What Is a Business Associate Agreement (BAA) Under HIPAA?


What Is a Business Associate Agreement (BAA) Under HIPAA?
If you're a healthcare vendor working with patient data, or planning to, you've likely encountered the question: what is a business associate agreement? This legal document sits at the core of HIPAA compliance, and getting it wrong can result in hefty fines and damaged partnerships with health systems.
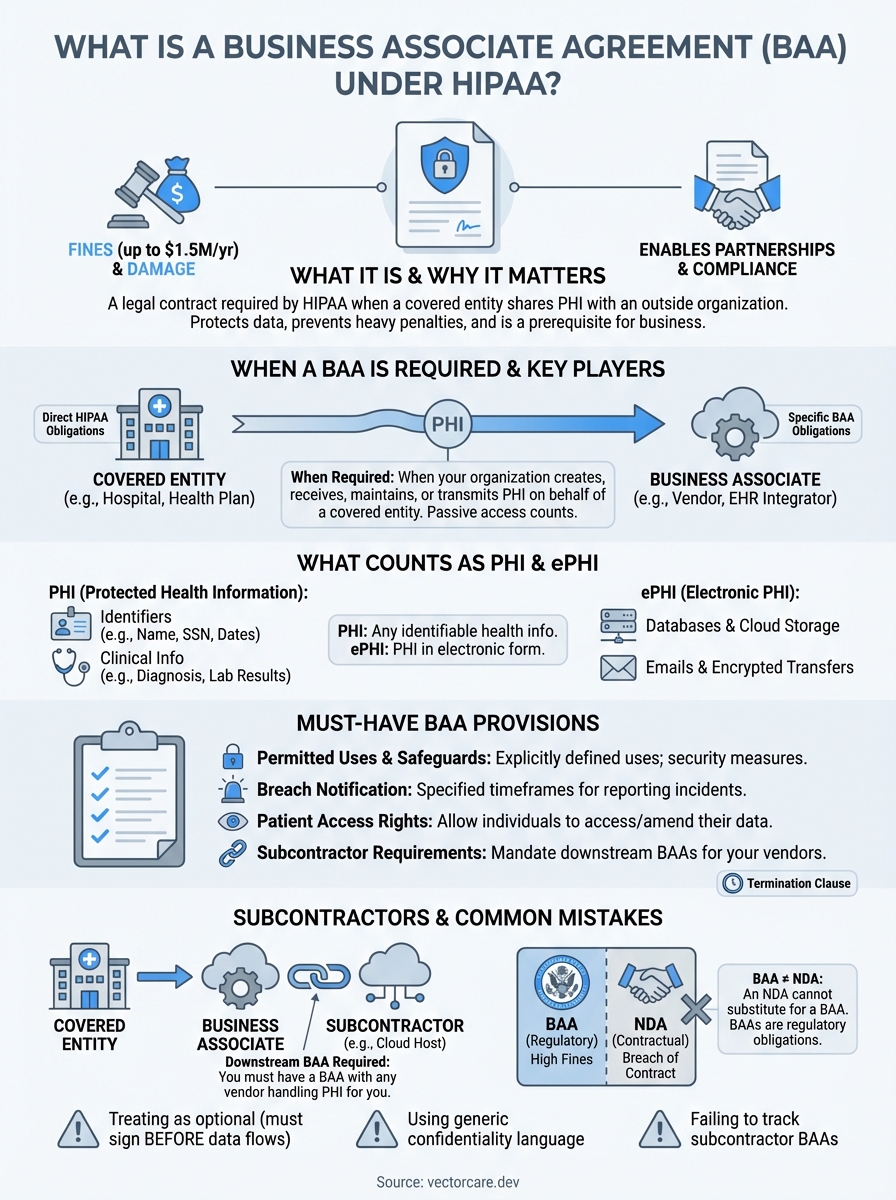
A Business Associate Agreement (BAA) is a contract required by HIPAA whenever a covered entity (like a hospital or health plan) shares protected health information (PHI) with an outside organization. For healthcare vendors building integrations with EHR systems like EPIC, understanding BAAs isn't optional, it's a prerequisite for doing business. Health systems won't move forward without one, and your compliance posture directly impacts your ability to win contracts.
