What Is Identity Federation? How It Works, Benefits, vs. SSO


What Is Identity Federation? How It Works, Benefits, vs. SSO
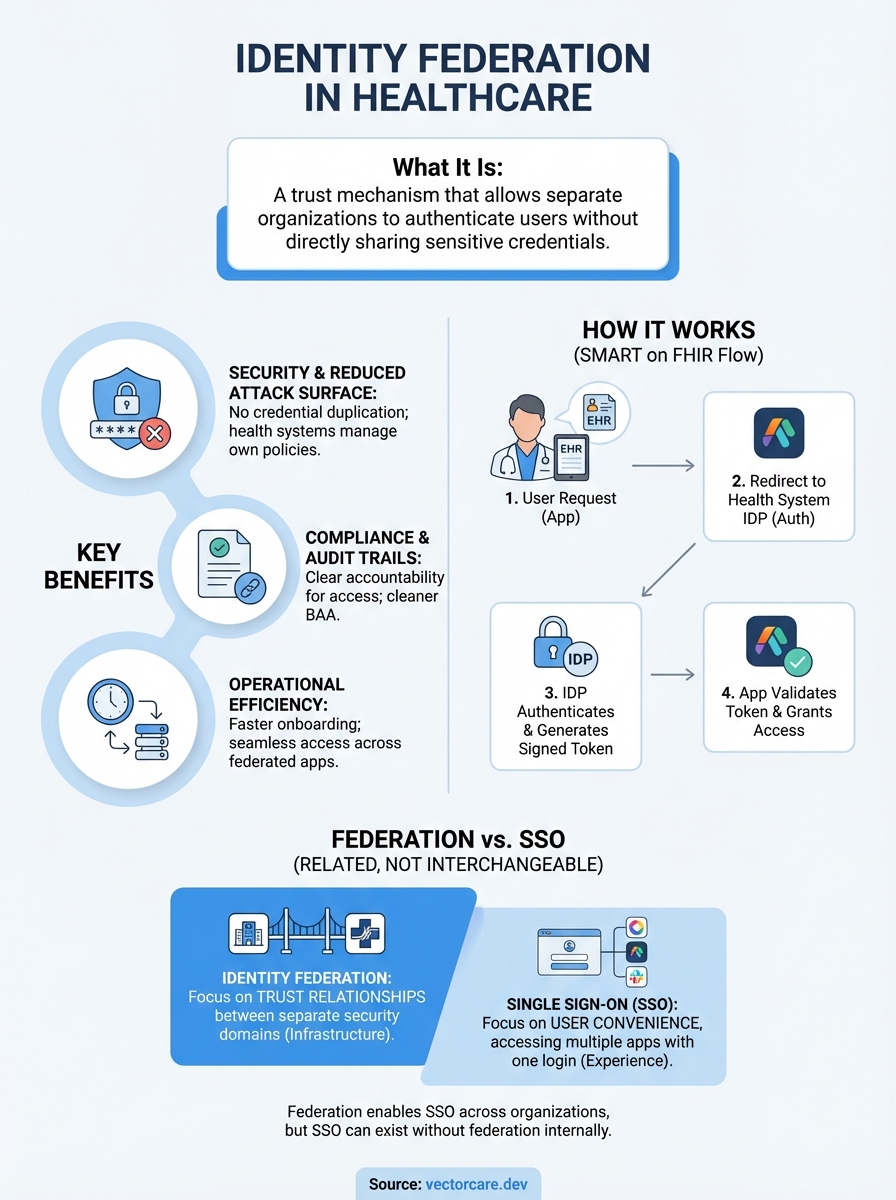
When a clinician logs into their hospital's EPIC system and seamlessly accesses a third-party clinical tool without entering another password, identity federation is doing the heavy lifting behind the scenes. It's the mechanism that allows separate organizations to trust each other's authentication without sharing sensitive credentials directly.
For healthcare vendors building SMART on FHIR applications, the kind VectorCare helps deploy into EPIC environments, understanding identity federation isn't optional. It's foundational to how your app will authenticate users across health systems, each with their own security domains and policies. Get it wrong, and you're looking at security gaps or failed integrations. Get it right, and clinicians experience the frictionless access they expect.
