HIPAA Privacy Rule Overview: PHI, Rights, And Disclosures


HIPAA Privacy Rule Overview: PHI, Rights, And Disclosures
Every healthcare vendor building applications that touch patient data needs a solid HIPAA Privacy Rule overview before writing a single line of code, or configuring a single workflow. Whether you're developing a remote patient monitoring solution, a clinical decision support tool, or any service that integrates with EHR systems like EPIC, understanding what's protected and who's responsible isn't optional. It's the foundation of compliant healthcare technology.
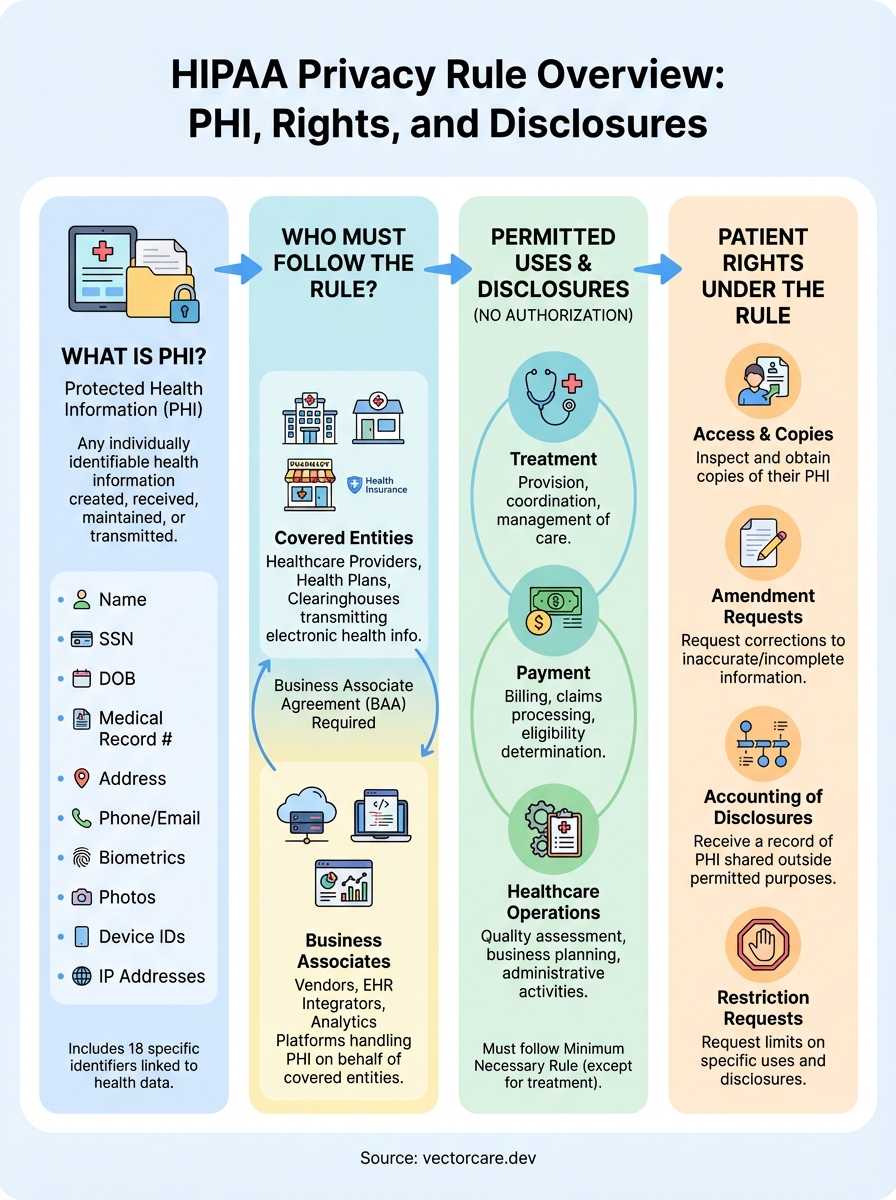
The Privacy Rule establishes national standards for protecting individuals' medical records and other personal health information. It defines what counts as Protected Health Information (PHI), identifies which organizations qualify as covered entities, outlines when and how data can be shared, and grants patients specific rights over their own health records. For healthcare vendors seeking integration with health systems, this knowledge directly impacts product design, partnership agreements, and your ability to secure contracts with hospitals and clinics.