At VectorCare, we handle HIPAA and SOC2 compliance as part of our managed SMART on FHIR platform, including the BAA requirements that come with EHR integrations. We've seen firsthand how confusing these agreements can be for vendors focused on building great healthcare products rather than navigating regulatory paperwork.
This guide breaks down everything you need to know about Business Associate Agreements: what they are, who needs them, what they must include, and how to ensure your organization meets its legal obligations when handling PHI.
Why business associate agreements matter for HIPAA
HIPAA's Privacy and Security Rules place strict requirements on how protected health information flows between organizations. Business Associate Agreements exist because healthcare data rarely stays within a single organization. When covered entities need outside help with billing, IT services, data analytics, or clinical tools, they must share PHI. Without a BAA, this sharing violates federal law.
The Department of Health and Human Services (HHS) doesn't view BAAs as optional paperwork. They represent a legal mechanism that extends HIPAA's reach beyond covered entities to any organization that touches PHI. Your BAA creates enforceable obligations on both parties, establishing clear responsibilities for safeguarding patient data and outlining the consequences of breaches.
The financial stakes of BAA violations
Operating without a BAA when one is required can result in civil penalties ranging from $100 to $50,000 per violation, with annual maximums reaching $1.5 million per violation category. These penalties apply to both the covered entity that failed to obtain a BAA and the business associate that proceeded without one. Criminal violations can carry fines up to $250,000 and prison sentences of up to 10 years for knowing misuse of PHI.
Beyond direct fines, the reputational damage from a HIPAA violation can destroy your business relationships in healthcare. Health systems have zero tolerance for vendors that compromise patient privacy. A single breach investigation can trigger contract terminations across your entire customer base, effectively ending your ability to operate in the healthcare market. Insurance companies may also deny coverage for breaches that occurred while you were operating without proper BAAs.
Organizations that handle PHI without a signed BAA are operating in violation of HIPAA from day one, regardless of their security practices.
BAAs as business enablers
Your signed BAA doesn't just satisfy a compliance checkbox. It demonstrates to health systems that you understand the regulatory landscape and take patient privacy seriously. Healthcare organizations won't even consider vendors who can't produce a proper BAA. Understanding what is a business associate agreement and having one ready to execute accelerates your sales cycle and removes a major barrier to partnership.
BAAs also clarify responsibilities when things go wrong. They specify who notifies patients during a breach, who covers investigation costs, and what indemnification applies. These provisions protect your organization by defining the boundaries of your liability. Without a BAA, you face uncertainty about your legal exposure if a covered entity mishandles data you provided, or if your systems are compromised.
The agreement creates a compliance framework for your ongoing relationship. It requires you to implement appropriate safeguards, report security incidents within specified timeframes, and allow the covered entity to audit your practices. These obligations might seem burdensome, but they force you to build security practices that protect your business and your customers. Healthcare vendors with mature BAA processes and strong compliance programs win more contracts and command higher valuations.
When a business associate agreement is required
You need a BAA whenever your organization creates, receives, maintains, or transmits protected health information on behalf of a covered entity. This requirement applies the moment PHI enters your systems, regardless of whether you actively view the data or simply store it. Understanding what is a business associate agreement means recognizing that passive access still counts as handling PHI under HIPAA regulations.

The trigger isn't about your intent or how you use the data. If a hospital sends you patient records for any business purpose, you become a business associate by definition. Your BAA obligation exists before you perform any work. Health systems that share PHI without first executing a BAA with your organization violate HIPAA, and you violate HIPAA by accepting that data without a signed agreement in place.
Activities that trigger BAA requirements
Your organization needs a BAA when you perform specific functions or services that involve PHI exposure. Common scenarios include claims processing, data analysis, utilization review, quality assurance, billing services, benefit management, practice management, and repricing. If you provide IT services like cloud hosting, data storage, or software development that touches PHI, you need a BAA.
Healthcare vendors building EHR integrations through platforms like EPIC's SMART on FHIR always require BAAs. Your application pulls patient data from the EHR, processes it, and potentially stores it, all of which constitute business associate activities. Payment processors, email providers handling PHI communications, document shredding services, and legal consultants reviewing patient records all need BAAs before starting work.