This article breaks down what identity federation actually means, the technical components that make it work, and the concrete benefits it delivers. We'll also clear up a common point of confusion: how identity federation differs from Single Sign-On (SSO), since the two are related but not interchangeable. By the end, you'll have a solid grasp of why federation matters for healthcare interoperability and secure EHR integration.
Why identity federation matters
You can't afford to pass credentials between systems in healthcare. When a clinician authenticates once through their health system's identity provider, identity federation allows your SMART on FHIR app to trust that authentication without ever seeing their password. This isn't just convenient, it's essential for maintaining security boundaries between separate organizations.
Security without credential sharing
Federation eliminates the riskiest part of traditional authentication: credential duplication. Instead of storing usernames and passwords for thousands of clinicians across hundreds of health systems, your application relies on the trust relationship established through federation protocols. The health system vouches for the user's identity, and your app accepts that voucher through cryptographically signed tokens.
This approach drastically reduces your attack surface. If your application never stores credentials, you can't leak them in a breach. The health system maintains full control over their users' authentication requirements, including password policies, multi-factor authentication, and account lifecycle management, without sharing that sensitive data with you.
"Identity federation transforms authentication from a liability you manage into a trust relationship you leverage."
Compliance and regulatory benefits
HIPAA and other healthcare regulations demand strict controls over access to protected health information. When you ask about what is identity federation in a compliance context, the answer centers on accountability and audit trails. Federation creates a clear record of which organization authenticated the user and when that authentication occurred.
Your Business Associate Agreement (BAA) becomes cleaner because you're not handling authentication credentials. The health system's identity governance policies automatically extend to your application through the federation relationship. When a clinician leaves, the health system revokes their access once, and your app immediately respects that change.
Operational efficiency for health systems
Health systems don't want to manage separate credentials for every vendor application their clinicians use. Federation means IT administrators provision access once in their central identity system, and it flows to all federated applications. This cuts onboarding time from days to minutes and eliminates the helpdesk burden of password resets across dozens of disconnected systems.
For vendors like those using VectorCare's platform, federation also accelerates deployment. You skip the complex work of building custom authentication integrations for each health system. The federation standards handle interoperability, letting you focus on your application's clinical value rather than reinventing identity management.
How identity federation works
Identity federation operates through a trust relationship between your application (the service provider) and the health system's authentication system (the identity provider). When a clinician attempts to access your SMART on FHIR app from within EPIC, your application redirects them to the health system's identity provider for authentication. Once verified, the identity provider sends back a cryptographically signed assertion that confirms the user's identity without ever exposing their credentials to your system.
The authentication flow
The process begins when your application detects an unauthenticated user attempting access. Instead of presenting a login form, your app redirects the user's browser to the health system's identity provider with a specific authentication request. This request includes details like which application is asking and what permissions it needs.

The identity provider authenticates the clinician using whatever method the health system requires: password, multi-factor authentication, or biometrics. Your application never participates in this step. After successful authentication, the identity provider generates a security token that asserts the user's identity and attributes, then redirects the browser back to your application with this token attached.
"The authentication happens at the identity provider, but the authorization to use your app happens through the trusted token exchange."
Token validation and access
Your application receives the token and validates its cryptographic signature using public keys that were exchanged when the federation relationship was established. This validation proves the token came from the trusted identity provider and hasn't been tampered with during transit.
Once validated, your application extracts the user's identity attributes from the token and grants access based on those claims. The entire process takes seconds and happens transparently to the clinician, who simply sees your application load without requiring separate credentials.
Key components and protocols
When you're exploring what is identity federation from a technical standpoint, you need to understand the specific protocols and components that make it work in healthcare environments. These standards define exactly how authentication assertions get created, transmitted, and validated between your application and health systems.
SAML and OpenID Connect
SAML (Security Assertion Markup Language) remains the dominant protocol for enterprise federation, particularly in healthcare where EPIC and other EHR systems rely on it for SMART on FHIR integrations. SAML uses XML-based security tokens to carry identity assertions between the identity provider and your application, with built-in signature verification and encryption support.
OpenID Connect builds on OAuth 2.0 to provide a modern alternative that uses JSON Web Tokens (JWT) instead of XML. While SAML handles the heavy lifting in most health system federations today, OpenID Connect is gaining traction for consumer-facing healthcare applications and mobile integrations where its lighter weight format delivers better performance.