At VectorCare, we build HIPAA and SOC2 compliance into every SMART on FHIR application our platform generates, but compliance starts with understanding the rules themselves. This guide breaks down the Privacy Rule's core components: the information it protects, the entities it governs, permitted disclosures, and patient rights you'll need to support in any EHR-integrated solution.
Why the HIPAA Privacy Rule exists
Before 1996, healthcare data lived in a legal gray zone where no federal standard existed for protecting patient information. Your medical records could move between providers, insurers, and billing companies without your knowledge or consent. State laws varied wildly, creating situations where information protected in one state became freely shareable across state lines. Healthcare vendors, insurers, and providers operated under inconsistent rules that left patients vulnerable and organizations uncertain about their legal obligations.
The healthcare privacy problem before HIPAA
The shift to electronic health records in the 1990s accelerated these privacy concerns. Paper records stayed physically locked in filing cabinets, but digital systems allowed instant copying and transmission across networks. Healthcare organizations began sharing data electronically for legitimate purposes like billing and care coordination, but the same technology enabled unauthorized access and misuse. Patients had no reliable way to know who accessed their records, why information was shared, or how to correct errors.
Insurance companies could deny coverage based on pre-existing conditions discovered through health records, and employers sometimes accessed employee medical information without consent. Pharmacies sold prescription data to marketing firms, and researchers accessed patient records without oversight. The lack of federal protection meant that sensitive diagnoses, treatment plans, and test results received less legal protection than video rental histories under existing privacy laws.
Without standardized rules, healthcare vendors building technology solutions faced different requirements in every state, making national deployment nearly impossible.
What the Privacy Rule accomplished
Congress passed the Health Insurance Portability and Accountability Act in 1996, directing the Department of Health and Human Services to create privacy regulations if Congress didn't act first. When legislative negotiations stalled, HHS issued the Privacy Rule in 2000, establishing the first comprehensive federal protection for health information. The rule took effect in 2003 for most covered entities, creating uniform standards that applied nationwide regardless of state boundaries.

The Privacy Rule accomplished three critical objectives for healthcare technology. First, it defined exactly what information counts as protected, removing ambiguity about which data elements require safeguards. Second, it established clear rules for when organizations can share patient information without permission, standardizing workflows for treatment, payment, and healthcare operations. Third, it granted patients enforceable rights to access their own records, request corrections, and receive accounting of disclosures.
For healthcare vendors building EPIC integrations or other EHR-connected solutions, this standardization made compliance predictable. You now follow one set of federal rules instead of navigating fifty different state requirements. The Privacy Rule doesn't prevent you from building innovative healthcare technology; it creates boundaries that protect both patients and vendors from liability. Understanding this HIPAA privacy rule overview helps you design applications that health systems will actually adopt, because you've built privacy protection into your architecture from day one rather than retrofitting compliance later.
Who must follow the Privacy Rule
The Privacy Rule doesn't apply to everyone who touches healthcare data. HHS defines specific organization types that must comply with these standards, and if you're building healthcare technology, understanding where you fit in this structure determines your compliance obligations and contractual relationships.
Covered entities and their obligations
Healthcare providers who transmit health information electronically qualify as covered entities under the Privacy Rule. This includes hospitals, clinics, doctors, psychologists, dentists, nursing homes, and pharmacies that submit electronic claims, use electronic health records, or send electronic prescriptions. Your health system customers fall into this category, which is why they require vendors to sign Business Associate Agreements before integrating any technology that accesses PHI.
Health plans also qualify as covered entities. These organizations include health insurance companies, HMOs, Medicare, Medicaid, employer-sponsored health plans, and government programs that pay for healthcare. If your healthcare solution processes claims data, coordinates benefits, or determines coverage eligibility, you'll interact with covered entities on both the provider and payer sides.
Healthcare clearinghouses round out the covered entity list. These organizations process nonstandard health information they receive from other entities into standard formats, or vice versa. Billing services and community health information systems often function as clearinghouses. Most healthcare vendors building EPIC integrations won't qualify as clearinghouses themselves, but you should recognize this category when mapping your data flows.
