Role-Based Access Control Definition: RBAC Made Simple Today


Role-Based Access Control Definition: RBAC Made Simple Today
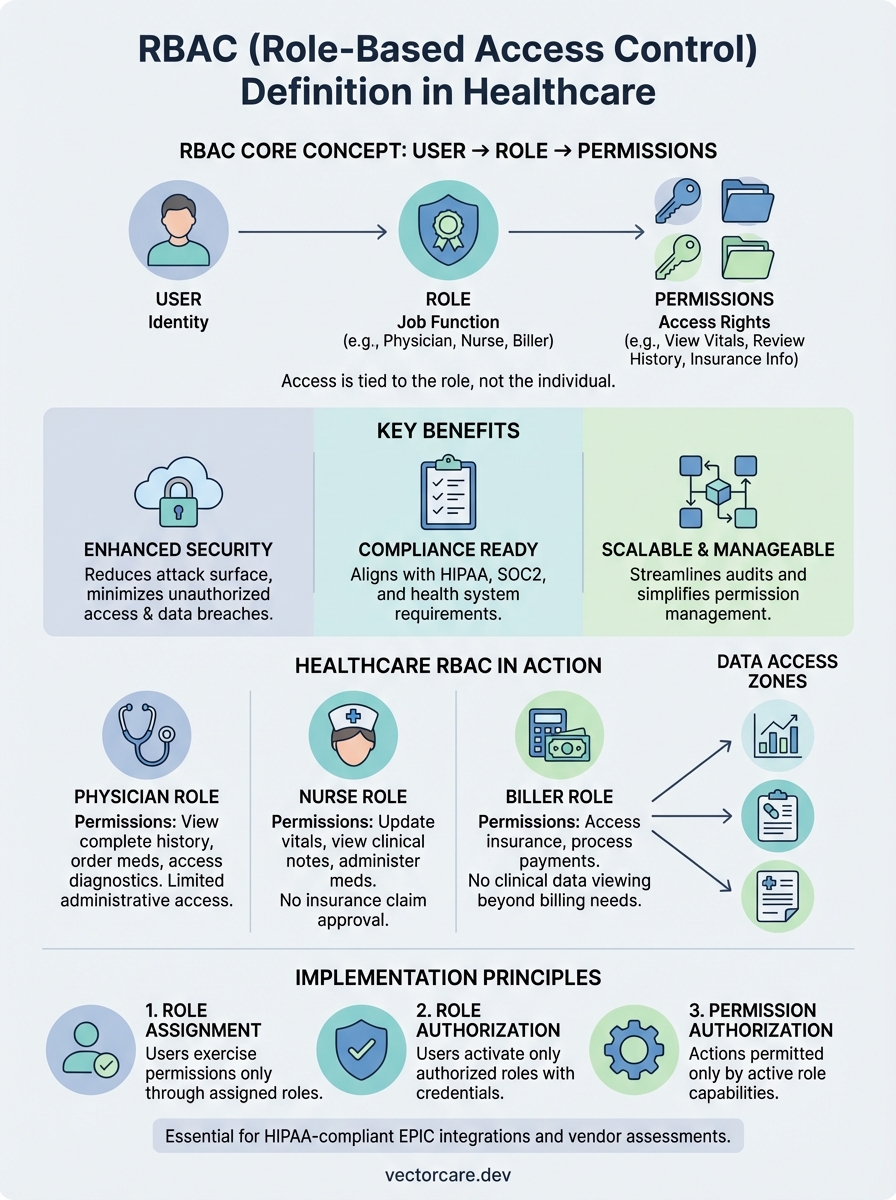
Healthcare vendors building applications that touch patient data face a critical question: who gets access to what? The answer lies in understanding the role based access control definition, a security model that determines permissions based on a user's job function rather than their individual identity. For vendors integrating with EPIC EHR systems, getting this right isn't optional; it's fundamental to compliance and contract success.
RBAC operates on a straightforward principle: users receive access rights tied to their organizational role, nothing more, nothing less. A nurse sees patient vitals. A billing coordinator accesses insurance information. A physician reviews complete medical histories. Each role carries specific permissions that match actual job requirements.
