Secrets Management Definition: What It Is And Key Practices


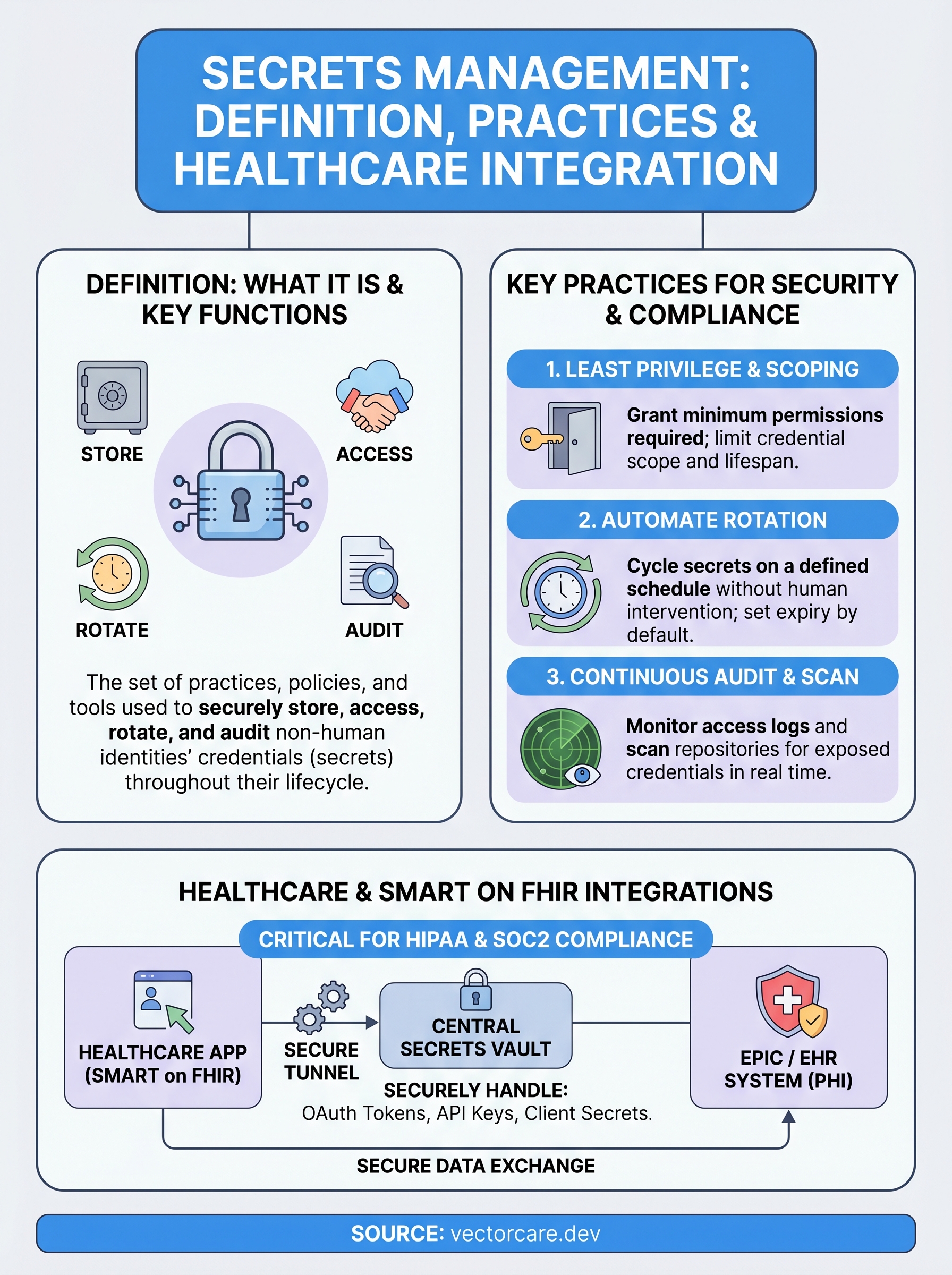
Every application your team builds or integrates with relies on credentials that grant access to sensitive systems, API keys, OAuth tokens, database passwords, encryption keys, and certificates. These are collectively known as "secrets," and a secrets management definition boils down to this: the set of practices, policies, and tools used to securely store, access, rotate, and audit these credentials throughout their lifecycle. Get it wrong, and you hand attackers the keys to protected health information, payment systems, or critical infrastructure.
