AWS SOC 2 Report: How to Access and Use It for Compliance


AWS SOC 2 Report: How to Access and Use It for Compliance
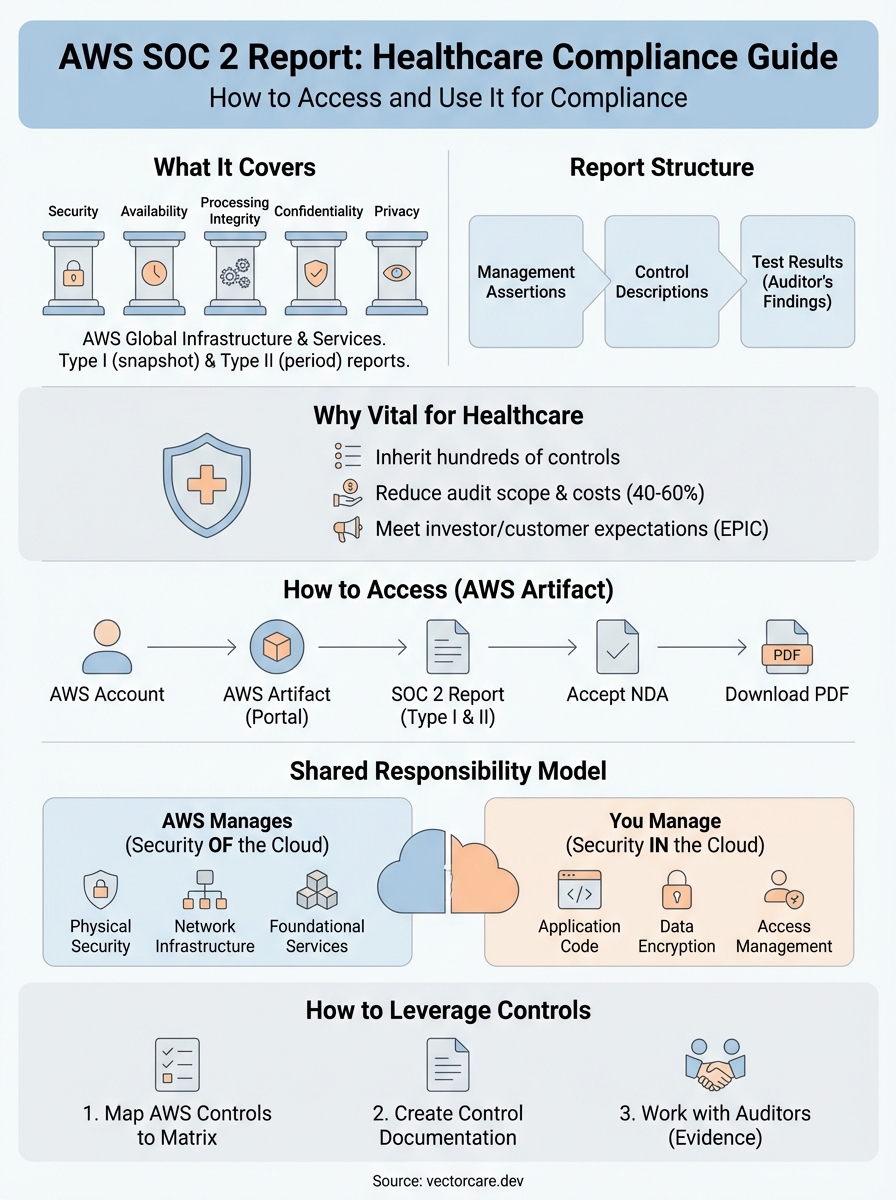
The aws soc 2 report is an official audit document that shows how Amazon Web Services meets security and compliance standards set by the American Institute of CPAs. It contains detailed evidence of AWS controls for security, availability, processing integrity, confidentiality, and privacy. Healthcare vendors need this report to prove their cloud infrastructure meets industry requirements and to satisfy auditors during their own SOC 2 assessments. The report gets updated regularly and covers AWS global infrastructure and services.
This guide shows you how to access the AWS SOC 2 report through AWS Artifact, what it covers, and how to use it for your compliance needs. You'll learn about the shared responsibility model, how AWS controls map to your audit requirements, and practical steps to leverage AWS compliance documentation for your own audits. If you build healthcare applications that integrate with electronic health records, understanding this report can streamline your compliance journey and reduce audit preparation time significantly.
What the AWS SOC 2 report covers
The aws soc 2 report examines AWS infrastructure and services against five trust service criteria defined by the American Institute of CPAs. AWS provides both Type I and Type II reports, with the Type II report covering a six-month examination period. You'll find detailed descriptions of AWS controls, testing procedures, and results that auditors performed across AWS data centers, network infrastructure, and cloud services. The report includes AWS global infrastructure spanning multiple regions and availability zones.