Business associates must have a signed BAA in place before any PHI is transmitted to or accessed by their systems.
When you don't need a BAA
You don't need a BAA if your organization qualifies as a covered entity itself, since covered entities have direct HIPAA obligations. Healthcare providers, health plans, and healthcare clearinghouses don't sign BAAs with each other when they exchange data for treatment, payment, or operations. They follow HIPAA's Privacy Rule directly for these routine disclosures.
Conduit services that simply transport encrypted data without accessing its contents don't need BAAs. The postal service, internet service providers, and couriers fall into this category because they lack access to the actual PHI. However, if your service includes any data storage, even temporary caching, you move beyond conduit status and need a BAA.
Your organization doesn't need a BAA for de-identified data that meets HIPAA's safe harbor or expert determination standards. Once PHI is properly stripped of identifying information, it no longer triggers BAA requirements. Similarly, limited data sets that remove direct identifiers but retain dates and geographic information require a data use agreement rather than a full BAA.
Covered entity vs business associate
The distinction between covered entities and business associates determines who needs a BAA with whom. This classification shapes your entire HIPAA compliance strategy and defines your legal obligations when handling protected health information. Your organization's role in the healthcare ecosystem dictates whether you sign BAAs with others or require them from vendors who work for you.

Who qualifies as a covered entity
HIPAA defines three categories of covered entities: healthcare providers, health plans, and healthcare clearinghouses. Hospitals, clinics, doctors, dentists, psychologists, and pharmacies all qualify as covered entities when they transmit health information electronically. Your organization is a covered entity if you provide medical treatment directly to patients and bill insurance electronically.
Health plans include insurance companies, HMOs, Medicare, Medicaid, employer-sponsored health plans, and government health programs. These organizations pay for healthcare services and maintain patient eligibility records. Healthcare clearinghouses process nonstandard health information into HIPAA-compliant formats, converting claims data between different systems.
Covered entities have direct HIPAA obligations and require BAAs from any outside organization that handles PHI on their behalf.
Who qualifies as a business associate
Your organization becomes a business associate when you perform functions or services for a covered entity that involve creating, receiving, maintaining, or transmitting PHI. This status applies to vendors providing data analysis, claims processing, quality assurance, billing, benefit management, and IT services. Understanding what is a business associate agreement requires recognizing that your role as a service provider to healthcare organizations places you in this category.
Software vendors building EHR integrations through platforms like EPIC's SMART on FHIR operate as business associates. Your application accesses patient data from the health system's EHR, which makes you subject to BAA requirements. Cloud hosting providers, email services handling PHI, consultants reviewing patient records, and attorneys working on healthcare cases all function as business associates.
Key compliance differences
Covered entities face direct regulation under HIPAA's Privacy, Security, and Breach Notification Rules. They must implement comprehensive compliance programs, designate privacy officers, train staff, and respond to patient rights requests. Your organization as a covered entity shoulders the primary responsibility for protecting patient information and ensuring all business partners sign BAAs.
Business associates inherit specific HIPAA obligations through their BAAs but follow more targeted requirements. You must implement appropriate safeguards, report security incidents to covered entities, and return or destroy PHI when contracts end. Your compliance program focuses on the specific functions you perform rather than the full scope of HIPAA requirements that covered entities manage.
What counts as PHI and ePHI in a BAA context
Your BAA protects protected health information, which HIPAA defines as any information that identifies a patient and relates to their health condition, healthcare services, or payment for care. This definition casts a wide net that captures far more data types than most vendors initially realize. Understanding what is a business associate agreement requires recognizing exactly what patient information triggers your compliance obligations.
Protected health information (PHI) identifiers
PHI includes 18 specific identifiers that HIPAA explicitly lists. Your systems handle PHI when they process names, addresses (beyond state level), dates related to patients, phone numbers, fax numbers, email addresses, Social Security numbers, medical record numbers, health plan numbers, account numbers, certificate numbers, vehicle identifiers, device identifiers, URLs, IP addresses, biometric identifiers, photos, and any unique identifying code. A single data element combined with health information creates PHI that your BAA must protect.
