Oracle Identity Federation: How OIF Enables Cross-Domain SSO


Oracle Identity Federation: How OIF Enables Cross-Domain SSO
Oracle Identity Federation (OIF) solves a fundamental challenge in enterprise environments: enabling users to authenticate once and access applications across multiple security domains without managing separate credentials for each system. For healthcare vendors building integrations with electronic health record systems like EPIC, understanding federated identity architecture becomes essential, secure, standards-based authentication underpins every clinical workflow that touches patient data.
OIF serves as Oracle's enterprise-grade solution for implementing cross-domain single sign-on (SSO), supporting protocols like SAML 2.0, OAuth, and OpenID Connect. It integrates tightly with Oracle Access Management and Oracle Cloud Infrastructure, giving organizations a centralized way to manage identity assertions between trusted partners. Whether you're federating identities between on-premises systems and cloud applications or enabling third-party vendors to access protected resources, OIF provides the framework to do it securely.
This article breaks down how Oracle Identity Federation works, its core components, and step-by-step configuration guidance for cross-domain SSO deployments. At VectorCare, we handle the complexities of healthcare authentication, including SMART on FHIR compliance and OAuth flows, so vendors can launch EPIC integrations without building identity infrastructure from scratch. Understanding OIF's approach to federated identity helps illustrate why proper authentication architecture matters, especially when patient data and clinical workflows are involved.
Why Oracle Identity Federation matters
Traditional authentication models break down when your organization needs to grant access across multiple security domains. You face a choice: replicate user credentials across every system (creating security vulnerabilities and password fatigue) or build custom federation logic for each integration point (consuming engineering resources that should focus on your core product). Oracle identity federation provides a third path, standardizing how identity assertions move between trusted partners while maintaining centralized control over authentication policies.
Security and compliance requirements
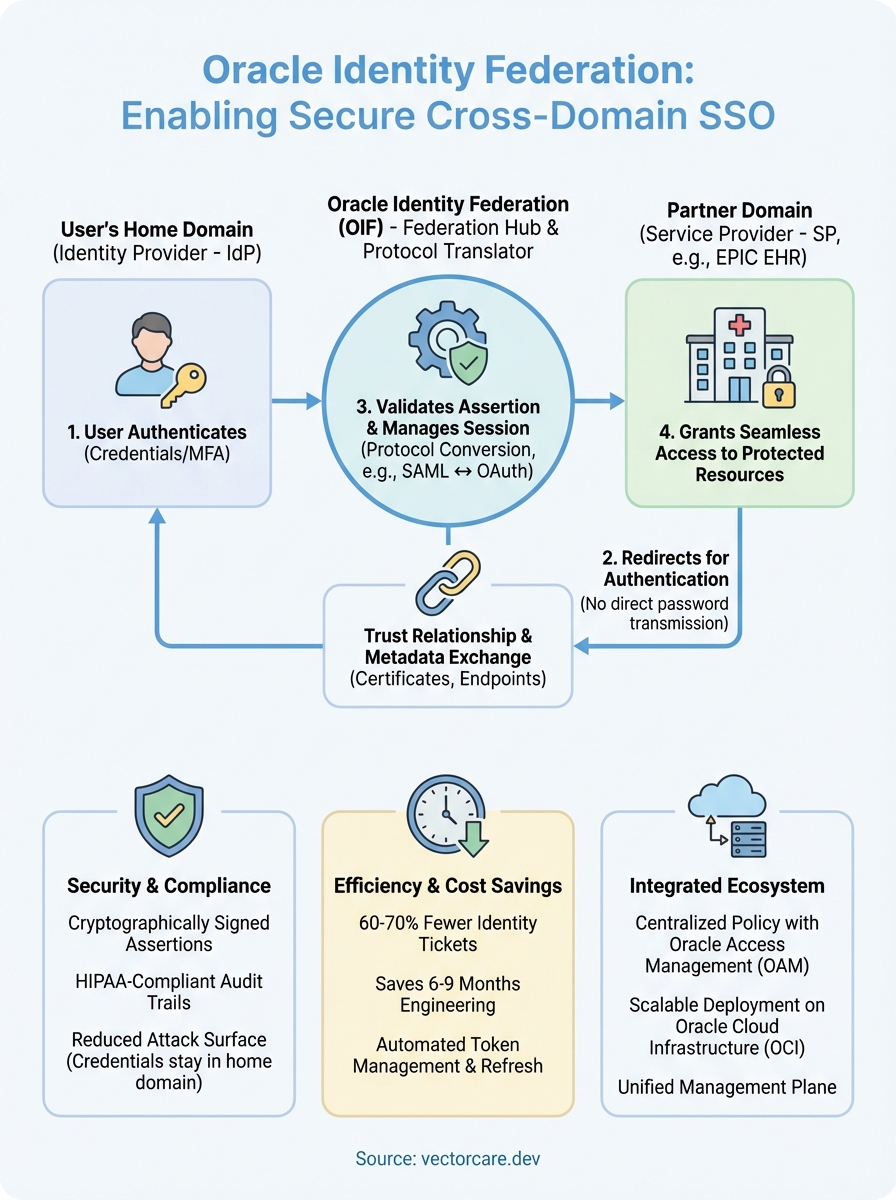
Healthcare environments amplify every authentication weakness. When you connect to an EPIC EHR system, you're handling protected health information (PHI) that falls under HIPAA regulations, and every authentication event creates an audit trail that compliance teams scrutinize. OIF gives you cryptographically signed assertions that prove a user authenticated with your identity provider, eliminating the need to transmit passwords across network boundaries. This architecture reduces your attack surface because credentials never leave the originating domain.
Federated identity architecture shifts authentication responsibility to dedicated identity providers, letting application teams focus on authorization logic rather than credential management.
