SOC 2 Trust Services Criteria: Understanding the 5 Categories


SOC 2 Trust Services Criteria: Understanding the 5 Categories
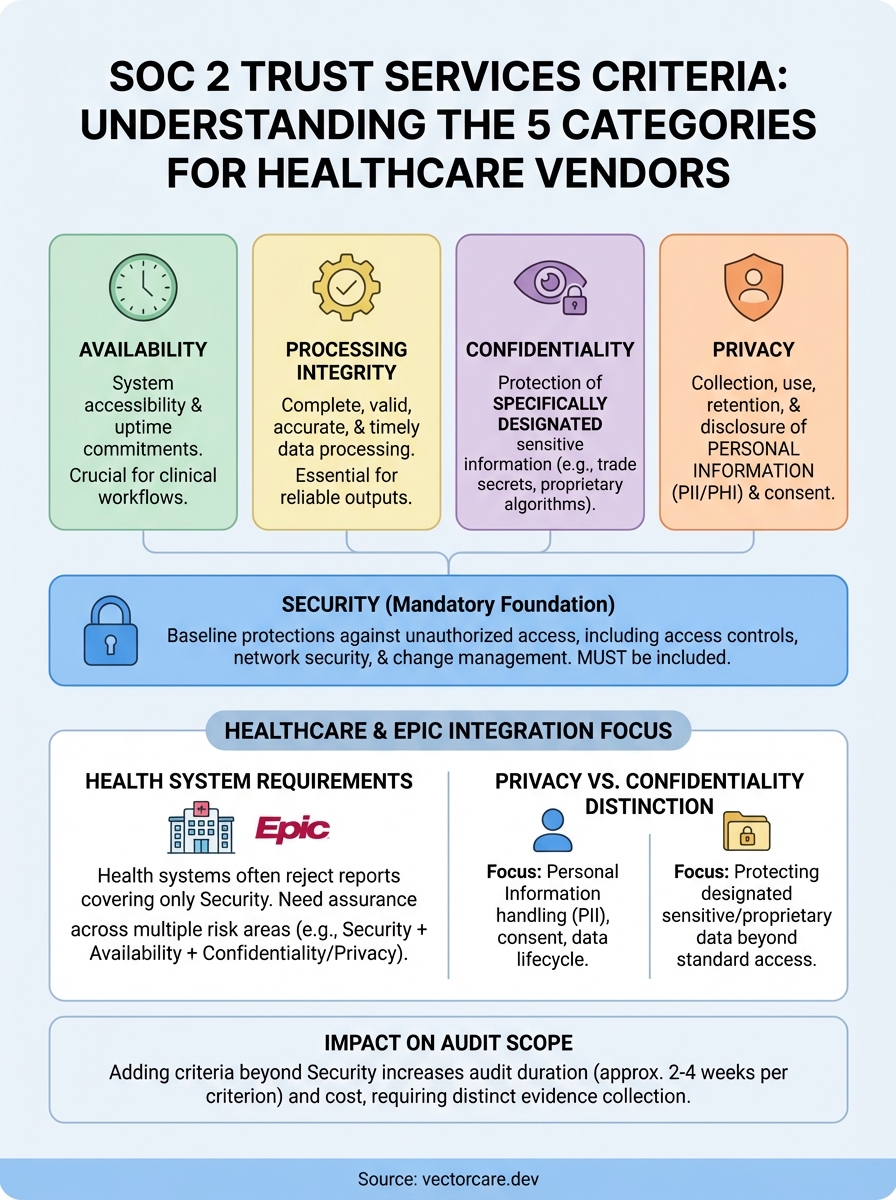
SOC 2 trust services criteria are the five security categories that auditors evaluate when certifying your organization's data handling practices. Think of them as quality standards for protecting customer information. Every SOC 2 audit examines Security (the mandatory baseline), while you choose from four additional criteria based on your business needs: Availability, Processing Integrity, Confidentiality, and Privacy. Healthcare vendors pursuing EPIC integration typically need multiple criteria to meet health system requirements.
This guide breaks down each of the five trust services criteria and helps you understand what they measure. You'll learn which criteria are required versus optional, how to select the right combination for your organization, and why the distinction between privacy and confidentiality matters more than most vendors realize. We'll also cover how your criteria selection affects audit complexity and timeline, so you can plan your compliance strategy with realistic expectations. Whether you're preparing for your first SOC 2 audit or refining your current scope, you'll find practical guidance for building a certification that meets your business goals.
Why trust services criteria matter for healthcare vendors
Healthcare vendors face stricter security requirements than most software companies because you handle protected health information (PHI) that falls under HIPAA regulations. When you pursue contracts with health systems, your SOC 2 report serves as proof of your security practices, but not all reports carry equal weight. Health systems review which trust services criteria you selected because each category addresses different risk areas they care about.
Health system requirements go beyond basic security
Your choice of soc 2 trust services criteria directly affects your competitive position when bidding for contracts. Most health systems require vendors to demonstrate Security and Availability as baseline criteria, since clinical workflows cannot tolerate system downtime or data breaches. If your application processes sensitive patient data like genetic information or mental health records, you'll likely need Confidentiality as well. The Privacy criterion becomes essential when you collect, use, or disclose personal information in ways that go beyond direct care delivery.
Health systems typically reject SOC 2 reports that only cover Security because they need assurance across multiple risk areas.
EPIC integration adds another layer of complexity to your compliance requirements. The EPIC App Orchard expects vendors to maintain robust security controls, and many health systems won't sign vendor agreements without evidence of comprehensive trust services coverage. Selecting the wrong combination of criteria means you'll need to repeat the audit process later to add missing categories, which costs additional time and money. Your initial criteria selection should align with both your current operations and your expected customer requirements over the next 12 months.
How the five trust services criteria work
The AICPA Trust Services Criteria establish a standardized framework that auditors use to evaluate your organization's controls. Each criterion focuses on specific operational risks that affect how you protect customer data. Your auditor tests whether you've designed appropriate controls for each selected criterion and whether those controls operate effectively throughout the audit period. The five soc 2 trust services criteria build upon each other, with Security serving as the foundation that supports all other categories.
Security: the mandatory foundation
Every SOC 2 audit includes the Security criterion because it addresses fundamental controls that protect system resources from unauthorized access. This category covers your access controls, logical security, network security, and change management processes. You cannot opt out of Security because the other four criteria depend on these baseline protections to function properly.
Security forms the foundation of your SOC 2 audit, and you must include it regardless of which additional criteria you select.
The four optional categories
You select from Availability, Processing Integrity, Confidentiality, and Privacy based on your business operations and customer requirements. Each addresses distinct risk areas:

