Role Based Access Control Models Explained (NIST RBAC)


Role Based Access Control Models Explained (NIST RBAC)
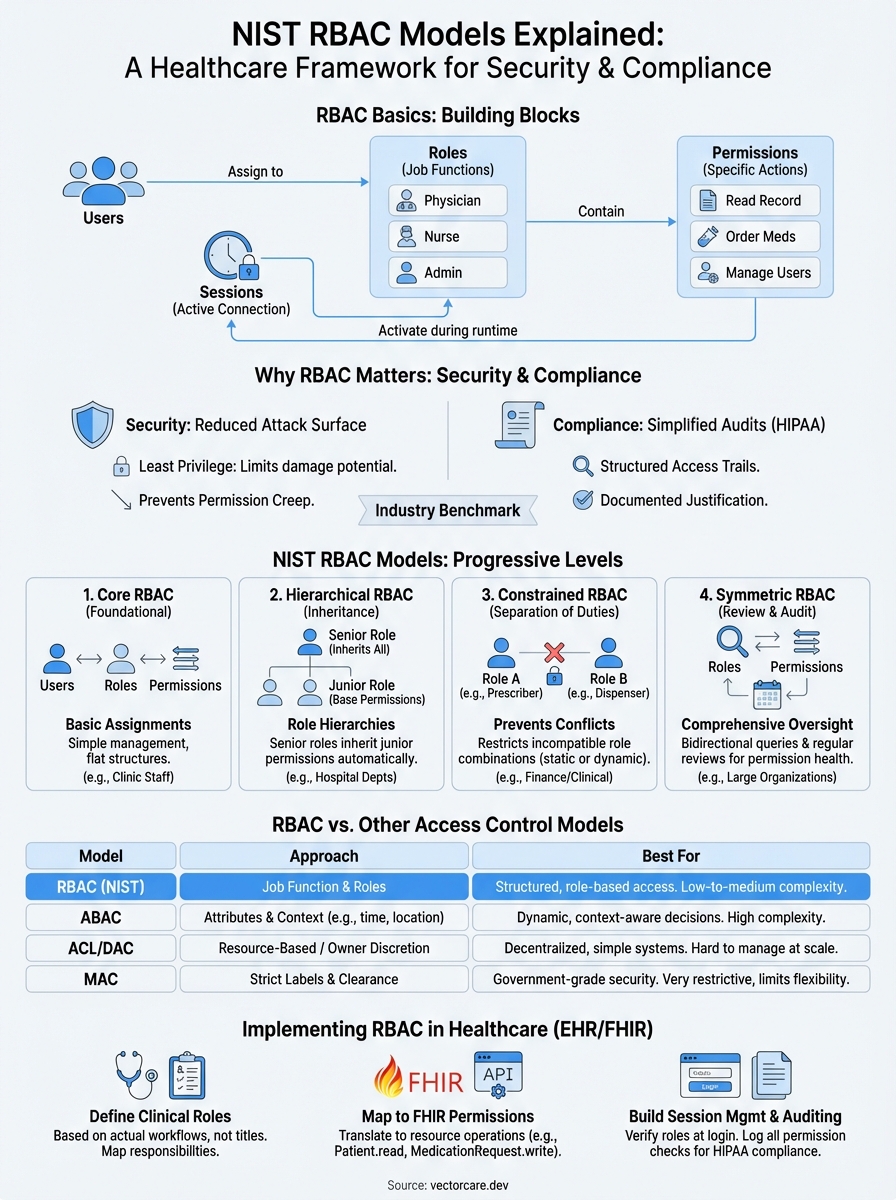
Healthcare applications handle some of the most sensitive data imaginable, patient records, diagnoses, treatment histories. Controlling who accesses what isn't optional; it's both a regulatory mandate and a core security practice. Role based access control models provide the systematic framework for managing these permissions, and NIST's standardized approach has become the industry benchmark for implementing RBAC correctly.
Understanding these models matters whether you're building internal systems or developing vendor applications that integrate with EHR platforms like EPIC. Each NIST level, Core, Hierarchical, and Constrained, adds specific capabilities and restrictions that address different organizational needs. From simple permission assignment to complex separation of duties requirements, choosing the right model prevents security gaps and compliance failures before they happen.
At VectorCare, we build these access control principles directly into our no-code SMART on FHIR platform, ensuring healthcare vendors can deploy HIPAA-compliant applications without architecting security frameworks from scratch. This article breaks down each NIST RBAC model: what it includes, how it differs from the others, and when to apply each level in your security strategy.