Organizations leveraging OIF report 60-70% reduction in identity-related support tickets because users authenticate once per session instead of entering credentials for each application. The framework handles token refresh, session management, and assertion validation automatically, preventing common implementation errors that lead to security incidents. You also gain granular control over which attributes (email, role, department) transfer with each assertion, supporting principle of least privilege without custom coding.
Cost and complexity of custom authentication
Building federation logic from scratch consumes 6-9 months of engineering time for most development teams. You need expertise in SAML 2.0 specifications, XML signature validation, certificate management, and protocol-specific error handling. Each partner integration introduces new requirements: one system expects signed assertions, another requires encrypted attributes, and a third needs specific binding protocols. OIF abstracts these complexities into configuration templates, letting you establish trust relationships through administrative interfaces rather than code.
Maintenance costs compound over time as protocols evolve and security standards tighten. When a vulnerability appears in your custom SAML library, you're responsible for patching, testing, and deploying fixes across every application that depends on it. Oracle handles these updates as part of OIF's lifecycle, applying security patches and protocol updates without requiring application changes. Your team avoids the ongoing burden of monitoring specifications for changes and validating implementation compatibility.
Multi-domain access patterns
Modern healthcare delivery spans organizational boundaries. A referral workflow might involve a primary care provider, specialist, imaging center, and pharmacy, each operating in separate security domains with distinct authentication systems. OIF enables you to establish trust relationships once, then route identity assertions across this network as workflows demand. Users authenticate with their home organization's identity provider, and OIF handles assertion translation for downstream systems.
Cloud migrations create temporary multi-domain scenarios where some applications run on-premises while others operate in Oracle Cloud Infrastructure. You need authentication to work consistently across both environments during the transition period, which can span years for complex healthcare systems. OIF bridges these domains, letting you migrate applications incrementally without disrupting user access or forcing password resets. This flexibility becomes essential when you're coordinating changes across multiple stakeholders with different migration timelines.
Key identity federation concepts and terms
Understanding identity federation requires familiarity with specific technical terminology that describes how authentication flows between systems. These concepts form the foundation of how Oracle Identity Federation operates, and you'll encounter them in configuration interfaces, documentation, and troubleshooting scenarios. Grasping these terms upfront prevents confusion when you establish federation relationships or diagnose authentication failures.