Business associates and the vendor relationship
If you build technology that creates, receives, maintains, or transmits PHI on behalf of a covered entity, you become a business associate under HIPAA. This classification applies to most healthcare vendors developing EHR integrations, analytics platforms, or remote monitoring solutions. You must comply with the Privacy Rule even though you're not a covered entity yourself.

Business associates face the same penalties as covered entities for Privacy Rule violations, making compliance equally critical regardless of your organization type.
When you deploy a SMART on FHIR application through VectorCare that pulls patient data from EPIC, you're functioning as a business associate. Your contract with each health system requires a Business Associate Agreement that specifies your privacy obligations, permitted uses of PHI, and security safeguards. This HIPAA privacy rule overview matters because it defines exactly what you can and cannot do with the data flowing through your application, affecting everything from feature design to data retention policies.
What counts as PHI under HIPAA
Protected Health Information (PHI) includes any individually identifiable health information that a covered entity or business associate creates, receives, maintains, or transmits in any form. Your application touches PHI the moment it accesses patient names, medical record numbers, diagnoses, lab results, or treatment plans from an EPIC system. The Privacy Rule protects this information whether it's stored electronically, on paper, or communicated verbally between providers.
The key word is "identifiable." Information qualifies as PHI when it relates to an individual's past, present, or future physical or mental health, the provision of healthcare to that individual, or payment for healthcare, and it identifies the individual or provides a reasonable basis to identify them. This HIPAA privacy rule overview emphasizes that the linkage between health data and identity triggers protection requirements.
The 18 HIPAA identifiers
HHS specifies 18 data elements that make health information identifiable under the Privacy Rule. These identifiers include names, geographic subdivisions smaller than a state (addresses, cities, ZIP codes with fewer than 20,000 people), dates directly related to an individual (birth dates, admission dates, discharge dates, death dates), telephone numbers, fax numbers, email addresses, Social Security numbers, medical record numbers, health plan beneficiary numbers, account numbers, certificate or license numbers, vehicle identifiers, device identifiers and serial numbers, web URLs, IP addresses, biometric identifiers (fingerprints, voiceprints), full-face photographs, and any other unique identifying number or code.
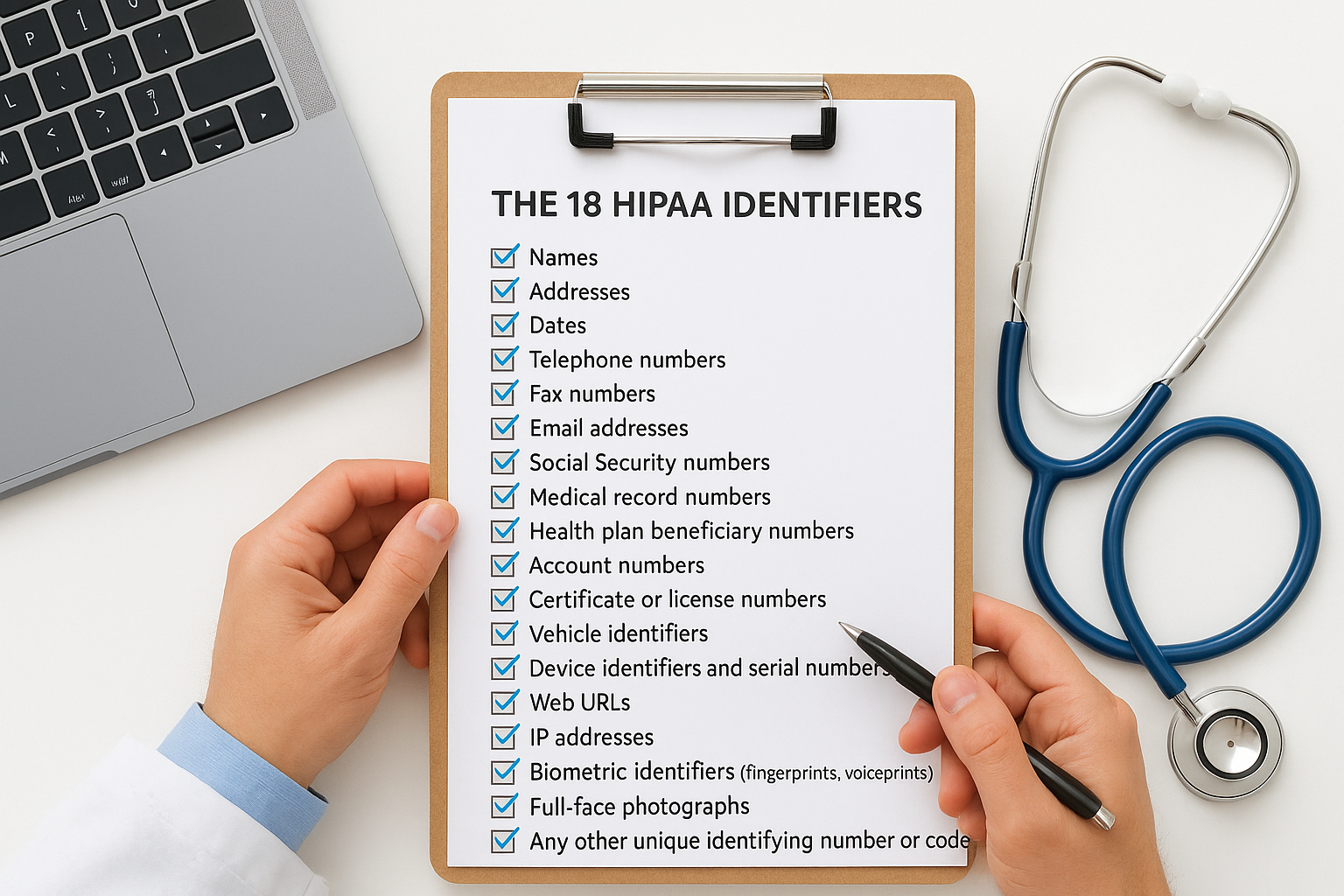
Your SMART on FHIR application pulling data from EPIC will encounter multiple identifiers in every patient record. A typical encounter note contains the patient's name, medical record number, date of birth, and often their address and phone number. Lab results include specimen collection dates and medical record numbers. Each of these elements triggers Privacy Rule protections when combined with health information.
