HIPAA Minimum Necessary Standard: Examples And Exceptions


HIPAA Minimum Necessary Standard: Examples And Exceptions
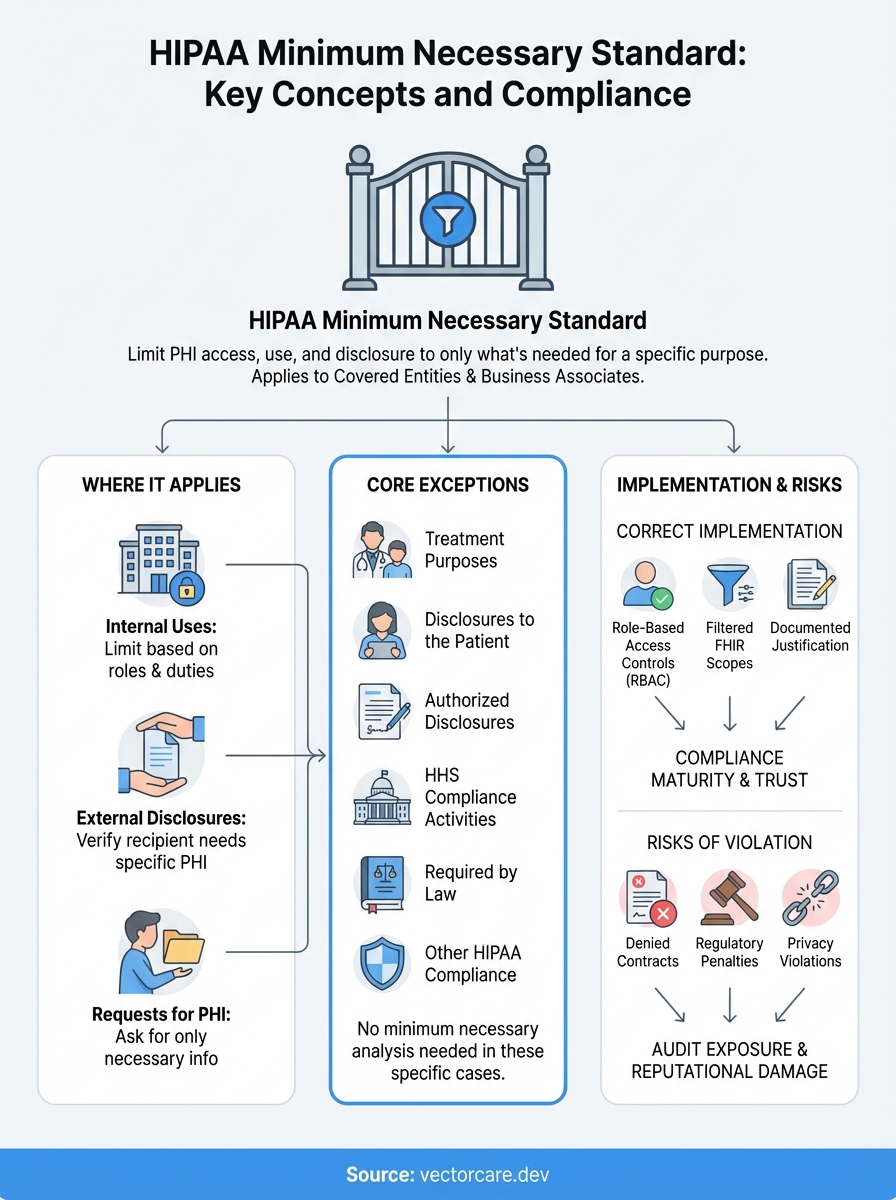
Every time patient data moves between systems, whether through an EHR integration, a third-party app, or a referral workflow, HIPAA's rules apply. The HIPAA minimum necessary standard requires covered entities and their business associates to limit PHI access and disclosure to only what's needed for a specific purpose. It sounds straightforward, but applying this principle across complex healthcare technology stacks creates real compliance challenges.
For healthcare vendors building integrations with systems like EPIC, understanding where the minimum necessary standard applies (and where it doesn't) is critical. Get it wrong, and you risk regulatory penalties, denied contracts with health systems, or worse, patient privacy violations that erode trust. Get it right, and you demonstrate the kind of compliance maturity that health systems demand from their technology partners.
