs also provide pre-built integrations with major analytics and marketing tools, which matters if your application routes data to third-party systems. When a patient withdraws consent, the CMP propagates that change to every connected system automatically, removing the manual coordination that typically creates propagation delays and compliance gaps.
What to look for in a consent tool
Not every CMP is built for the complexity of healthcare data environments. Before you commit to a platform, evaluate it against the following criteria:

- HIPAA-ready architecture: The tool must support BAA execution and store consent records in a HIPAA-compliant environment, not just general enterprise security standards.
- Granular preference management: Look for tools that let patients control consent at the data-type level, not just a single all-or-nothing toggle.
- Versioned policy tracking: Every consent record should link to the specific policy version active at the time of collection, so your audit trail holds up under regulatory scrutiny.
- Automated re-consent workflows: When you update your data practices, the tool should trigger targeted re-consent requests to affected users without manual intervention.
- API access and EHR compatibility: Your consent tool needs to communicate with your application in real time. If it cannot expose consent status via API, enforcing it at the data layer becomes a manual workaround rather than a technical guarantee.
Choosing a tool that checks all five criteria from the start saves you a significant retrofit effort later, particularly once multiple health systems depend on your application running without compliance interruptions.
Special considerations for healthcare and EHR apps
Healthcare applications that integrate with EHR systems like EPIC operate in a fundamentally different regulatory environment than standard SaaS products. General consent lifecycle management principles apply, but the clinical context adds layers of specificity around what consent must cover, how it must be documented, and how quickly your systems must respond when a patient updates or revokes their authorization status.
HIPAA authorization requirements go beyond standard consent
HIPAA draws a sharp line between routine treatment disclosures covered under your Notice of Privacy Practices and the specific written authorizations required for uses of PHI outside standard care operations. If your application accesses clinical data for purposes like remote patient monitoring, analytics, or care coordination, you need a separate signed authorization that names the specific data types, the stated purpose, and an expiration condition. A blanket acknowledgment on a signup screen does not satisfy this requirement, and health system legal teams will flag the gap during vendor review.
A HIPAA authorization missing any of the six required elements, such as a clear description of the information to be used or an explicit expiration date, is legally invalid and exposes your organization to enforcement action.
Your authorization forms also need to inform patients of their right to revoke at any time, and you must document exactly how revocation requests can be submitted and processed. Building that revocation workflow before your first health system deployment is significantly cheaper than retrofitting it after your application is live and multiple institutions depend on uninterrupted access to it. Every week you delay adds technical debt that compounds once your patient population scales.
Consent propagation inside EPIC workflows
When your application runs inside EPIC's clinical environment, consent changes cannot live only in your external database. Your integration must read updated consent status in real time before processing any FHIR data pull or write operation, not just at session start. A patient who revokes authorization mid-workflow should trigger an immediate stop on pending data transactions, not wait until the next scheduled synchronization cycle runs.
EPIC-integrated apps surface data to multiple provider roles, including physicians, nurses, care coordinators, and administrative staff, which means your consent enforcement logic must account for role-based access controls. A patient may authorize sharing specific clinical data with their care team but explicitly exclude billing personnel or third-party referral partners from that same access. Your application needs to enforce those distinctions programmatically at the data layer, not depend on individual providers to self-regulate what they access beyond the scope of what the patient actually authorized.
Key takeaways and next steps
Consent lifecycle management spans far more than a single signup form. Every stage, from notice and collection through enforcement, re-consent, and deletion, carries specific compliance obligations under HIPAA, GDPR, and CCPA that health systems will verify before they sign a vendor contract. Skipping any single stage doesn't just create legal risk; it actively costs you deals during vendor review.
Your path forward starts with three concrete steps: centralize consent records into a single source of truth, write plain-language notices that name specific data types and use cases, and select a CMP that supports HIPAA-ready architecture with real-time API enforcement. For applications running inside EPIC, extend that foundation to include role-based access controls and consent propagation across every FHIR data transaction your app performs.
If you're building or expanding an EPIC integration and need a platform that handles compliance infrastructure from day one, explore what VectorCare builds for healthcare vendors.
The Future of Patient Logistics
Exploring the future of all things related to patient logistics, technology and how AI is going to re-shape the way we deliver care.