For healthcare vendors building integrations with EHR systems like EPIC, the stakes are even higher. SMART on FHIR applications exchange OAuth tokens and API credentials with clinical systems constantly. A leaked token doesn't just expose code, it can expose patient data and violate HIPAA regulations, putting your contracts and your business at risk. Proper secrets management is a foundational requirement for SOC2 and HIPAA compliance, not an afterthought.
At VectorCare, we built our no-code SMART on FHIR platform with this reality baked in. Our managed infrastructure handles the secure credential lifecycle for EPIC integrations so vendors don't have to engineer it from scratch. But whether you use a managed platform or build your own stack, understanding how secrets management works is essential. This article breaks down exactly what secrets are, why managing them matters, the core practices that keep applications secure, and how to evaluate your current approach.
Secrets management definition in plain English
At its core, the secrets management definition covers how organizations control the credentials that machines use to talk to each other. Think of it as the equivalent of a password manager for your entire software infrastructure, but designed for non-human identities like applications, services, containers, and automated pipelines rather than individual users. When your app calls an external API, authenticates to a database, or fetches data from an EHR system, it presents a secret to prove it has permission. Secrets management is the system that creates, delivers, protects, rotates, and eventually retires those credentials in a controlled way.
Secrets management is not just a security best practice. It is the operational backbone that determines whether your applications can access what they need without exposing what they should not.
How secrets differ from regular credentials
Human passwords get reset every few months and sit behind multi-factor authentication. Application secrets operate differently. They are often long-lived, embedded in code or configuration files, and passed between services automatically without any human in the loop. Because no person types these credentials in at runtime, it is easy to treat them as static artifacts rather than dynamic, sensitive assets that require the same care as any other access control mechanism.
The distinction matters because attackers know this gap exists. Leaked API keys and hardcoded tokens rank among the most common entry points for data breaches. A developer accidentally commits a database connection string to a public repository, a container image ships with credentials baked in, or a CI/CD pipeline logs an OAuth token in plaintext. Each of these scenarios exposes your system not because your perimeter defenses failed, but because no one treated the secret as something that needed active, ongoing protection.
The lifecycle every secret goes through
Every secret follows a predictable path from creation to deletion, and each stage introduces risk if you handle it carelessly. When you create a secret, you need to confirm it is strong enough to resist brute-force attempts and scoped to only the permissions the application actually needs. When you distribute it, you need a secure channel so it never travels in plaintext. When the application uses it, audit logging should capture every access event so you can reconstruct exactly which identity used the credential and when.

Rotation is the stage most teams skip, and it is where problems accumulate quietly over time. If you never rotate a secret, a compromised credential stays valid indefinitely. Modern secrets management tools automate rotation on a defined schedule, which means even if an attacker obtains a token, the window of exposure stays narrow. Finally, revocation and retirement close the lifecycle by ensuring old secrets stop working the moment they are no longer needed. Without a formal process for this last step, stale credentials pile up across your infrastructure and create shadow access points that are nearly impossible to audit after the fact.
What counts as a secret
Before you can manage secrets effectively, you need to know exactly what qualifies as one. A secret is any credential that grants a non-human identity access to a protected resource. That definition cuts across dozens of credential types that live inside modern software stacks. Part of applying any useful secrets management definition to your own environment means taking stock of every place where your applications authenticate to something else, because each one of those touchpoints produces at least one secret that needs active oversight.