Identity provider and service provider
The identity provider (IdP) authenticates users and generates assertions that prove authentication occurred. When you log into your organization's portal, you interact with an IdP that validates your credentials and creates a digitally signed token containing your identity attributes. This provider maintains the authoritative user directory and enforces authentication policies like password complexity or multi-factor requirements.
Service providers (SP) rely on these assertions to grant access to protected resources without performing authentication themselves. An EPIC EHR module acting as a service provider accepts assertions from your organizational IdP, verifying the signature and extracting user attributes needed for authorization decisions. This separation lets you centralize authentication logic while distributing access control to individual applications.
Trust relationships and assertions
You establish trust relationships by exchanging cryptographic certificates between identity providers and service providers before any authentication occurs. These certificates enable signature validation, ensuring that assertions originate from legitimate sources rather than attackers attempting to forge identity claims. Trust configuration typically involves uploading metadata files that contain certificate information, supported protocols, and endpoint URLs.
Assertions carry identity information between trusted partners as XML documents or JSON Web Tokens (JWT). Each assertion includes the authenticated user's identifier, timestamps limiting validity periods, and optional attributes like email or department affiliation. You control which attributes transfer with each assertion, balancing functionality needs against privacy requirements.
Properly configured assertions include audience restrictions that prevent replay attacks where intercepted tokens get reused against unintended service providers.
Federation protocols define the technical mechanisms for exchanging assertions. SAML 2.0 uses browser redirects and XML signatures, while OAuth 2.0 employs access tokens and API-based flows. Your choice of protocol depends on the integration requirements of your target applications and the capabilities of participating identity systems.
How OIF enables cross-domain SSO
Oracle Identity Federation implements cross-domain single sign-on by acting as a protocol translator and assertion broker between security domains. When you authenticate with your home organization's identity provider, OIF captures that authentication event and generates assertions that partner systems recognize. This process happens transparently through browser redirects, meaning users experience seamless access to applications across organizational boundaries without seeing the underlying federation machinery.
Authentication flow across domains
The SSO flow begins when you attempt to access a protected resource in a partner domain. The service provider redirects your browser to OIF, which determines your home identity provider based on configured trust relationships or discovery protocols. OIF then redirects you to authenticate with that IdP, where you enter credentials or complete multi-factor challenges. After successful authentication, the IdP generates a SAML assertion containing your identity and sends it back to OIF through your browser.
OIF validates the assertion signature using the IdP's certificate, confirming the assertion originated from a trusted source. It then transforms the assertion format if the target service provider expects different protocols or attribute mappings. You might authenticate using SAML 2.0 with your corporate IdP, but the partner application requires OAuth tokens. OIF handles this protocol conversion automatically, extracting identity attributes from the SAML assertion and packaging them into OAuth access tokens.
Single sign-on through OIF eliminates the need for users to maintain separate credentials across partner organizations while giving security teams centralized control over authentication policies and access patterns.
Session management and token lifecycle
OIF maintains session state so subsequent requests to federated applications skip the authentication step. Your browser receives a session cookie from OIF after initial authentication, which it presents on future requests. OIF checks this cookie against active sessions before redirecting to identity providers, providing true single sign-on across multiple service providers. Session timeouts align with your organization's security policies, automatically forcing re-authentication when sessions expire or when risk-based rules detect suspicious activity.
How to set up OIF for SAML federation
Setting up Oracle Identity Federation for SAML requires three distinct phases: gathering certificates and metadata from partner organizations, configuring trust relationships in the OIF console, and validating the authentication flow across domains. You complete most configuration through administrative interfaces rather than code, but you need precise attention to certificate handling and endpoint URLs because misconfigurations create authentication failures that are difficult to diagnose.
Pre-configuration requirements
Before you configure oracle identity federation, you obtain X.509 certificates from each participating organization and exchange metadata files that describe supported protocols and endpoints. Your identity provider generates a metadata XML file containing its entity ID, certificate public keys, and single sign-on service URLs. Service providers need this metadata to validate assertion signatures and know where to redirect authentication requests.