Any single identifier from the list of 18, when linked to health information, creates PHI that requires the full set of Privacy Rule safeguards and patient rights.
De-identification and the safe harbor method
You can remove information from Privacy Rule coverage through proper de-identification, which eliminates all 18 identifiers and ensures no reasonable basis exists to identify individuals. The safe harbor method requires removing all listed identifiers and certifying that you cannot re-identify individuals using remaining information. This approach lets you use healthcare data for research, analytics, or product development without triggering PHI restrictions, but the burden falls on you to demonstrate complete de-identification before treating data as unrestricted.
When you can use or share PHI without permission
The Privacy Rule permits specific uses and disclosures of PHI without obtaining patient authorization, recognizing that healthcare requires routine data sharing for legitimate purposes. These permitted disclosures balance patient privacy with practical healthcare delivery, allowing providers and business associates to operate efficiently while maintaining baseline protections. Understanding these exceptions helps you design workflows that comply with the Privacy Rule without creating unnecessary friction in clinical processes.
Your SMART on FHIR application can access and use PHI for treatment, payment, and healthcare operations without asking each patient for permission every time. This HIPAA privacy rule overview shows that these three categories cover most routine healthcare activities, from coordinating care between specialists to processing insurance claims. Health systems expect vendors to support these workflows without introducing authorization barriers that slow down clinical decision-making.
Treatment, payment, and healthcare operations
Treatment includes any provision, coordination, or management of healthcare and related services by healthcare providers. When a physician orders lab tests through your application, views results from another department, or refers a patient to a specialist, these activities qualify as treatment. Your application can pull patient data from EPIC to display relevant history, medication lists, or prior imaging results without obtaining separate patient consent, because this information directly supports clinical care.
Payment encompasses activities that health plans and providers undertake to obtain reimbursement for healthcare services. This includes determining eligibility, processing claims, reviewing medical necessity, conducting utilization review, and coordinating benefits. Healthcare vendors building revenue cycle solutions or billing integrations operate under this exception, accessing diagnosis codes, procedure codes, and treatment documentation needed to generate and submit claims.
Healthcare operations cover administrative, financial, legal, and quality improvement activities necessary to run a healthcare organization. This broad category includes quality assessment, case management, conducting training programs, accreditation activities, business planning, customer service, and fraud detection. Your analytics solution measuring clinical outcomes or decision support tool evaluating care protocols falls under healthcare operations when deployed at a covered entity.