Static credentials and API keys
API keys are the most familiar form of secret. When your application calls a third-party service, a payment processor, a mapping provider, or an EHR system, it sends an API key to confirm its identity and authorization level. Database passwords and connection strings fall into the same category. They sit inside configuration files or environment variables and rarely change unless something forces a rotation. Encryption keys and certificates also belong here. They protect data at rest and in transit, and a compromised encryption key can expose every record your system has ever stored.
A single hardcoded API key committed to a public repository can expose your entire data layer within hours, as automated scanners continuously comb public code hosts for exposed credentials.
SSH private keys round out the static credentials category. Your infrastructure teams use them to access servers and cloud instances, but automated deployment pipelines also use SSH keys to push code and run scripts without human involvement. Each of these credential types needs the same lifecycle controls: creation, secure distribution, rotation, and revocation.
Short-lived and dynamic secrets
Not every secret is static. OAuth access tokens are a prime example of short-lived credentials. When a SMART on FHIR application authenticates against EPIC, it receives a token that expires on a defined schedule. The application must manage that token securely for its lifespan and handle token refresh without exposing the credential in logs or memory. Service account tokens used by containers and cloud functions operate the same way. They are issued dynamically, scoped tightly, and should expire quickly. Managing dynamic secrets requires tooling that handles issuance and renewal automatically rather than relying on engineers to intervene manually each time a credential refreshes.
Why secrets management matters
Understanding the full secrets management definition goes beyond knowing what secrets are. You also need to understand what happens when you handle them poorly. Researchers routinely find thousands of valid API keys exposed in public repositories within hours of being committed, many granting access to production databases and cloud infrastructure. Exposed credentials are not a theoretical risk. They are a routine outcome when organizations treat secrets as configuration details rather than sensitive security controls that need active governance.
The real cost of a leaked credential
When an attacker gets hold of a live API key or OAuth token, the damage compounds quickly. They can extract data, impersonate legitimate services, pivot to connected systems, and plant persistent access mechanisms before your team detects anything unusual. For healthcare vendors, that chain of events can mean unauthorized access to protected health information, which triggers mandatory breach notification under HIPAA and potentially six-figure fines from the Office for Civil Rights.
A single exposed credential in a connected healthcare system can cascade into a full breach before your security team receives its first alert.
Reputation damage is harder to quantify but equally serious. Health systems are conservative buyers. If a vendor suffers a credential-related breach, procurement teams will pause contract negotiations, and existing customers may invoke termination clauses. The financial fallout from one leaked secret often exceeds the entire annual cost of implementing proper controls in the first place, which makes investing in credential governance an easy decision when you frame it against the alternative.
Compliance frameworks that require it
HIPAA does not use the phrase "secrets management," but its technical safeguard requirements map directly onto the practice. You must implement access controls, audit controls, and transmission security for any system that touches electronic protected health information. Managing OAuth tokens and API keys through a defined, documented process satisfies multiple safeguard categories at once and gives you concrete evidence to present during any compliance review.
SOC2 Type II audits evaluate whether your controls operate consistently over time, which means rotation logs, access audit trails, and revocation records all become audit evidence. If you cannot demonstrate that your application credentials follow a documented lifecycle, you will struggle to pass any meaningful security certification. Building these controls from the start is far cheaper than retrofitting them before an audit deadline or after a breach has already occurred.
How secrets management works
Any useful secrets management definition includes not just what secrets are but how the systems designed to protect them actually operate. At the center of most implementations sits a secrets vault, a hardened, encrypted store that holds credentials separately from your application code and configuration files. Instead of embedding a database password in a config file, your application requests it from the vault at runtime, which means the credential never touches source control and stays isolated behind its own access controls.