Trust service criteria explained
AWS organizes its SOC 2 report around security, availability, processing integrity, confidentiality, and privacy. Security controls cover network security, access management, encryption, and threat detection across all AWS services. Availability controls demonstrate how AWS maintains uptime commitments and disaster recovery capabilities through redundant systems and automated failover mechanisms. Processing integrity shows that AWS systems work as intended without errors or unauthorized modifications. Confidentiality controls prove AWS protects sensitive data through encryption at rest and in transit. Privacy controls demonstrate AWS compliance with data protection regulations and customer data handling requirements.

AWS includes over 300 controls in its SOC 2 report, far more than most organizations could build independently.
AWS services and regions included
The report covers core AWS services like EC2, S3, RDS, Lambda, and VPC along with supporting services for security, monitoring, and compliance. You get evidence for AWS global infrastructure including all commercial regions, edge locations, and availability zones. Amazon includes its shared infrastructure components such as data centers, power systems, cooling, network architecture, and physical security measures. The scope extends to AWS management tools like CloudTrail, Config, and CloudWatch that you use to monitor your own compliance posture.
Type I vs Type II differences
A Type I report provides a snapshot of AWS controls at a specific point in time, showing control design but not operating effectiveness. You'll see what controls AWS has in place and how they're supposed to function. Type II reports test those controls over six months, providing evidence that controls operated effectively throughout the examination period. Healthcare vendors typically need the Type II report because auditors want proof of sustained compliance, not just theoretical control design. AWS publishes updated Type II reports twice per year, giving you access to the most recent examination period for your audit needs.
Report organization and structure
AWS structures the report into management assertions, control descriptions, and test results that you can reference during your audit. Management assertions explain what AWS claims about its control environment. Control descriptions detail each security measure, its purpose, and how AWS implements it across infrastructure and services. Test results show the independent auditor's examination procedures and findings for each control tested. You can map these controls directly to your own SOC 2 requirements, reducing the work your auditors need to perform on infrastructure components you inherit from AWS.
Why this report is vital for healthcare vendors
Healthcare vendors face strict compliance requirements that go beyond standard software companies. You need to demonstrate security controls for patient data and prove your infrastructure meets HIPAA technical safeguards before health systems will sign contracts. The aws soc 2 report gives you documented evidence that your AWS infrastructure has been independently audited against industry standards. This documentation can cut your audit preparation time in half and reduce the compliance burden on your engineering team significantly.
Reducing your audit scope and costs
When your auditors examine your SOC 2 compliance, they need to verify every control in your technology stack. Using AWS infrastructure lets you inherit hundreds of pre-audited controls instead of building and documenting them yourself. You reference the AWS SOC 2 report to show that AWS handles infrastructure security, physical data center controls, network security, and disaster recovery. Your auditors can then focus on your application-level controls and business processes rather than questioning how you secure servers or manage data center access.
Healthcare vendors using AWS typically reduce their SOC 2 audit costs by 40-60% compared to managing their own infrastructure.
Organizations that build on AWS avoid duplicating control testing that AWS already performed. Your audit team spends less time and fewer billable hours examining infrastructure components. Instead of documenting how you manage physical security, power redundancy, and network architecture, you simply provide the AWS SOC 2 report as evidence for those inherited controls.
Meeting investor and customer expectations
Health systems require vendor security documentation before they sign contracts or grant access to their EPIC systems. You need to prove your platform meets their security standards and won't introduce vulnerabilities into their clinical workflows. Providing the AWS SOC 2 report alongside your own compliance documentation shows you built on trusted infrastructure that major healthcare organizations already rely on. Investors evaluating your company want to see that you've addressed compliance early and chosen infrastructure that scales with regulatory requirements rather than creating future technical debt.
How to access the report in AWS Artifact
AWS provides the aws soc 2 report through AWS Artifact, a self-service portal that gives you immediate access to compliance documentation. You need an AWS account to access the reports, but you don't need to run any infrastructure or pay for services to download compliance documents. AWS Artifact functions as your central repository for audit reports, certifications, and compliance documentation that you can share with your auditors and customers. The service includes both AWS-wide reports and agreements you can accept for your organization.
Creating your AWS account and accessing Artifact
You start by creating a standard AWS account at aws.amazon.com using your company email address. After you verify your email and complete the account setup process, you log into the AWS Management Console. Navigate to AWS Artifact by typing "Artifact" in the search bar at the top of the console or by selecting it from the Security, Identity, & Compliance services section. Your account needs administrator permissions to access and download reports, so ensure you're logged in with appropriate credentials or request access from your AWS account administrator.
Navigating to the SOC 2 report
Inside AWS Artifact, you'll see two main sections: Reports and Agreements. Click on Reports to view all available compliance documents organized by category and region. Use the filter options to select "SOC" under report types, which shows you both SOC 2 Type I and Type II reports for AWS services. Look for the most recent report date to ensure you're downloading the latest examination period. AWS updates these reports twice per year, typically in spring and fall, covering consecutive six-month periods.
AWS Artifact provides instant access to compliance reports that would normally require weeks of back-and-forth communication with vendors.