The treatment, payment, and operations exceptions let you build functional healthcare applications without requiring authorization workflows that would make your technology unusable in real clinical settings.
Required disclosures and public interest activities
The Privacy Rule mandates disclosure in two specific situations regardless of patient preferences: when patients request access to their own PHI, and when HHS conducts compliance investigations or enforcement actions. You must provide patients their records when they exercise their access rights, and you must cooperate with HHS audits examining your Privacy Rule compliance.
Public interest activities create additional permission-free disclosure categories for situations that serve broader societal needs. These include reporting to public health authorities for disease surveillance, disclosing information about abuse or neglect to appropriate authorities, providing information to law enforcement under specific circumstances, and sharing data required by judicial or administrative proceedings. Your application might encounter these scenarios when health systems use your technology to report communicable diseases or respond to subpoenas.
When you need patient authorization
The Privacy Rule requires you to obtain written patient authorization before using or disclosing PHI for purposes that fall outside treatment, payment, healthcare operations, and the specific exceptions outlined above. This authorization requirement protects patients from unexpected or unwanted uses of their health information, particularly in situations where commercial interests or non-healthcare purposes drive the disclosure. Your healthcare application must build authorization workflows into features that trigger these requirements, capturing patient consent before accessing or sharing data in ways that exceed permitted exceptions.
What authorization must include
Valid authorization under HIPAA requires specific elements and statements that patients must understand before signing. The document must describe the information you plan to use or disclose in sufficient detail, identify who will receive the information, state the purpose of the disclosure, include an expiration date or event, and inform patients of their right to revoke authorization at any time except when you've already acted based on the authorization. You must also explain whether treatment, payment, enrollment, or eligibility depends on providing authorization.
Authorization forms need plain language that patients can actually understand, not legal jargon that obscures what you're requesting. You must provide patients with a signed copy of their authorization, and you cannot condition healthcare services on authorization except in limited circumstances like research studies where the research activities and healthcare services are intertwined. Your SMART on FHIR application pulling data for purposes beyond direct patient care needs these authorization workflows built into the user experience.
Marketing, research, and sale of PHI
Marketing communications require authorization unless they describe health-related products or services you currently provide or occur face-to-face. If you sell patient data to pharmaceutical companies for targeted advertising or receive payment for sending promotional materials, you need explicit patient authorization that discloses the financial arrangement. This HIPAA privacy rule overview shows that even legitimate business activities trigger authorization requirements when they cross from healthcare operations into commercial promotion.
Authorization requirements prevent you from monetizing patient data or conducting marketing campaigns without explicit patient knowledge and consent, protecting individuals from commercial exploitation of their health information.
Research activities outside of treatment operations typically require authorization unless you obtain a waiver from an Institutional Review Board or use properly de-identified data. Selling PHI to third parties always requires authorization that specifically states you'll receive payment in exchange for the information, making patients aware that their data has commercial value you're extracting.
The minimum necessary rule and common exceptions
The Privacy Rule requires you to make reasonable efforts to limit PHI use and disclosure to the minimum necessary to accomplish your intended purpose. This means you don't pull every data element from an EPIC system when your application only needs specific fields to function. Your SMART on FHIR application should request access to diagnosis codes and medication lists if that's what supports your clinical decision logic, not demographics, insurance information, and full encounter histories that sit unused in your database.
What minimum necessary means in practice
You must review your data requests and identify which specific data elements your application genuinely needs to perform its intended function. If you're building a remote patient monitoring solution that tracks vital signs and alerts providers to concerning trends, you need patient identifiers, relevant diagnoses, current medications that affect those vital signs, and contact information. You don't need psychiatric history, genetic testing results, or unrelated specialist notes that have no connection to the monitoring parameters you're tracking.
This HIPAA privacy rule overview applies the minimum necessary standard to both uses within your organization and disclosures to external parties. Your internal teams should access only the PHI necessary for their specific job functions. Developers debugging application errors need test data or properly de-identified information, not production databases containing real patient records. Support staff resolving a billing inquiry need the specific encounter in question, not full medical histories spanning years.