Clinical information also constitutes PHI even without direct identifiers. Your application handles PHI when it processes diagnosis codes, lab results, prescription records, treatment plans, doctor's notes, and insurance claims. Demographics like race, ethnicity, and language preferences become PHI when linked to healthcare context. Even appointment schedules and patient portal access logs qualify as protected information under HIPAA.
Your organization handles PHI the moment any individually identifiable health information enters your systems, regardless of whether you actively view or process it.
Electronic PHI (ePHI) specific considerations
Electronic protected health information refers to any PHI your organization creates, receives, maintains, or transmits in electronic form. This includes data in your databases, files on your servers, emails containing patient information, encrypted transmissions between systems, backup tapes, mobile device storage, and cloud-hosted records. Your BAA covers ePHI whether it sits at rest in storage or moves in transit across networks.
Healthcare vendors building EHR integrations exclusively handle ePHI since data flows through APIs and software interfaces. Your application processes ePHI when it queries patient records via EPIC's SMART on FHIR platform, displays clinical data in user interfaces, stores information in your database, or transmits results back to the health system. Word processing documents containing patient information, spreadsheets with health data, and PDF reports all qualify as ePHI that your BAA governs.
Temporary data storage counts as ePHI handling. Your application's cache, log files capturing patient identifiers, cookies containing health information, and even deleted files that remain recoverable all trigger BAA requirements. You cannot argue that transient data falls outside your agreement's scope.
What a HIPAA-compliant BAA must include
HIPAA regulations specify mandatory provisions that every Business Associate Agreement must contain. Your BAA cannot simply reference compliance requirements in general terms. It must explicitly address specific obligations, permitted uses, and safeguards that both parties agree to follow. Understanding what is a business associate agreement includes recognizing these non-negotiable elements that HHS enforces during audits and investigations.

Required provisions every BAA needs
Your agreement must establish permitted uses and disclosures of PHI, limiting your organization to activities specified in the contract. It requires you to implement appropriate administrative, physical, and technical safeguards that protect ePHI confidentiality, integrity, and availability. The BAA must mandate subcontractor agreements when you engage others to handle PHI on your behalf.
Your BAA needs breach notification requirements specifying timeframes for reporting security incidents to the covered entity. It must include provisions for PHI access, allowing individuals to request copies of their information that you maintain. The agreement requires you to make PHI available for the covered entity to fulfill amendment requests from patients and to provide an accounting of disclosures when requested.
Your BAA must explicitly grant the covered entity the right to terminate the contract if you violate material terms or fail to cure violations within a specified timeframe.
Enforcement and termination clauses
The agreement must authorize the covered entity to audit your compliance practices and review your security measures. Your BAA needs provisions for PHI return or destruction when the contract ends, with exceptions for legal retention requirements. It must specify remedies for breaches, including your liability for violations and the covered entity's right to immediately terminate for material breaches.
Indemnification provisions protect both parties from third-party claims resulting from the other's HIPAA violations. Your BAA should clearly define when you act as a business associate versus when you might function in another capacity. These definitions prevent confusion about which activities fall under BAA governance and which remain outside its scope.
Documentation and updates
Your organization must maintain signed copies of all BAAs with covered entities and business associates. These documents serve as proof of compliance during HHS investigations and demonstrate your commitment to patient privacy. BAAs require periodic review and updates when regulations change, services expand, or new security risks emerge that affect your handling of protected health information.
Subcontractors and downstream BAAs
Your organization doesn't always handle PHI alone. When you hire third-party vendors to perform functions that involve accessing or processing protected health information, you create a subcontractor relationship that triggers additional BAA requirements. These downstream agreements extend the compliance chain from covered entities through business associates to any organization they engage for PHI-related services.
HIPAA regulations hold you responsible for ensuring your subcontractors maintain the same safeguards and restrictions that govern your own handling of PHI. You cannot outsource compliance obligations simply by hiring another vendor. Understanding what is a business associate agreement includes recognizing that your BAA with the covered entity requires you to obtain written assurances from subcontractors before they touch any protected information.
When you need downstream BAAs
You must obtain a BAA from any vendor that creates, receives, maintains, or transmits PHI on your behalf. Cloud hosting providers storing your application's database need downstream BAAs. Email services that handle PHI communications, analytics platforms processing patient data, and backup providers maintaining copies of health records all require these agreements before you grant them access.