"The protocol you choose depends less on preference and more on what the health system's identity infrastructure already supports."
Metadata exchange and trust
Before any authentication can happen, your application and the health system must exchange federation metadata that establishes the trust relationship. This metadata includes public keys for signature verification, endpoint URLs where authentication requests should be sent, and supported protocol versions.
Trust doesn't happen automatically. Both parties verify the metadata through out-of-band mechanisms like manual verification or certificate authorities. Once established, this trust allows your application to validate tokens from the identity provider without requiring real-time communication for each authentication event, which improves reliability when network issues occur.
Identity federation vs SSO
When people ask what is identity federation versus Single Sign-On, they're often confused because the two concepts overlap but serve different purposes. SSO focuses on user convenience by letting you authenticate once and access multiple applications without re-entering credentials. Federation focuses on trust relationships between separate security domains, enabling authentication across organizational boundaries. Your application might use both, or federation might enable SSO, but they're not the same thing.

How they overlap
SSO and federation work together in most healthcare integrations. When a clinician logs into EPIC and your SMART on FHIR app launches without additional credentials, that seamless experience is SSO. The underlying mechanism that makes it possible is federation between the health system's identity provider and your application. Federation establishes the trust, while SSO delivers the user experience.
"SSO is what users experience, federation is the infrastructure that makes it possible across organizations."
Where they diverge
Federation can exist without SSO. A health system might federate with your application but still require explicit user consent or additional authentication for each access, eliminating the single sign-on experience. Conversely, SSO can work within a single organization's applications without any federation, using shared session management instead of cross-domain trust protocols.
The key distinction matters for architecture decisions. When you implement federation using SAML or OpenID Connect, you're building cross-organizational trust relationships that persist regardless of session state. SSO configurations handle how those authenticated sessions extend across multiple applications. Your application needs federation to integrate with health systems, but the SSO behavior depends on how you configure session handling after the federated authentication completes.
Common use cases and examples
Understanding what is identity federation becomes clearer when you see where it operates in real healthcare workflows. These examples show how federation solves specific integration challenges that healthcare vendors face when connecting applications across organizational boundaries. The patterns repeat across different specialties and use cases, making federation a fundamental building block for interoperability.
SMART on FHIR app launches
Your application launches directly from within EPIC's clinical interface when a clinician clicks your app's icon. Federation handles authentication instantly because the health system's identity provider has already verified the clinician when they logged into EPIC. Your app receives a token confirming their identity and role without interrupting their workflow.
This pattern extends to specialized clinical scenarios like remote patient monitoring dashboards, clinical decision support tools, and telehealth integrations. Each application trusts the same identity assertion from the health system, eliminating redundant login prompts that would break the clinician's focus during patient care.
"Federation turns multiple authentication events into a single trusted identity that flows across your entire application ecosystem."
Multi-system patient coordination
Referral management platforms use federation when care coordinators at one health system need to track patient services delivered by external providers. Federation allows the coordinator to authenticate once through their own organization while accessing real-time updates from partner organizations that maintain separate security domains. The token exchange proves they have legitimate access without creating shared credential databases that multiply security risks.
Accountable care organizations (ACOs) deploy federation when member hospitals need unified access to population health analytics while maintaining independent IT infrastructures. Each hospital's clinicians authenticate through their own identity provider, but federation gives them seamless access to shared dashboards and reporting tools.
Final takeaways
Identity federation delivers the secure, cross-organizational authentication that healthcare interoperability requires. When you understand what is identity federation and how it establishes trust between your application and health systems, you can build integrations that protect credentials while delivering seamless access. The protocols and token exchanges might seem complex initially, but they solve real problems around credential management, compliance, and user experience that would otherwise block your application's adoption.
Your focus should stay on building clinical value, not wrestling with authentication infrastructure. VectorCare handles the complete SMART on FHIR integration including federation setup, protocol compliance, and ongoing security maintenance. If you're ready to build and deploy your SMART on FHIR app without spending months on authentication engineering, federation becomes one less technical barrier between your solution and the health systems that need it.
The Future of Patient Logistics
Exploring the future of all things related to patient logistics, technology and how AI is going to re-shape the way we deliver care.