RBAC basics: roles, permissions, and sessions
Before you implement any role based access control models, you need to understand the three fundamental components that make RBAC work: roles, permissions, and sessions. These elements form the building blocks that determine who can do what in your system. You don't assign permissions directly to individual users; instead, you group permissions into roles and assign those roles to users based on their job functions.

Think of roles as permission containers that represent specific responsibilities within your organization. Permissions define the specific actions users can perform on resources. Sessions create the runtime connection between users and their assigned roles. When you configure RBAC properly, you establish a clear chain: users activate roles through sessions, which grant them the permissions needed to perform their duties.
Roles define job functions, not individuals
You create roles based on organizational responsibilities, not individual user names. A role represents what someone needs to do, such as "Nurse" or "Lab Technician," rather than who they are. This approach lets you assign multiple users to the same role without duplicating permission configurations across your system.
Healthcare applications typically implement roles that mirror clinical hierarchies and departmental structures. You might define an "Attending Physician" role with full patient record access, a "Resident" role with restricted modification permissions, and a "Medical Student" role with read-only capabilities. Each role contains the exact set of permissions required for that function, no more and no less.
When you structure roles around job functions instead of individuals, you simplify permission management and reduce configuration errors.
The key advantage appears when staff members change positions or departments. You simply reassign them to their new role instead of modifying individual permissions. This scalability makes RBAC practical for large healthcare organizations with hundreds or thousands of users.
Permissions control what actions users can perform
Permissions represent the granular access rights that control specific operations on specific resources. You define each permission as an operation-resource pair, such as "read patient demographics" or "modify lab orders." These permissions become the atomic units of access control in your system.
Your RBAC implementation maps permissions to system capabilities and data types. For an EHR integration, you create permissions for reading patient charts, updating medication lists, ordering diagnostic tests, and viewing imaging results. Each permission corresponds to a specific FHIR resource and operation type (read, write, create, delete).
You bundle related permissions together when you assign them to roles. A "Pharmacist" role might include permissions to view medication histories, submit prescription orders, and check drug interactions, but exclude permissions to modify diagnostic codes or access psychiatric notes. This bundling ensures users receive exactly the access they need without manual permission tracking.
Sessions link users to roles at runtime
Sessions create the active connection between users and their assigned roles during actual system use. When you log into an application, the system initiates a session that activates your assigned roles and their associated permissions. This activation model gives you flexible access control that adapts to different contexts and workflows.
You can configure RBAC to let users hold multiple roles simultaneously or switch between roles during a session. A physician who also serves as a department administrator might activate their "Physician" role for clinical work and their "Department Admin" role for scheduling and staff management. Sessions track which roles are currently active and enforce the appropriate permissions.
The session component also enables audit logging and compliance tracking. Your system records when users activate roles, what actions they perform under those roles, and when sessions terminate. This creates the detailed access trails that HIPAA and other regulations require for healthcare applications.
Why RBAC models matter for security and compliance
Healthcare organizations face constant pressure to protect patient data while maintaining operational efficiency. Role based access control models provide the structured approach you need to satisfy both requirements simultaneously. Without formalized RBAC, you rely on ad hoc permission decisions that create security gaps, audit failures, and regulatory violations. NIST's standardized models give you tested frameworks that reduce risk while supporting the complex access patterns healthcare workflows demand.
RBAC reduces your attack surface and limits data breaches
You minimize security risks when you implement proper role based access control models because they enforce the principle of least privilege automatically. Users receive only the permissions required for their specific job functions, which dramatically reduces the damage potential if credentials become compromised. An attacker who gains access to a nurse's account can't delete patient records or modify billing information if those permissions aren't included in the nurse role.
Data breaches in healthcare cost organizations an average of $10.93 million per incident, according to IBM's 2023 Cost of a Data Breach Report. Proper RBAC implementation cuts this exposure by limiting what any single compromised account can access. When you structure permissions around roles instead of individuals, you also eliminate the permission creep problem that occurs when users accumulate unnecessary access rights over time.
You create defensible security boundaries when each role contains only the minimum permissions needed for that function.
RBAC simplifies HIPAA and regulatory compliance
Your compliance obligations become manageable when you use standardized RBAC frameworks that map directly to regulatory requirements. HIPAA demands that covered entities implement access controls to ensure only authorized users can view protected health information. The NIST RBAC models provide the documented structure auditors expect to see, with clear role definitions, permission assignments, and separation of duties controls.