Centralized vaults and authentication
A secrets vault authenticates every request before it releases a credential. Your application proves its identity using a trusted mechanism, often a short-lived token issued by your cloud provider's identity service or an internal certificate authority. The vault then checks whether that identity has permission to access the specific secret being requested. If the request passes both checks, the vault returns the credential through an encrypted channel, logs the access event, and optionally issues a time-limited version that expires after a defined period. This chain of authentication, authorization, and auditing is what separates a vault from simply storing passwords in an environment variable.
Vaults that log every credential access give your security team a complete record of which service touched which secret and when, which is essential evidence during an incident investigation.
Secret injection and runtime delivery
Once a vault approves a request, it delivers the credential to your application through a process called secret injection. Rather than reading a static file, your application pulls the secret dynamically at startup or at the moment it needs to authenticate to another service. Common delivery mechanisms in containerized environments include:

- Sidecar containers: A companion container pulls secrets from the vault and makes them available to the main application through a shared volume.
- Init containers: A startup container fetches credentials before the main process launches, then exits cleanly.
- Agent processes: A vault agent running alongside your app handles token renewal and secret refresh automatically.
This approach means that even if an attacker gains access to your container's filesystem, they find no credential stored in plaintext. The secret existed in memory only for as long as the application needed it, and the vault's audit logs capture every access event regardless of what happens afterward.
Key practices that prevent secret sprawl
Secret sprawl happens when credentials multiply faster than your team can track them. Applications get deployed, tokens get issued, keys get copied into config files, and within months you have hundreds of credentials scattered across repositories, CI/CD pipelines, and cloud environments with no clear owner for any of them. Applying a disciplined secrets management definition to your workflows stops this pattern before it takes hold.
Enforce least privilege at the credential level
Every secret you issue should carry only the minimum permissions required for its specific function. A service that reads patient data from an API should receive a read-only token, not a token with write or admin access. When you scope credentials tightly, a leaked secret does limited damage on its own because it cannot reach anything beyond its narrow authorization boundary. Combine least privilege with short expiration windows, and the window of exposure for any individual credential shrinks further. Review permission scopes whenever a service changes its function, and revoke credentials that exceed what the current workload actually needs.
Automate rotation and set expiry by default
Manual rotation rarely happens on schedule. Engineers deprioritize it under deadline pressure, and static credentials end up persisting for years across environments. Automated rotation eliminates that dependency on human follow-through by cycling secrets on a defined schedule without requiring anyone to intervene. Set credentials to expire by default rather than treating expiration as an optional add-on. Most modern secrets vaults support rotation policies natively, and integrating them into your deployment pipeline means new credentials propagate to your applications automatically without downtime or manual updates.
Treat every non-expiring credential as a liability, not a convenience, because it is exactly the kind of long-lived asset attackers look for when they scan compromised environments.
Audit and scan continuously
Rotation and least privilege protect credentials that live inside your controlled infrastructure. They do nothing about secrets that accidentally leave your environment through code commits, log files, or improperly configured pipelines. Continuous scanning tools monitor your repositories and build artifacts for exposed credentials in real time, catching leaks before attackers do. Pair scanning with centralized audit logs from your vault so you maintain a complete record of every secret access event. That combination gives you both early warning when a credential escapes and full forensic visibility when you need to investigate why a system behaved unexpectedly.
Choosing tools and architectures
The right tool depends on where your infrastructure lives and how your team deploys applications. Cloud-native teams working on AWS, Azure, or Google Cloud have built-in secrets management services available through their existing provider, which simplifies integration and reduces operational overhead. If your stack spans multiple clouds or includes on-premises components, a self-hosted vault solution gives you consistent credential management across environments regardless of where each workload runs. Matching your tooling to your deployment model matters more than chasing the most feature-rich option available.
Cloud-native vs. self-hosted vaults
Cloud providers each offer a managed secrets service designed to integrate with their identity and access systems. AWS Secrets Manager handles automatic rotation and integrates natively with IAM roles, so your applications request credentials without managing long-term keys. Azure Key Vault follows the same pattern for Microsoft-centric stacks, and Google Cloud Secret Manager offers fine-grained IAM policies that tie directly into your existing Google Cloud identity controls. These managed options reduce your operational burden because the provider handles encryption, availability, and patching without requiring your team to run additional infrastructure.