Accepting the NDA and downloading
Before you download any report, AWS requires you to accept a non-disclosure agreement that protects the confidential information in the compliance documents. Read the NDA terms, check the acceptance box, and submit your agreement. AWS processes your acceptance immediately, and you can then download the report as a PDF file. Save this file in your secure compliance documentation folder and restrict access to team members who need it for audit purposes.
Understanding the shared responsibility model
The aws soc 2 report demonstrates AWS infrastructure controls, but you remain responsible for securing your application and data. AWS divides compliance responsibilities between themselves and customers through a shared responsibility model that determines who handles which security controls. AWS manages security "of" the cloud while you manage security "in" the cloud. This division affects how you map AWS controls to your SOC 2 audit and which controls you need to implement independently.
What AWS manages for you
AWS handles physical infrastructure, network security, and foundational services that support your applications. They secure data centers with physical access controls, video surveillance, and environmental safeguards. AWS maintains hypervisor security, patch management, and hardware lifecycle across their global infrastructure. Network protection includes DDoS mitigation, firewall management, and traffic monitoring at the infrastructure level. You inherit these controls when you reference the AWS SOC 2 report during your audit, eliminating the need to document or test infrastructure-level security yourself.
AWS manages over 100 infrastructure controls that you can directly reference in your SOC 2 audit, saving months of documentation work.
What you control and must audit
Your responsibility covers application code, data encryption, access management, and user permissions within AWS services. You configure security groups, network ACLs, and IAM policies that control who accesses your resources and what actions they can perform. Data classification, backup procedures, and incident response processes fall entirely under your control. You also manage operating system patches for EC2 instances, database configurations for RDS, and API security for your applications. These customer-controlled areas require separate documentation and testing in your SOC 2 audit.
Where responsibilities overlap
Some controls require both AWS infrastructure and your configuration to work effectively. Encryption requires AWS to provide encryption capabilities while you decide which data to encrypt and manage encryption keys. Logging depends on AWS CloudTrail availability and your configuration of which events to capture and how long to retain them. Your auditors need to see that you properly configured AWS services and that you monitor the controls you own within the AWS environment.
How to leverage AWS controls for your own audit
You translate AWS infrastructure controls into your SOC 2 documentation by mapping AWS controls to your control objectives and referencing the aws soc 2 report as evidence. Your auditors accept AWS control testing as proof that infrastructure-level security works effectively, which means you focus your testing budget on application and business process controls. This approach requires you to understand which AWS controls satisfy your requirements and how to present that mapping in your control matrix.
Mapping AWS controls to your control matrix
Your control matrix lists every SOC 2 requirement and identifies the control owner and evidence source for each item. You designate AWS as the control owner for infrastructure components like physical security, network protection, and hardware management. Reference the specific AWS control number and page location from the SOC 2 report so your auditors can verify the mapping. For example, if your control matrix requires disaster recovery capabilities, you cite AWS controls for data replication across availability zones and automated backup systems. Your auditors review the AWS report to confirm those controls were tested and found effective.
Properly mapping AWS controls can eliminate 30-50% of the control testing work your auditors would otherwise perform.
Creating your control documentation
You build documentation that explains how your organization uses AWS services to satisfy control requirements. Write implementation guides that show which AWS features you enabled, how you configured security settings, and what monitoring you perform on inherited controls. Include screenshots of your IAM policies, CloudTrail configurations, and encryption settings as evidence that you properly implemented AWS security features. Your documentation should bridge the gap between AWS infrastructure controls and your specific implementation choices.
Working with your auditors
Share the AWS SOC 2 report with your audit team during the planning phase before fieldwork begins. Walk them through your control matrix to show which controls AWS handles and which you manage independently. Auditors familiar with cloud platforms understand the shared responsibility model, but you need to demonstrate your knowledge of AWS security features and how you configured them. Provide access to your AWS console or screenshots showing active security controls so auditors can verify your implementation matches your documentation.
Final thoughts on AWS compliance
The aws soc 2 report gives healthcare vendors a significant advantage when building compliant infrastructure for EPIC integrations. You access detailed evidence of AWS security controls through AWS Artifact, reference those controls in your own audit, and focus your compliance efforts on application-level security rather than infrastructure management. AWS handles physical security, network protection, and disaster recovery while you concentrate on building features that help health systems improve patient care.
Your path to SOC 2 compliance becomes faster and more cost-effective when you build on audited infrastructure. Healthcare vendors that leverage AWS controls typically complete their first SOC 2 audit in months rather than years. The shared responsibility model clarifies which security areas you own and which AWS manages, giving your auditors a clear framework for evaluating your compliance posture.
If you need to integrate with EPIC systems while maintaining HIPAA and SOC 2 compliance, VectorCare provides a managed platform that handles both the technical integration work and compliance requirements so you can focus on your core healthcare product.
The Future of Patient Logistics
Exploring the future of all things related to patient logistics, technology and how AI is going to re-shape the way we deliver care.