This article breaks down the HIPAA minimum necessary standard with practical examples and clear explanations of the exceptions. Whether you're configuring data access for a SMART on FHIR application or designing workflows that pull patient information, you'll walk away with actionable guidance. At VectorCare, we build these compliance considerations directly into our no-code platform, so healthcare vendors can launch EPIC integrations that meet HIPAA requirements from day one.
Why the minimum necessary standard matters
The HIPAA minimum necessary standard directly impacts your ability to win health system contracts and maintain them. When you integrate with EPIC or other EHR systems, compliance teams scrutinize your data access patterns during vendor assessments. They want evidence that your application requests only the specific patient information required for its stated purpose, nothing more. Health systems reject vendors who demonstrate overly broad data requests because it exposes them to regulatory risk and creates liability gaps in their business associate agreements.
Business consequences of getting it wrong
Your sales cycle extends significantly when you cannot demonstrate minimum necessary compliance. Health system privacy officers block contract approvals until you document exactly what PHI your application accesses, why it needs each data element, and how you limit access to authorized users. This documentation requirement adds weeks or months to implementation timelines. Some health systems maintain explicit policies that reject integrations requesting full patient record access when the use case only requires specific data points like demographics or medication lists.
Beyond delayed contracts, you face ongoing audit exposure. OCR enforcement actions increasingly target cases where organizations accessed or disclosed more PHI than necessary for treatment, payment, or healthcare operations. The financial penalties for systematic violations reach into millions of dollars, but the reputational damage to your vendor relationships often costs more. Health systems terminate contracts with vendors who create compliance incidents, and those terminations spread through the tight-knit health IT procurement community.
Technical debt from poor design choices
When you build applications that request excessive data scopes from the start, you create technical debt that compounds over time. Your data model becomes bloated with fields you do not actively use. Your backend systems store PHI unnecessarily, expanding your attack surface and increasing breach notification obligations if security incidents occur. Each additional data element you request creates another point of failure in your compliance program.
The minimum necessary standard forces you to make intentional design decisions about data access rather than defaulting to "request everything and filter later."
Engineers who do not understand minimum necessary often implement FHIR resource requests that pull complete patient records when workflows only need targeted information. Your application might request full Observation resources when it only needs vital signs, or pull entire Encounter histories when recent visits suffice. These overly permissive scopes create compliance violations even when you never display or use the excess data in your user interface.
Operational complexity in multi-tenant environments
The standard creates unique challenges when you deploy your application across multiple health systems. Each implementation requires role-based access controls tailored to that organization's specific workflows and job functions. What counts as "necessary" for a physician differs from what a nurse, scheduler, or billing specialist needs. Your platform must support granular permission configurations that align with each customer's policies, not a one-size-fits-all approach that overprovisions access to simplify your engineering.
Managing these configurations across dozens or hundreds of health system deployments becomes operationally expensive without the right architecture. You need systems that enforce minimum necessary by default, with explicit justification required to expand data access. Manual configuration of access controls for each user role at each customer creates an unsustainable operational burden as your customer base grows.
The legal definition and where it appears in HIPAA
The HIPAA minimum necessary standard appears in 45 CFR § 164.502(b) and establishes a fundamental principle that governs how covered entities and business associates handle protected health information. The regulation states that when using or disclosing PHI, or when requesting PHI from another covered entity, you must make reasonable efforts to limit the information to the minimum necessary to accomplish the intended purpose. This applies to uses, disclosures, and requests, but the Privacy Rule does not define specific quantities or types of information that meet the standard in all situations.

Where the regulation appears in the Code of Federal Regulations
You find the primary minimum necessary requirements in Section 164.502(b) of Title 45, which covers the general use and disclosure provisions of the Privacy Rule. Additional implementation specifications appear in Section 164.514(d), which details how covered entities must implement the minimum necessary standard through policies and procedures. These sections work together to create both the obligation and the practical framework for compliance.
The regulation requires you to establish role-based access protocols for routine disclosures and to develop criteria for non-routine requests. Section 164.514(d)(2) specifically mandates that you identify persons or classes of persons in your workforce who need access to PHI to carry out their duties, and for each category, you must determine the minimum necessary PHI for those duties. This creates a documentation requirement that goes beyond simple technical implementation.