Compliance audits focus on demonstrating that you control access appropriately and maintain detailed access logs. RBAC gives you both capabilities by design. You document who has what access through role assignments, and you track all permission changes through role modification records. This structured approach satisfies regulatory requirements while reducing the manual effort needed to demonstrate compliance during audits.
State privacy regulations like the California Consumer Privacy Act also require that you limit data access to legitimate business purposes. RBAC models enforce this limitation automatically by restricting each role to permissions aligned with specific job responsibilities, creating the documented access justification that regulators require.
The three NIST RBAC rules you must follow
You implement role based access control models correctly only when you enforce NIST's three fundamental rules that govern how users, roles, and permissions interact. These rules define the mandatory constraints that prevent unauthorized access in any RBAC system, regardless of which model level you choose. NIST standardized these requirements to create consistent security boundaries across different implementations, and you must build them into your access control architecture from the beginning. Violating any of these rules creates security vulnerabilities that undermine your entire RBAC framework.
Rule 1: Users exercise permissions only through assigned roles
The role assignment rule requires that users can perform actions only by activating assigned roles during their sessions. You cannot grant permissions directly to users or allow them to assume roles they haven't been explicitly assigned. This rule forces all access control decisions through the role assignment process, which creates the audit trail and permission structure that makes RBAC effective.
Your system must verify role assignments before allowing any session activation. When a physician attempts to access patient records, your application checks whether the "Physician" role has been assigned to that user account. Without a valid assignment, the system denies access regardless of what the user claims their job function to be.
You maintain security boundaries when every permission flows through documented role assignments rather than individual user grants.
Rule 2: Users activate only their authorized roles
The role authorization rule ensures that users can activate only roles authorized for their account. Your RBAC implementation must maintain a definitive list of which roles each user can assume and enforce this list during session creation. This prevents users from escalating privileges by activating roles they shouldn't have access to, even if those roles exist in your system.
Healthcare applications enforce this rule by checking user credentials against role authorization databases before granting access. A nurse cannot activate the "Pharmacy Manager" role even if they discover it exists in the system, because that role wasn't authorized for their user account.
Rule 3: Permissions activate only through authorized role sessions
The permission authorization rule restricts users to exercising only the permissions authorized for their currently active roles. You configure each role with specific permission sets, and your system grants access to resources only when the user's active role includes that permission. This rule creates the direct link between job functions and access rights that defines RBAC.
Your access control checks validate permissions at every operation attempt. When a user tries to modify a lab order, your system verifies that their active role includes the "modify lab orders" permission before allowing the change.
Core RBAC model and when it works best
Core RBAC represents the foundational level of NIST's role based access control models, providing the essential components you need for basic permission management. This model includes user-role assignments, role-permission assignments, and session management, along with the three fundamental rules that govern all RBAC implementations. You implement Core RBAC when your organization needs straightforward access control without complex hierarchies or separation of duties requirements.
What Core RBAC includes and how it functions
Your Core RBAC implementation establishes the basic framework for assigning users to roles and mapping permissions to those roles. The model maintains three critical relationships: which users belong to which roles, which permissions each role grants, and which roles users activate during sessions. You don't get role hierarchies or constraint mechanisms at this level, just direct assignments that create clear permission boundaries.
Core RBAC gives you complete flexibility to assign multiple roles to individual users and multiple users to the same role. A physician working in both emergency medicine and cardiology can hold both the "Emergency Department Physician" and "Cardiologist" roles simultaneously, activating whichever role their current task requires. This many-to-many relationship between users and roles handles most basic healthcare access scenarios effectively.
You achieve substantial security improvements with Core RBAC alone because it eliminates direct user-to-permission assignments and creates manageable role structures.
When Core RBAC provides sufficient access control
Core RBAC works best for smaller healthcare organizations or departments with straightforward reporting structures and limited access complexity. Your clinic with 50 staff members and clear job functions probably doesn't need hierarchical inheritance or separation of duties constraints. You assign nurses to the "Nurse" role, physicians to the "Physician" role, and administrators to the "Administrative Staff" role, and the permission management remains simple.
Organizations with flat organizational structures benefit from Core RBAC's simplicity. When you don't have multiple management layers or complex approval workflows, the added capabilities of higher RBAC levels create unnecessary configuration overhead. Your urgent care center where everyone performs clearly defined functions without overlapping responsibilities fits this model perfectly.