Software development contractors building features that touch PHI fall under this requirement. Your customer support vendors need BAAs if they access patient information while troubleshooting issues. Payment processors handling healthcare transactions, security firms conducting penetration tests on systems containing PHI, and data centers housing your physical servers all qualify as subcontractors requiring written agreements.
Your covered entity holds you liable for any HIPAA violations committed by your subcontractors, making downstream BAAs critical to your own compliance.
Your obligations as the primary business associate
Your role as a business associate requires you to vet subcontractors for HIPAA compliance before engaging them. You must ensure downstream BAAs contain the same provisions and restrictions that your agreement with the covered entity imposes. This means your subcontractors face identical obligations regarding safeguards, breach notification, PHI access, and termination rights.
You bear responsibility for monitoring subcontractor compliance throughout your relationship. Your BAA with the covered entity typically requires you to report any subcontractor violations and take corrective action when problems arise. If your subcontractor breaches PHI, you face potential liability under your primary BAA regardless of whether the breach resulted from their negligence or yours. This cascading liability structure motivates you to choose vendors with strong security practices and mature compliance programs.
BAA vs NDA and other confidentiality agreements
Healthcare vendors often confuse Business Associate Agreements with standard confidentiality agreements like NDAs. While both documents protect sensitive information, they serve different legal purposes and trigger different obligations. Your organization needs to understand when each agreement applies because using the wrong document creates compliance gaps that expose you to HIPAA violations. A standard NDA cannot substitute for a BAA when you handle protected health information.

Key legal and functional differences
A Non-Disclosure Agreement (NDA) creates a contractual obligation to keep information confidential between two parties. Your organization signs NDAs to protect trade secrets, business strategies, or proprietary data during partnerships or sales discussions. These agreements rely on contract law for enforcement and typically specify remedies like injunctions or damages for breaches.
Business Associate Agreements operate under federal healthcare regulations rather than just contract law. Your BAA doesn't simply protect confidentiality; it imposes specific HIPAA requirements for safeguarding PHI, reporting breaches, allowing audits, and providing patients with access rights. Understanding what is a business associate agreement means recognizing that violations trigger regulatory penalties from HHS, not just breach of contract claims. Your NDA might prohibit sharing information, but your BAA requires you to implement technical safeguards, train staff, and maintain detailed documentation of your security practices.
NDAs protect business confidentiality through contract law, while BAAs enforce federal healthcare privacy regulations with penalties reaching $1.5 million annually per violation category.
When each agreement type applies
You need a BAA whenever you handle protected health information on behalf of a covered entity, regardless of whether you also have an NDA in place. Your organization requires an NDA when discussing business terms, reviewing financial projections, or evaluating proprietary technology before signing contracts. These documents often coexist because business relationships involve both confidential business information and patient data.
Your BAA takes precedence for PHI governance even when an NDA exists. If your vendor agreement includes confidentiality provisions covering all shared data, you still need a separate BAA that specifically addresses HIPAA requirements. Generic confidentiality clauses in master service agreements cannot replace the detailed obligations that HIPAA mandates for business associate relationships. Some organizations draft combined agreements that include both NDA provisions and full BAA language, but you must ensure the document explicitly covers all required BAA elements to maintain compliance.
How to create, negotiate, and maintain BAAs
Your organization faces a choice when creating Business Associate Agreements: start from scratch, adapt a template, or use agreements provided by covered entities. Most healthcare vendors begin with a standard template that includes all mandatory HIPAA provisions, then customize it for specific services and security measures. Understanding what is a business associate agreement helps you recognize which provisions require flexibility and which remain non-negotiable across all relationships.
Creating an effective BAA requires input from legal counsel familiar with HIPAA regulations, not just general contract attorneys. Your agreement must balance protecting your organization from excessive liability while satisfying the covered entity's compliance requirements. This process takes time, but investing in a solid template accelerates future agreements and reduces negotiation cycles with new customers.
Starting with a template
Your first BAA should come from an attorney experienced in healthcare privacy law who can draft language that complies with current regulations. Many covered entities provide their own BAA templates, which simplifies the process but often includes provisions that favor their interests over yours. You need to review these templates carefully for liability clauses, indemnification scope, and audit rights that might expose your organization to unreasonable risk.