You also establish network connectivity between OIF and partner identity systems, verifying that firewalls permit HTTPS traffic on standard ports. SAML flows rely on browser redirects, so you configure public-facing URLs that users' browsers can reach. Organizations running OIF behind load balancers need to ensure session affinity so subsequent requests in the authentication flow reach the same OIF instance that initiated the transaction.
Configuring identity provider trust
You upload the identity provider's metadata file through the OIF administration console, which automatically extracts certificate information and endpoint configurations. The console lets you map SAML attributes from incoming assertions to internal user attributes that your applications understand. Your IdP might send "mail" as the email attribute, but your application expects "email," so you create mapping rules that translate between these formats during assertion processing.

Trust configuration includes setting assertion validity periods that balance security requirements against network latency, typically ranging from 60 to 300 seconds.
Establishing service provider trust
Service provider configuration follows the inverse process. You export OIF's metadata and provide it to each service provider that will accept assertions. You then register each service provider in OIF's configuration, specifying which user attributes to include in assertions sent to that partner. Testing validates the complete flow by attempting authentication through each configured service provider and verifying that assertions contain expected attributes.
OIF with Oracle Access Management and OCI
Oracle Identity Federation operates as a core component within Oracle's broader identity management stack, integrating directly with Oracle Access Management (OAM) to provide enterprise-scale authentication capabilities. This tight integration lets you deploy centralized identity governance across both on-premises infrastructure and cloud environments without managing separate federation engines for each deployment model. Organizations running hybrid architectures gain consistent authentication experiences regardless of where applications reside.
Integration with Oracle Access Management
OAM provides the underlying policy engine that enforces authentication requirements and authorization rules while OIF handles the protocol-level federation mechanics. When you deploy both products together, OAM's authentication modules feed identity assertions to OIF, which then packages them for external partners using SAML or OAuth protocols. This division of responsibility keeps authentication policies centralized in OAM while federation configuration remains isolated in OIF's administration interface.
You configure OAM's authentication schemes to define password policies, multi-factor requirements, and adaptive authentication rules. OIF inherits these policies automatically when generating assertions for federated partners, ensuring that security standards apply consistently across all access paths. Your security team maintains a single policy repository rather than duplicating rules across multiple identity systems.
Deploying oracle identity federation alongside Oracle Access Management creates a unified control plane for managing both internal application access and cross-domain federation relationships through consolidated administrative interfaces.
Deployment in Oracle Cloud Infrastructure
OCI deployments leverage managed identity services that handle infrastructure provisioning, patching, and scaling without requiring dedicated operations teams. You provision OIF instances through Oracle's Identity Cloud Service or deploy standalone containers in OCI compute environments based on your architecture requirements. Cloud deployments eliminate certificate management complexity because OCI's certificate service automates renewal and distribution across federated endpoints.
Healthcare vendors connecting to EPIC EHR systems often run OIF in OCI alongside their application infrastructure to maintain consistent network latency and simplified firewall rules. Placing federation components in the same cloud region as your applications reduces authentication overhead while keeping all healthcare data within compliant infrastructure boundaries.
Final takeaways
Oracle identity federation provides the infrastructure for secure cross-domain authentication, handling protocol translation and assertion management without requiring custom code from your engineering team. You gain centralized control over identity flows between trusted partners while users experience seamless access across organizational boundaries. The framework's integration with Oracle Access Management and OCI creates a unified authentication architecture that scales from single partnerships to complex multi-domain ecosystems, particularly valuable in healthcare environments where patient data protection and audit compliance drive every technical decision.
Healthcare vendors building EPIC integrations face authentication requirements that extend beyond basic federation. You need SMART on FHIR compliance, OAuth flows configured for clinical workflows, and HIPAA-compliant infrastructure that handles these identity exchanges securely. VectorCare eliminates this complexity by providing a managed platform that handles authentication, federation, and compliance requirements out of the box. Build and deploy your SMART on FHIR app in days instead of spending months configuring identity infrastructure that distracts from your core product development.
The Future of Patient Logistics
Exploring the future of all things related to patient logistics, technology and how AI is going to re-shape the way we deliver care.