Practical healthcare scenarios where Core RBAC succeeds
You implement Core RBAC effectively in single-department applications that don't require cross-functional access controls. A physical therapy clinic's scheduling system needs only basic roles: therapists who view and document sessions, front desk staff who manage appointments, and billing personnel who process insurance claims. Each role has distinct permissions without inheritance relationships or mutual exclusion requirements.
Vendor applications that integrate with EHR systems often rely on Core RBAC for initial deployments. Your remote patient monitoring tool might define roles for clinical reviewers, patient engagement coordinators, and system administrators, with each role receiving the specific permissions needed for their function without complex constraints or hierarchies.
Hierarchical RBAC model for role inheritance
Hierarchical RBAC builds on Core RBAC by adding role inheritance relationships that reflect organizational structures and reporting hierarchies. This model lets you define senior roles that automatically inherit all permissions from junior roles, eliminating redundant permission assignments and simplifying management as your access control needs grow. You implement Hierarchical RBAC when your organization has clear management layers where supervisors need all the capabilities of their subordinates plus additional administrative permissions.
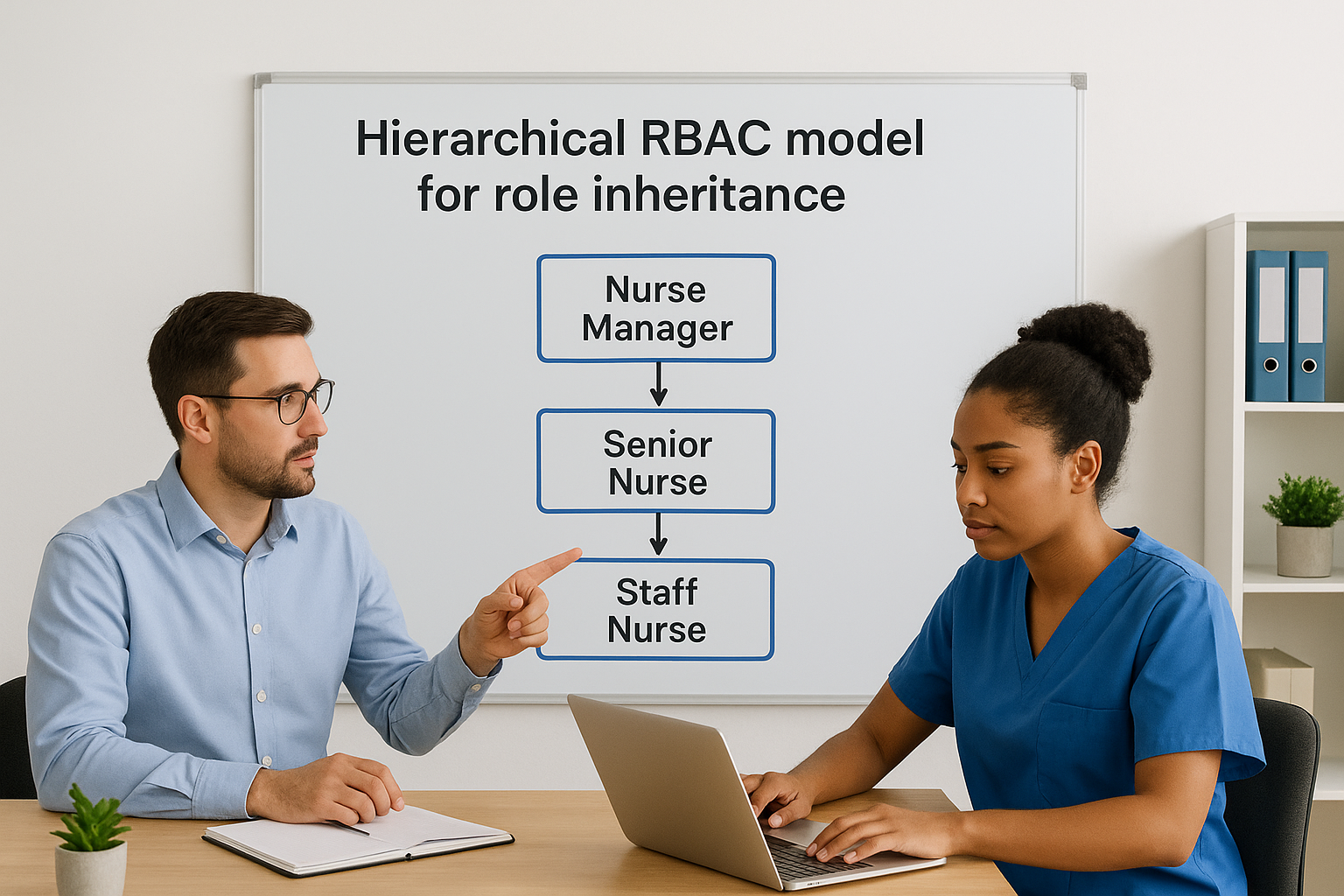
How role inheritance creates permission hierarchies
You establish inheritance by defining parent-child relationships between roles, where senior roles automatically acquire all permissions assigned to junior roles. When you create a "Senior Nurse" role as a parent of the "Staff Nurse" role, the senior nurse inherits every permission the staff nurse has, plus any additional permissions you assign specifically to the senior role. This inheritance flows down multiple levels, so a "Nurse Manager" role inherits from "Senior Nurse," which inherits from "Staff Nurse."