Templates from covered entities typically include the minimum required provisions plus additional protections. Your review should focus on termination triggers, notice periods for security incidents, and requirements for PHI destruction. Some agreements demand immediate termination rights for any violation, while others allow cure periods that give you time to address issues before the relationship ends.
Your BAA template needs legal review by HIPAA-qualified counsel, not just adaptation from generic confidentiality agreements found online.
Negotiation strategies
Covered entities expect to negotiate specific provisions rather than accepting templates without changes. Your organization should identify which terms you can accept without modification and which require discussion. Common negotiation points include liability caps, insurance requirements, audit frequency, and the definition of what constitutes a reportable security incident. You gain leverage when you demonstrate existing compliance programs and security certifications that reduce the covered entity's risk.
Ongoing maintenance requirements
Your signed BAA requires annual review to ensure it reflects current regulations, services, and security practices. HIPAA updates, new subcontractor relationships, and expanded services all trigger the need for amendments. You must document all reviews and maintain version control for executed agreements, creating a clear record of what terms governed your relationship at any point in time.
Common BAA mistakes and how to avoid them
Healthcare vendors make predictable errors when implementing Business Associate Agreements, and these mistakes create compliance gaps that invite regulatory scrutiny. Your organization can avoid most problems by recognizing common pitfalls before they trigger violations. Learning from other vendors' missteps saves you from expensive corrective actions, potential fines, and damaged relationships with health systems that expect mature compliance practices.
Treating BAAs as optional paperwork
Many vendors delay obtaining signed agreements until after they start handling PHI, operating under the assumption that their security measures alone provide sufficient protection. This mistake violates HIPAA from day one because the regulations require a BAA before any PHI transmission occurs. Your organization faces liability for every moment you handle protected information without proper documentation, regardless of how well you safeguard the data. You must execute agreements before technical integrations go live, not after. Health systems conducting audits will immediately flag missing BAAs as critical violations that could terminate your contract.
Operating without a signed BAA constitutes a HIPAA violation even if your security practices exceed regulatory requirements.
Using generic confidentiality language
Your standard NDA or master service agreement cannot substitute for a properly drafted BAA. Vendors frequently make this mistake by assuming confidentiality provisions cover HIPAA requirements, but generic language lacks the specific safeguards, breach notification timelines, and audit rights that regulations mandate. Understanding what is a business associate agreement means recognizing that you need explicit provisions addressing PHI access, amendment procedures, and termination triggers that standard confidentiality clauses never include. You must review every agreement with covered entities to ensure it contains all required elements, even when the health system provides the template.
Failing to track subcontractor BAAs
Your organization becomes responsible for subcontractor violations, yet many vendors lose track of which downstream providers need agreements. This oversight creates compliance gaps when auditors discover that your cloud hosting provider, email service, or analytics platform never signed a BAA. You need a centralized system that documents every vendor touching PHI, tracks agreement status, monitors expiration dates, and flags relationships requiring updates when services change. Regular reviews prevent situations where you discover compliance problems only after a covered entity demands proof of your subcontractor agreements during their annual audit.
Wrap-up and next steps
Understanding what is a business associate agreement positions your healthcare vendor organization to operate compliantly and build strong partnerships with health systems. Your BAA serves as the legal foundation for handling protected health information, creating enforceable obligations that protect both parties and ensure patient privacy. This contract extends beyond simple confidentiality, embedding HIPAA's requirements into your daily operations through specific safeguards, breach notification procedures, and audit rights that demonstrate your commitment to regulatory compliance.
Your next step involves reviewing your current vendor relationships to ensure you have executed BAAs with every covered entity you serve and every subcontractor who touches PHI. This audit identifies compliance gaps that require immediate attention. If you're building EPIC integrations and want to focus on your core product rather than navigating HIPAA complexities, VectorCare handles compliance requirements including BAAs, SOC2 certification, and SMART on FHIR standards as part of our managed platform. You get faster deployment and peace of mind knowing your regulatory obligations are addressed from day one.
The Future of Patient Logistics
Exploring the future of all things related to patient logistics, technology and how AI is going to re-shape the way we deliver care.