- Availability: System accessibility and uptime commitments
- Processing Integrity: Complete, valid, accurate, and timely processing
- Confidentiality: Protection of specifically designated sensitive data
- Privacy: Collection, use, retention, and disclosure of personal information
Healthcare vendors typically need multiple criteria because health systems evaluate risk across different operational areas when reviewing vendor compliance.
How to determine which criteria your organization needs
Your criteria selection should reflect both your operational practices and your customer requirements. Start by reviewing the commitments you make to customers in your service level agreements, privacy policies, and security documentation. If you guarantee specific uptime percentages, you need Availability. When you promise accurate data processing or claim your system produces reliable outputs, Processing Integrity becomes relevant. Healthcare vendors handling PHI should evaluate whether their data protection practices require Confidentiality, Privacy, or both trust services categories.
Assess your contractual obligations
Review your existing and prospective customer contracts to identify explicit compliance requirements. Many health systems specify which soc 2 trust services criteria they expect vendors to maintain, and some EPIC partners require specific combinations based on the application type. Your sales team can provide valuable input about compliance questions that arise during procurement, which often signal the criteria you'll need for competitive positioning.
Customer contracts often specify required SOC 2 criteria before you begin the audit process, so review these documents early.
Document the types of data your system handles and how you process it. If you collect patient contact information, demographic data, or health records, you likely need Privacy. Systems that protect designated confidential information beyond standard access controls require Confidentiality coverage.
Differences between privacy and confidentiality
Healthcare vendors often confuse these two trust services categories because both address sensitive information protection. The distinction matters because selecting the wrong criterion creates gaps in your audit coverage that health systems will notice. Confidentiality focuses on protecting information you've designated as confidential through agreements or policies, while Privacy addresses how you collect, use, retain, and disclose personal information. You might need both criteria depending on your data handling practices.

When confidentiality applies
Your organization needs the Confidentiality criterion when you protect specific types of information beyond standard access controls. This applies when you handle trade secrets, proprietary algorithms, or specially designated patient data that requires protection separate from general security measures. The criterion tests whether you maintain appropriate safeguards for information that customers or partners specifically label as confidential through contracts or service agreements.
Confidentiality addresses protection of specifically designated sensitive information, not all personal data your system handles.
When privacy applies
Privacy becomes necessary when you collect, use, store, or share personal information as part of your service delivery. Healthcare applications that gather patient demographics, contact details, or health records need this criterion because you make commitments about how you handle this personally identifiable information (PII). Your privacy policy creates obligations that auditors verify through the Privacy criterion of the soc 2 trust services criteria framework.
Impact of scope on audit duration and complexity
Your choice of soc 2 trust services criteria directly affects how long your audit takes and how much it costs. Audits covering only Security typically require 6-8 weeks to complete, while adding Availability, Processing Integrity, Confidentiality, or Privacy extends the timeline by 2-4 weeks per criterion. Each additional category requires your auditor to test separate control sets, review additional documentation, and validate different operational processes. Healthcare vendors selecting multiple criteria should expect audit periods lasting 12-16 weeks from kickoff to final report delivery.
How additional criteria extend your timeline
Adding criteria increases complexity because each category requires distinct evidence collection and testing procedures. Your team needs to provide documentation for controls specific to each criterion, and auditors must verify that these controls operated effectively throughout the entire audit period. Availability requires uptime logs and incident response records, Processing Integrity needs data accuracy validation, and Privacy demands evidence of consent management and data retention practices.
Each additional criterion typically adds 2-4 weeks to your audit timeline because auditors must test separate control sets.
Cost implications of multi-criteria audits
Audit firms charge based on the scope and complexity of your engagement. Adding criteria beyond Security increases fees by $5,000-$15,000 per category depending on your organization's size and operational complexity. Budget appropriately for these incremental costs when planning your compliance strategy.
Building your compliance strategy
Start your SOC 2 planning by mapping which trust services criteria align with your customer requirements and operational practices. Healthcare vendors pursuing EPIC integration should expect to implement Security plus at least two additional criteria to meet health system expectations. Review your service agreements, privacy policies, and data handling processes to identify the commitments you've already made to customers, then select criteria that validate those promises through independent audit.
Budget adequate time and resources for your audit preparation. Organizations selecting multiple soc 2 trust services criteria need 3-6 months to document controls, gather evidence, and remediate gaps before the formal audit period begins. If you're building SMART on FHIR applications for EPIC integration, VectorCare handles HIPAA and SOC 2 compliance requirements while you focus on your core product development. Your compliance strategy should balance thorough coverage with practical implementation timelines that support your business growth objectives.
The Future of Patient Logistics
Exploring the future of all things related to patient logistics, technology and how AI is going to re-shape the way we deliver care.