Your system enforces these hierarchies during permission checks by traversing the inheritance tree. When a user with the "Nurse Manager" role attempts an action, your access control mechanism verifies permissions assigned directly to that role and all permissions inherited from subordinate roles in the hierarchy. This automatic inheritance reduces configuration effort while maintaining security boundaries.
You eliminate permission duplication when inheritance handles the common permissions shared across organizational levels.
Practical benefits of hierarchical role structures
Healthcare organizations benefit from hierarchical role based access control models because clinical hierarchies naturally align with permission inheritance. Your attending physicians need everything residents can do plus supervisory capabilities like approving treatment plans and signing off on documentation. Instead of manually assigning dozens of individual permissions to the attending role, you establish it as a parent role that inherits from the resident role automatically.
Hierarchical RBAC reduces administrative overhead when you modify permissions. If you add a new permission to the "Staff Nurse" role, every senior role above it in the hierarchy inherits that permission immediately without additional configuration. This cascading effect keeps your permission structure consistent across organizational levels while adapting quickly to changing requirements.
Healthcare scenarios where hierarchical RBAC excels
You implement hierarchical models in hospital systems with multiple clinician levels and clear reporting structures. Your emergency department might define roles for medical students, residents, fellows, and attending physicians, where each level inherits permissions from the level below while adding supervisory capabilities. Medical students get read-only access, residents add documentation permissions, fellows gain procedure authorization rights, and attendings inherit everything plus final approval authority.
Departmental applications benefit from hierarchical structures when department heads need broader access than staff members. Your radiology department creates a hierarchy where radiologists can interpret images, senior radiologists can approve reports, and the department chief inherits both capabilities while adding scheduling and resource management permissions that support administrative responsibilities.
Constrained RBAC model for separation of duties
Constrained RBAC extends Hierarchical RBAC by adding constraint mechanisms that prevent conflicts of interest and enforce separation of duties policies. This model introduces both static and dynamic restrictions that limit which role combinations users can hold or activate simultaneously. You implement Constrained RBAC when your organization needs to prevent users from accumulating permissions that create fraud risks, compliance violations, or security vulnerabilities through conflicting responsibilities.
Static separation of duties constraints
You configure static constraints to prevent users from receiving mutually exclusive roles during the assignment process. Your system blocks these assignments at configuration time, refusing to assign a user to the "Medication Prescriber" role if they already hold the "Pharmacy Dispenser" role. This proactive approach stops conflicts before they enter your access control structure.
Healthcare organizations use static constraints to enforce regulatory requirements that prohibit combining certain clinical and financial responsibilities. Your billing department staff cannot receive roles that include clinical documentation rights, preventing scenarios where employees might alter patient records to justify billing decisions. Static constraints create permanent barriers between incompatible functions.
You eliminate entire categories of fraud and compliance risk when static constraints prevent problematic role combinations from existing in your system.
Dynamic separation of duties enforcement
Dynamic constraints allow users to hold multiple roles but prevent them from activating conflicting roles within the same session. Your pharmacist might have both "Medication Dispenser" and "Inventory Auditor" roles assigned, but your system blocks simultaneous activation of both during a single session. This flexibility lets staff perform different functions at different times while maintaining separation when conflicts matter.