This guide breaks down RBAC into practical terms, covering its core components, how it functions within healthcare security frameworks, and real implementation examples. At VectorCare, we build HIPAA-compliant integrations for healthcare vendors every day, and proper access control sits at the foundation of every application we deploy. Understanding RBAC will help you design smarter workflows and meet the security expectations health systems demand.
Why RBAC matters for security and compliance
Healthcare vendors face intense scrutiny over data security and regulatory compliance. When you build an application that accesses patient records in EPIC or other EHR systems, health systems expect you to demonstrate strict control over who can view, modify, or share sensitive information. The role based access control definition provides the foundation for meeting these expectations through a structured, enforceable security model.
RBAC reduces unauthorized access and data breaches
You limit your attack surface significantly when you implement RBAC properly. Instead of granting broad permissions to individual users, you assign access rights based on predefined roles that match specific job functions. A support technician never needs access to full patient medical histories. A data analyst doesn't require permission to modify clinical records. When you restrict access to only what each role genuinely needs, you minimize exposure to both internal misuse and external threats.
Data breaches in healthcare cost organizations an average of millions of dollars per incident, and most result from excessive permissions or compromised credentials. RBAC creates natural barriers that contain potential damage. If a user account gets compromised, attackers only gain access to what that specific role permits, not your entire system. This containment approach proves especially critical for healthcare vendors because you're handling protected health information (PHI) that carries strict liability requirements under federal law.
RBAC transforms access control from a user-by-user configuration nightmare into a manageable system of role assignments that scales with your organization.
Compliance frameworks require structured access controls
HIPAA mandates that covered entities and their business associates implement technical safeguards to protect electronic PHI. The Security Rule specifically requires you to establish procedures for authorizing access to electronic systems containing PHI. RBAC directly addresses this requirement by creating a documented, auditable framework that shows exactly who has access to what information and why.
SOC2 compliance, which many health systems now require from vendors, evaluates your organization's access control policies and implementation. Auditors look for evidence that you assign permissions based on job responsibilities, regularly review access rights, and promptly revoke permissions when roles change. RBAC provides the structure you need to demonstrate these controls exist and function properly.
Beyond HIPAA and SOC2, you'll encounter specific requirements from individual health systems during contract negotiations. They want to see your security architecture before they allow your application to touch their patient data. A well-implemented RBAC system gives you concrete evidence of security controls, making vendor approval processes faster and more straightforward.
RBAC streamlines audit processes and accountability
When security incidents occur or audits begin, you need to answer one question immediately: who accessed what data and when? RBAC makes this forensic analysis possible by tying every access event to a specific role. You can trace actions back to individuals while also understanding the permission context that allowed those actions.
Healthcare organizations conduct regular access reviews to ensure compliance with regulations and internal policies. Without RBAC, these reviews become overwhelming exercises in checking individual user permissions across multiple systems. With RBAC, you review role definitions and user-to-role assignments, a far more manageable process that you can complete quarterly or even monthly.
Your ability to demonstrate proper access governance influences contract success with health systems. They evaluate whether you can maintain security over time, not just at deployment. RBAC shows you have systematic controls in place rather than ad hoc permission management. This systematic approach reduces your operational overhead while simultaneously strengthening your security posture and compliance readiness.
How RBAC works from roles to permissions
The role based access control definition centers on a three-part architecture: users, roles, and permissions. You separate access rights from individual identities by inserting roles as the critical middle layer. Instead of granting permissions directly to each person, you create roles that represent job functions within your organization, then assign permissions to those roles. Users receive access rights only by membership in one or more roles.

The role assignment process
You begin by defining roles that match actual positions and responsibilities in your organization. A clinical coordinator role might need different system access than a physician or a lab technician. Each role represents a collection of duties that requires specific data access and system capabilities. When a new employee joins your team or an existing employee changes positions, you assign them to the appropriate role rather than configuring individual permissions from scratch.
This assignment happens through your identity management system or directly within your application. Most healthcare vendors integrate with existing directory services like Active Directory or use modern identity providers that support role management. The assignment creates a relationship between the user account and one or more roles, which then determines what that person can do within your system.
Permission mapping to roles
Permissions define the specific actions users can perform on system resources. You map these permissions to roles based on what each job function genuinely needs. A billing role receives permissions to view patient demographics and insurance information but cannot access clinical notes. A nurse role gets permissions to update vital signs and medication records but cannot approve insurance claims.