Exceptions to the minimum necessary standard
The Privacy Rule carves out significant exceptions where minimum necessary doesn't apply, recognizing that certain activities require broader information access. You can disclose any and all relevant PHI to healthcare providers for treatment purposes without analyzing what's minimally necessary. When your application shares patient data between an emergency department and a cardiologist coordinating care, you don't restrict the information flow beyond what clinical judgment determines is relevant.
The minimum necessary rule doesn't limit disclosures made to patients themselves, to HHS during compliance reviews, or when disclosures are required by law.
Disclosures you make pursuant to patient authorization also escape minimum necessary restrictions. Patients can authorize release of their complete medical records to attorneys, family members, or other third parties, and you honor that authorization without second-guessing whether all disclosed information is truly necessary. Research activities operating under IRB-approved protocols determine their own data requirements within the scope of the approved research plan rather than applying minimum necessary analysis to each data element.
Patient rights under the Privacy Rule
The Privacy Rule grants patients six specific rights that your healthcare application must support when you build SMART on FHIR integrations or other EHR-connected solutions. These rights shift control back to individuals whose health information you access, process, or store, requiring you to implement technical capabilities and operational procedures that honor patient requests. Health systems evaluating your technology expect these features built into your platform, not bolted on as afterthoughts when compliance questions arise during contract negotiations.

Access and amendment rights
Patients hold the right to inspect and obtain copies of their PHI in your designated record sets, which typically include medical records, billing records, and enrollment information. You must provide access within 30 days of receiving a written request, or 60 days if records are stored off-site, with one 30-day extension permitted if you provide written explanation for the delay. Your application needs workflows that generate patient-requested records in the format they prefer when reasonably producible, whether that's electronic files, paper copies, or direct transmission to specified recipients.
The amendment right lets patients request corrections to inaccurate or incomplete information in their records. You can deny amendment requests if the information is accurate and complete, if you didn't create the information, if patients aren't entitled to access the PHI, or if the record isn't part of your designated record set. Your application must track amendment requests and either update records accordingly or document the reason for denial, then provide patients with written explanations and the opportunity to submit statements of disagreement.
Supporting patient access and amendment rights requires technical infrastructure that extracts, formats, and secures PHI for patient distribution while tracking all requests and responses for compliance documentation.
Disclosure accounting and restriction requests
Patients can request an accounting of disclosures you made during the six years before their request date, excluding disclosures for treatment, payment, healthcare operations, disclosures made pursuant to authorization, and several other categories. This HIPAA privacy rule overview shows that you must track and report who received PHI, when disclosures occurred, and the purpose of each disclosure that falls outside the exceptions. Your SMART on FHIR application needs logging mechanisms that capture this information automatically rather than relying on manual documentation that inevitably contains gaps.
The restriction right allows patients to request limits on how you use or disclose their PHI for treatment, payment, or healthcare operations. You can accept or refuse most restriction requests, but you must honor requests to restrict disclosures to health plans when patients pay out of pocket in full for healthcare items or services, and the disclosure isn't otherwise required by law.
Notices, documentation, and required policies
The Privacy Rule imposes specific documentation and notification obligations that your organization must fulfill when operating as a covered entity or business associate. You cannot simply implement privacy protections and assume compliance; you must formally document your practices, policies, and procedures in writing, then make certain information available to patients and HHS upon request. These requirements create an audit trail that demonstrates your commitment to protecting PHI and provides patients with transparency about how you handle their health information.
Notice of Privacy Practices requirements
You must provide patients with a Notice of Privacy Practices (NPP) that explains in plain language how you use and disclose their PHI, their rights under HIPAA, and your legal duties regarding their information. This document needs to describe the types of uses and disclosures you're permitted to make without authorization, examples of treatment, payment, and healthcare operations activities, and any uses requiring authorization. Your NPP must state that patients can file complaints with you and HHS if they believe their privacy rights were violated.
Healthcare providers must make the NPP available at their first service delivery to patients and post it prominently in their facility and on their website. You need patients to acknowledge receipt in writing when feasible, and you must retain these acknowledgments for six years. Your notice must explain how patients can access their records, request amendments, obtain accounting of disclosures, and request restrictions or confidential communications.
Your Notice of Privacy Practices serves as the primary communication tool that sets patient expectations about privacy protections and establishes the legal framework for how you handle their health information throughout your relationship.