You implement dynamic constraints when operational needs require role flexibility but security demands prevent concurrent use. Your clinical research coordinator can review patient charts in one session and approve research protocols in another, but cannot perform both activities simultaneously to avoid data manipulation risks during study recruitment.
Healthcare scenarios requiring constraint-based RBAC
You deploy Constrained RBAC in financial and clinical applications where regulatory bodies mandate separation of duties. Your revenue cycle management system enforces constraints between roles that create charges, roles that verify medical necessity, and roles that submit insurance claims. These role based access control models prevent individuals from controlling transactions end-to-end, which reduces billing fraud opportunities.
Clinical trial systems benefit from constraint mechanisms that separate patient enrollment responsibilities from outcome assessment duties. Your research application blocks users with enrollment permissions from activating data analysis roles, ensuring blind study protocols remain intact and preventing bias in clinical results.
Symmetric RBAC and role and permission review
Symmetric RBAC represents the most comprehensive NIST model by combining all previous levels with additional review and administration functions. This model adds capabilities for examining existing role and permission assignments, identifying access control inconsistencies, and maintaining the health of your RBAC implementation over time. You implement Symmetric RBAC when your organization needs systematic oversight mechanisms that detect permission drift, unauthorized assignments, and configuration errors that accumulate as your system evolves.
What symmetric RBAC adds to constrained models
You gain bidirectional query capabilities when you implement Symmetric RBAC that let you examine role based access control models from multiple perspectives. Standard RBAC lets you ask "what permissions does this role have?" but Symmetric RBAC also answers "which roles grant this permission?" and "which users can perform this action?" These reverse lookups provide the visibility you need to audit access patterns and identify potential security issues.
Your system maintains indexes that support efficient queries in both directions across the user-role-permission relationships. When you investigate a potential data breach, you can quickly determine which roles include access to compromised resources and which users hold those roles. This investigative capability reduces incident response time and helps you contain security events before they escalate.
Role review processes that prevent permission creep
You conduct systematic role reviews by examining role assignments periodically to verify they still match current job responsibilities. Staff members change positions, departments reorganize, and responsibilities shift, but role assignments often remain unchanged. Regular reviews identify users who retained outdated roles after job changes or accumulated excessive permissions through multiple assignments.
Healthcare organizations schedule quarterly or annual role audits where department managers confirm that assigned roles align with actual job functions. Your review process flags accounts with unusual role combinations, dormant accounts that still hold active roles, and contractor accounts that exceeded their project timelines. Symmetric RBAC's query functions make these reviews efficient by generating reports that highlight potential issues automatically.
You maintain security hygiene when regular role reviews remove unnecessary access before it creates compliance violations or security incidents.
Permission review mechanisms for access control health
You analyze permission assignments across roles to identify redundant or conflicting configurations that indicate structural problems in your RBAC design. Symmetric RBAC helps you detect scenarios where multiple roles grant the same permission set, suggesting role consolidation opportunities, or where role permissions overlap in ways that violate separation of duties policies.
Permission reviews also reveal when configuration changes created unintended access paths. Your audit process might discover that modifying the "Lab Technician" role inadvertently granted database administration permissions, or that a new role bypasses established approval workflows. These systematic checks protect your access control framework from degrading as requirements change and configurations accumulate.
RBAC vs ABAC, ACL, DAC, and MAC
You choose between different access control approaches based on your security requirements and operational complexity. While role based access control models offer structured permission management through job functions, other models take fundamentally different approaches to granting access. Understanding how RBAC compares to Attribute-Based Access Control, Access Control Lists, Discretionary Access Control, and Mandatory Access Control helps you select the right framework for your healthcare applications.
RBAC versus ABAC for dynamic access decisions
ABAC evaluates multiple attributes at access time instead of relying on predefined role assignments. Your system checks user attributes (department, clearance level), resource attributes (classification, owner), and environmental attributes (time of day, location) to make real-time access decisions. This flexibility handles complex scenarios that RBAC struggles with, like granting access only during business hours or restricting sensitive data to users physically located within your facility.
You implement RBAC when your access patterns align with organizational roles and change infrequently. ABAC works better when you need context-aware decisions that consider multiple factors beyond job function. Healthcare applications often combine both approaches, using RBAC for baseline permissions and ABAC rules for additional restrictions based on patient relationships or data sensitivity levels.
You gain flexibility with ABAC but accept increased complexity in policy management and performance overhead compared to RBAC's straightforward role assignments.