You build this permission structure by analyzing workflows and determining the minimum access required for each role to complete its responsibilities.
Your application checks role-to-permission mappings whenever a user attempts an action. The system evaluates whether the user's current role includes the permission required for that specific operation. This evaluation happens transparently, creating a security layer that enforces access boundaries without requiring users to understand the underlying permission structure.
Session activation and enforcement
When you log into a system using RBAC, your session activates the permissions associated with your assigned roles. Your application loads these permissions at login and maintains them throughout your session. Every request you make triggers a permission check against your active role's capabilities. If your role permits the action, the system proceeds. If not, you receive an access denial.
This runtime enforcement ensures that changes to role definitions take effect immediately. When administrators modify permissions for a role, those changes apply to all users assigned to that role during their next session. You gain consistency across your entire user base while maintaining the flexibility to adjust access controls as your organization's needs evolve.
Core RBAC rules and common models
The role based access control definition establishes specific rules that govern how permissions flow through your system. These rules create consistency across your security framework and prevent unauthorized access through clearly defined boundaries. Understanding these core principles helps you implement RBAC correctly and avoid common configuration mistakes that expose patient data or create compliance gaps.
Three fundamental RBAC principles
You build effective RBAC on three non-negotiable rules that shape how permissions operate. First, role assignment requires that users can only exercise permissions through assigned roles. Your system never grants direct permissions to individual users outside the role structure. Second, role authorization ensures users activate only roles they're authorized to hold. An employee can't arbitrarily claim a physician role without proper credentials and administrative approval. Third, permission authorization means users can only perform actions their active roles permit. You enforce this rule at every system interaction, checking permissions before allowing any operation on protected resources.
These three principles work together to create a security model where every access decision traces back to explicit role assignments and predefined permission sets.
Organizations that violate these core rules undermine their entire RBAC implementation. When you allow exceptions or direct permission grants outside the role framework, you create security holes that auditors will identify and health systems will reject during vendor assessments. Strict adherence to these principles maintains the integrity of your access control system.
Common RBAC implementation models
You can deploy RBAC using several established models, each offering different complexity levels and capabilities. Flat RBAC represents the simplest implementation where users receive direct role assignments without hierarchy. Every role operates independently with its own permission set. This model works well for smaller organizations with straightforward access requirements but becomes difficult to manage as your user base grows.
Hierarchical RBAC adds role inheritance, allowing you to create parent-child relationships between roles. Senior physicians inherit all permissions from general physician roles while gaining additional administrative capabilities. This structure reduces configuration overhead because you define common permissions once at the parent level rather than duplicating them across multiple similar roles.
Constrained RBAC introduces separation of duties rules that prevent users from holding conflicting roles simultaneously. A user who enters financial transactions cannot also approve those same transactions. Healthcare vendors use these constraints to enforce compliance requirements that mandate segregation of specific functions. Your implementation model choice depends on your organization's size, complexity, and regulatory requirements.
RBAC vs ABAC and other access controls
Understanding where the role based access control definition fits among other access control models helps you select the right security approach for your healthcare application. You encounter several competing frameworks when designing system security, each with distinct advantages and implementation complexity. RBAC offers a middle ground between simplicity and flexibility that makes it particularly suitable for healthcare vendors building EPIC integrations where workflows follow predictable organizational structures.

How RBAC differs from ABAC
Attribute-Based Access Control (ABAC) evaluates multiple attributes about users, resources, and environmental conditions to make access decisions. Instead of checking role membership, ABAC examines characteristics like user department, data classification level, time of access, and geographic location. A physician accessing patient records from within your facility network during business hours receives different permissions than the same physician accessing records remotely at midnight.
ABAC provides more granular control than RBAC but requires significantly more complex policy definition and maintenance overhead.
RBAC groups permissions into roles that remain relatively stable over time. You define a nurse role once and assign it to hundreds of nurses who all receive identical access rights. ABAC requires you to create policy rules that account for countless attribute combinations. While ABAC excels in scenarios demanding contextual access decisions, most healthcare workflows operate within structured role boundaries that make RBAC's simpler model more practical. Healthcare vendors typically choose RBAC for core system access while using ABAC principles for special cases requiring contextual restrictions.