Documentation and record retention
The Privacy Rule requires you to maintain written policies and procedures that implement all privacy standards, keeping these documents for at least six years from creation date or when last in effect. You must document all privacy practices, patient authorizations, accounting of disclosures, notices provided to patients, and any complaints received. Your SMART on FHIR application needs logging mechanisms that automatically capture required documentation rather than depending on manual record-keeping that creates gaps in your compliance evidence during audits.
Training documentation represents another critical requirement under this HIPAA privacy rule overview. You must train all workforce members on your privacy policies within a reasonable time after they join your organization, provide refresher training when policies change materially, and maintain records proving that training occurred.
Enforcement, penalties, and complaint process
The Office for Civil Rights (OCR) within the Department of Health and Human Services enforces the Privacy Rule through investigations, audits, and penalty assessments. OCR receives thousands of complaints annually from patients who believe their privacy rights were violated, and your organization faces potential investigation whether you operate as a covered entity or business associate. This HIPAA privacy rule overview emphasizes that enforcement actions can result in significant financial penalties and, in severe cases, criminal prosecution that carries prison sentences for individuals who knowingly violate the rules.
OCR prioritizes cases involving willful neglect, systemic violations, and situations where organizations fail to cooperate with compliance reviews. Your healthcare vendor status doesn't shield you from enforcement actions; business associates receive the same scrutiny as covered entities when OCR identifies potential violations during audits or complaint investigations.
Civil monetary penalties and violation tiers
HHS structures civil penalties using a four-tier system that considers whether the violation resulted from lack of knowledge, reasonable cause, willful neglect that you corrected, or willful neglect you left uncorrected. Tier 1 penalties start at $100 per violation with an annual maximum of $25,000, applying when you didn't know about the violation and couldn't have known through reasonable diligence. Tier 4 violations carry minimum penalties of $50,000 per violation with an annual maximum of $1.5 million, targeting situations where you knew about Privacy Rule requirements but chose to ignore them without correction.
Civil penalties escalate rapidly when OCR finds patterns of non-compliance or deliberate disregard for patient privacy rights, making proactive compliance far less expensive than remediation after violations occur.
The distinction between tiers matters because multiple violations can occur in a single incident. If your application improperly discloses PHI for 100 patients, OCR can assess penalties for each affected individual rather than treating the breach as one violation. Settlement agreements often include corrective action plans that require you to implement new policies, conduct additional training, and submit to monitoring periods that extend OCR's oversight beyond the initial penalty assessment.
Criminal penalties for willful violations
The Department of Justice prosecutes criminal violations of HIPAA when individuals knowingly obtain or disclose PHI in violation of the Privacy Rule. Criminal penalties include fines up to $50,000 and one year in prison for basic violations, up to $100,000 and five years for violations committed under false pretenses, and up to $250,000 and ten years for violations committed with intent to sell, transfer, or use PHI for commercial advantage, personal gain, or malicious harm. These penalties apply to individuals within your organization, not just the entity itself.
How to file and respond to complaints
Patients can file Privacy Rule complaints directly with OCR through an online portal, by mail, or by fax within 180 days of when they knew or should have known about the alleged violation. OCR also accepts complaints beyond this deadline when good cause exists for the delay. You must cooperate with OCR investigations by providing requested records, responding to inquiries, and granting access to facilities and systems. Retaliation against patients who file complaints or participate in investigations violates the Privacy Rule and creates additional enforcement exposure for your organization.
What to do now
This HIPAA privacy rule overview covered the foundations that every healthcare vendor needs before building EHR integrations: what PHI is, who must protect it, when you can share it, and what rights patients hold over their information. You now understand the compliance framework that governs your SMART on FHIR applications and the documentation requirements that health systems expect from technology partners.
Your next step is implementing these privacy protections in actual applications. Building compliant EHR integrations traditionally requires months of engineering work to handle authorization workflows, implement minimum necessary controls, support patient access rights, and maintain required documentation. VectorCare eliminates this development burden by providing a no-code platform where HIPAA compliance, SOC2 certification, and Business Associate Agreements come standard with every deployment.
Build and deploy your SMART on FHIR app in weeks instead of months, with privacy protections built into the platform architecture. You focus on your healthcare solution while we handle the compliance infrastructure that keeps you aligned with Privacy Rule requirements.
The Future of Patient Logistics
Exploring the future of all things related to patient logistics, technology and how AI is going to re-shape the way we deliver care.