ACL and DAC approaches to permission management
Access Control Lists assign permissions directly to resources rather than organizing them through roles. Your patient record includes an ACL specifying exactly which users can read or modify it. DAC extends this concept by letting resource owners decide who gets access, creating decentralized permission management without centralized role structures.
You avoid ACLs in enterprise healthcare systems because they create permission sprawl that becomes unmanageable at scale. When every resource has its own access list, you lose the centralized visibility and consistent policy enforcement that RBAC provides through role-based structures. DAC compounds this problem by distributing permission decisions across multiple data owners.
MAC for government-grade security requirements
MAC implements security labels and clearance levels that users cannot override or modify. Your system administrator assigns classification levels to data and clearance levels to users, and the operating system enforces access automatically based on these predetermined labels. Users cannot share data with unauthorized individuals even if they want to, because MAC policies override user discretion completely.
Healthcare organizations rarely implement pure MAC because it restricts the clinical flexibility that patient care demands. You choose MAC only when regulatory requirements mandate strict classification controls that prevent any unauthorized disclosure, such as military medical facilities handling classified patient information.
How to implement RBAC in healthcare EHR apps
You build effective role based access control models in EHR applications by starting with your actual clinical workflows rather than theoretical security frameworks. Your implementation needs to align with how healthcare staff actually work: physicians moving between multiple departments, nurses covering different units, and specialists consulting across patient populations. Begin by documenting existing job functions and the data access each requires, then translate those patterns into roles that your SMART on FHIR application can enforce consistently.
Start with clear role definitions based on clinical workflows
You define roles by analyzing specific clinical responsibilities rather than copying generic healthcare titles. Your "Emergency Department Physician" role needs different permissions than "Primary Care Physician" even though both are doctors, because emergency physicians require rapid access to comprehensive patient histories without prior relationships while primary care physicians work within established panels. Map out what data each role accesses, what actions they perform, and which workflows they participate in before creating any technical configurations.
Interview clinical staff to understand edge cases that standard role definitions miss. Your implementation might need roles for physicians who also serve as department administrators, nurses who handle both patient care and quality improvement documentation, or billing specialists who require limited clinical data access for coding accuracy. These hybrid scenarios determine whether you need Core RBAC's flexibility or Constrained RBAC's separation controls.
Map permissions to FHIR resources and operations
You translate role requirements into specific FHIR permissions that your application enforces at the API level. Each permission corresponds to a resource type (Patient, Observation, MedicationRequest) and an operation (read, write, create, delete). Your "Lab Technician" role might include permissions to read Patient demographics, create Observation resources for test results, and update ServiceRequest statuses, but exclude permissions to modify diagnostic codes or medication orders.
You prevent authorization bypass vulnerabilities when permissions map directly to the FHIR resources your application accesses rather than relying on UI-level restrictions alone.
Configure SMART scopes that match your role permissions so your application requests only the access it needs during EHR authorization. Your roles determine which scopes to request: patient/Observation.read for roles viewing lab results, user/MedicationRequest.write for roles that submit prescriptions.
Build session management with audit logging
You implement session controls that activate roles when users authenticate and track every permission check throughout their session. Your application validates role assignments against your authorization database before granting any FHIR resource access, creating detailed logs that record which user, which role, what resource, and what action occurred. These logs satisfy HIPAA audit requirements while providing the evidence you need to investigate security incidents or unusual access patterns.
Configure session timeouts that match clinical workflows without creating security gaps. Your emergency department application might allow longer sessions than scheduled clinic systems because interruptions occur frequently during acute care situations.
Next steps
You implement role based access control models by selecting the NIST level that matches your security requirements and organizational complexity. Start with Core RBAC if you need straightforward permission management, add Hierarchical RBAC when your clinical structure includes supervisory roles, or deploy Constrained RBAC when separation of duties matters for compliance. Document your role definitions, map permissions to FHIR resources, and build comprehensive audit logging before launching your application.
Healthcare vendors building SMART on FHIR applications face significant technical overhead when implementing RBAC from scratch. Your team needs to architect session management, configure OAuth flows, handle permission checks across FHIR resources, and maintain compliance with HIPAA security requirements. VectorCare's no-code platform handles these complexities automatically, letting you deploy EPIC-integrated applications with built-in RBAC in weeks rather than months. Focus your engineering resources on your core product instead of recreating access control infrastructure.
The Future of Patient Logistics
Exploring the future of all things related to patient logistics, technology and how AI is going to re-shape the way we deliver care.