Traditional access control alternatives
Discretionary Access Control (DAC) allows resource owners to determine who can access their data. The person who creates a document decides which other users can read or modify it. You see DAC commonly in file systems where users control sharing permissions for files they create. Healthcare environments generally avoid pure DAC implementations because they require individual discretion rather than enforced organizational policies. When patient safety and regulatory compliance depend on strict access controls, you need systematic enforcement rather than user judgment.
Mandatory Access Control (MAC) assigns fixed security labels to users and resources, then enforces access based on label comparisons. Military and government systems use MAC to create clearance levels like "top secret" or "confidential." Users with "secret" clearance cannot access "top secret" resources regardless of their job role. MAC provides the strongest security guarantees but offers minimal flexibility. Healthcare vendors rarely implement pure MAC systems because clinical workflows require dynamic collaboration across different access levels rather than rigid hierarchical barriers that MAC enforces.
RBAC examples and implementation best practices
You see the role based access control definition come alive when examining real healthcare scenarios and proven deployment strategies. Healthcare vendors building EPIC integrations face concrete access challenges that RBAC solves systematically. Your implementation success depends on understanding both typical use cases and the practical steps required to configure role structures that match operational realities while maintaining security boundaries.
Real-world RBAC scenarios in healthcare
Your healthcare application likely needs distinct roles for different clinical and administrative functions. A physician role receives permissions to view complete patient histories, order medications, and access diagnostic imaging across your integrated system. Nurse practitioners get similar clinical access but with restrictions on certain prescription categories or approval workflows. Medical assistants access patient demographics and vital signs but cannot view sensitive psychiatric notes or substance abuse records that require additional authorization.
Administrative roles operate with different permission sets entirely. Your billing coordinator role includes access to insurance information and payment records but excludes clinical data beyond what billing requires. A quality assurance analyst reviews de-identified patient data for outcomes analysis without seeing personal identifiers. Registration staff create new patient records and schedule appointments but cannot modify existing clinical documentation. Each role reflects actual job responsibilities while enforcing separation of concerns that protects patient privacy and maintains compliance.
When you map roles to real positions within healthcare organizations, you create access patterns that users immediately understand and administrators can audit efficiently.
Steps to implement RBAC effectively
You start implementation by conducting a thorough workflow analysis that documents who currently performs which tasks in your target healthcare environment. Interview clinical and administrative staff to understand their daily activities and the data access each activity requires. This analysis reveals the natural role boundaries that exist within your user population and prevents you from creating artificial role structures that frustrate users or require constant exceptions.
Design your initial role set with simplicity as the priority. You create five to ten foundational roles that cover 80% of your users rather than attempting to build dozens of specialized roles from day one. Start with clear separations like physician, nurse, administrative staff, and system administrator. As your deployment matures, you refine these roles by splitting them into more specific variations based on actual usage patterns and security requirements you observe.
Establish a regular access review process before you go live. You schedule quarterly reviews where role owners verify that permission sets still match job requirements and that user assignments remain appropriate. This ongoing governance prevents permission creep where roles accumulate unnecessary access over time. Document every role definition, its associated permissions, and the business justification for each permission. Health systems conducting vendor assessments will request this documentation, and maintaining it proactively demonstrates your security maturity to potential customers.
Key takeaways
The role based access control definition centers on assigning permissions through predefined roles rather than individual users, creating a security framework that scales efficiently while maintaining strict access boundaries. You gain compliance-ready systems when you implement RBAC correctly, meeting HIPAA requirements and SOC2 standards that health systems demand from their vendors. Your organization benefits from reduced security risks, streamlined audit processes, and clear accountability trails that connect every access decision to specific role assignments.
Healthcare vendors building applications for EPIC integration need robust access controls from day one. RBAC provides the structured approach that makes vendor assessments smoother and contract negotiations faster. When you design your security architecture around role-based principles, you demonstrate the systematic controls that health systems require before allowing access to patient data.
VectorCare handles these security complexities for you when you build your SMART on FHIR application on our platform. We implement HIPAA-compliant RBAC frameworks as part of every deployment, ensuring your application meets health system security expectations without requiring you to build access control infrastructure from scratch.
The Future of Patient Logistics
Exploring the future of all things related to patient logistics, technology and how AI is going to re-shape the way we deliver care.