If you run workloads across multiple cloud environments or need secrets accessible from on-premises systems, a self-hosted vault gives you a single control plane that no individual cloud provider can offer on its own.
Self-hosted solutions give you provider-agnostic credential management with deep customization options for authentication backends and policy enforcement. The tradeoff is operational complexity, since your team takes on full responsibility for running, scaling, and patching the vault infrastructure itself.
Matching architecture to your threat model
Your practical secrets management definition should reflect the actual risk profile of your application, not just what a generic template recommends. Applications that handle regulated data, including anything touching electronic health records or payment systems, need stricter rotation schedules and tighter audit requirements than a low-risk internal tool.
Map your credential controls to your data classification policy so the most sensitive secrets receive the highest level of protection, and review that mapping whenever your application scope changes or you add a new external integration. Letting your threat model drive your architecture choices keeps your controls proportional and your compliance posture defensible.
Secrets management for healthcare integrations
Healthcare vendors face a more demanding version of the same credential problem every software team encounters. When your application integrates with EPIC through SMART on FHIR, it constantly exchanges OAuth tokens, client credentials, and API keys with clinical systems that hold protected health information. Applying a clear secrets management definition to your healthcare integration stack is not optional. It is a direct requirement of the compliance frameworks your health system customers will audit you against before they sign any contract.
SMART on FHIR token handling
Every SMART on FHIR application your team deploys authenticates against EPIC using OAuth 2.0 access tokens that expire on a fixed schedule. Your application must request, store, use, and refresh those tokens without ever writing them to a log file, a config file, or any persistent store that lacks encryption at rest. The practical requirement is that your token lifecycle runs through a vault or a managed secrets layer, not through hardcoded values buried in your codebase or passed as plaintext environment variables.
Exposing an OAuth token that grants access to an EPIC environment does not just break your application. It creates a reportable HIPAA breach the moment that token connects to patient data.
Your FHIR client credentials, the client ID and client secret your application uses to initiate the OAuth flow, need the same treatment. Store them in a vault, scope them to the minimum permissions your integration requires, and rotate them on a defined schedule aligned with your security policy.
Vendor-managed platforms and credential responsibility
If you build your EPIC integration on a managed no-code platform rather than a custom stack, the platform operator takes on most of the credential lifecycle responsibility on your behalf. Your vendor should handle vault storage, token rotation, audit logging, and HIPAA-aligned access controls as part of the service. Before signing with any platform, confirm that the provider holds a Business Associate Agreement and can demonstrate SOC2 compliance with documented evidence of how they manage application credentials.
VectorCare's platform manages the complete credential lifecycle for SMART on FHIR integrations, including secure token handling, HIPAA-compliant storage, and audit trails, so your engineering team focuses on your core product instead of building and maintaining secrets infrastructure from scratch.
Final takeaways
The full secrets management definition covers far more than storing passwords in a secure location. It encompasses every stage of a credential's lifecycle, from creation and scoped distribution to automated rotation, continuous auditing, and formal revocation. When you apply these controls consistently, you reduce your exposure from leaked credentials, satisfy the technical safeguard requirements under HIPAA and SOC2, and give health system customers a defensible security posture to evaluate during procurement.
For healthcare vendors building SMART on FHIR integrations, credential governance is a prerequisite, not an enhancement. Your OAuth tokens, client secrets, and API keys connect directly to systems holding protected health information, which means every gap in your credential lifecycle carries both regulatory and business risk. Start building your EPIC integration on a platform that handles secrets management for you so your team can focus on delivering clinical value instead of engineering security infrastructure from scratch.
The Future of Patient Logistics
Exploring the future of all things related to patient logistics, technology and how AI is going to re-shape the way we deliver care.