What the standard actually requires you to do
The standard operates through a reasonableness test rather than prescriptive rules about specific data elements. You must implement policies and procedures that limit PHI to the minimum necessary to accomplish the intended purpose of a particular use, disclosure, or request. The Department of Health and Human Services deliberately avoided creating specific checklists or data field requirements because what counts as minimum necessary varies based on the purpose, the workforce member's role, and the specific circumstances of each disclosure.
Your organization bears the burden of documenting why specific PHI elements are necessary for each defined purpose, not simply asserting that you need comprehensive access.
Covered entities must review and update these determinations as part of their ongoing compliance programs. When circumstances change, such as implementing new workflows or adding system integrations, you need to reassess whether your existing minimum necessary determinations still apply. This creates an iterative compliance obligation that extends throughout your application's lifecycle, not just during initial implementation.
When the minimum necessary standard applies
The HIPAA minimum necessary standard applies to every use and disclosure of PHI your organization makes, with specific exceptions we'll cover in the next section. You face this compliance obligation whether you access patient data internally for your own operations, share it with external parties, or request it from other covered entities. Understanding when the standard triggers helps you design compliant workflows from the start rather than retrofitting access controls after implementation.
Internal uses within your organization
When your workforce members access PHI in your systems, the minimum necessary standard requires you to limit access based on job roles and specific duties. A billing specialist should not see clinical notes if their work only requires demographic information and procedure codes. Your role-based access controls must reflect actual workflow requirements, not aspirational access that someone might theoretically need in an edge case scenario.
You must implement this through documented policies that identify which workforce categories need which PHI elements. Each role category requires its own determination of minimum necessary data access. Your system administrators might need broad access for technical maintenance, but that access still falls under the minimum necessary standard and requires documentation of why that level of access serves a legitimate purpose tied to their specific responsibilities.
External disclosures to third parties
The standard applies when you disclose PHI to business associates, other covered entities, or any external party for treatment, payment, or healthcare operations purposes. When your application sends patient data to a laboratory, referral coordinator, or analytics platform, you must verify that you transmit only the PHI those recipients need to perform their specific function. Sending complete patient records when the recipient only needs test results creates a compliance violation.
Your disclosure decisions require documented justification that demonstrates why each PHI element you share is necessary for the stated purpose of the disclosure.
This creates particular challenges for SMART on FHIR applications that pull data through standardized resource types. You cannot request entire FHIR resources when your use case only requires specific data elements within those resources. Your application must implement filtering mechanisms that limit the PHI you retrieve to match your documented minimum necessary determinations.
When requesting PHI from others
When you request patient information from another covered entity, you must limit your request to the minimum necessary to accomplish your purpose. This applies whether you request data through an EHR interface, a FHIR API call, or a traditional records request. The requesting organization bears the burden of ensuring its requests comply with the standard, and the disclosing entity relies on your determination that the requested information meets the minimum necessary threshold for your stated purpose.
The six exceptions you need to know
The HIPAA minimum necessary standard includes six specific exceptions where you do not need to limit PHI to the minimum necessary. These exceptions recognize situations where applying the standard would interfere with critical healthcare functions or where other Privacy Rule protections already apply. Understanding these exceptions prevents you from creating unnecessary barriers to legitimate data sharing while maintaining compliance with HIPAA's broader privacy framework.
Treatment purposes
When healthcare providers request or disclose PHI for treatment purposes, the minimum necessary standard does not apply. A physician can request a patient's complete medical history from another provider without justifying why each data element is necessary for treatment decisions. This exception recognizes that clinical judgment requires comprehensive information, and providers need the flexibility to access all relevant patient data when delivering care.
Your application must distinguish between treatment workflows and other purposes. If your SMART app supports clinical decision-making or care coordination, you can request broader data scopes than you could for administrative or operational functions. However, you still need to document that your use case qualifies as treatment under HIPAA's definition, which requires direct patient care activities rather than research, quality improvement, or population health analytics.
Disclosures to the patient
When you disclose PHI directly to the individual who is the subject of the information, the minimum necessary standard does not apply. Patients have the right to access their complete health records under HIPAA's access provisions, and you cannot limit what they receive based on minimum necessary determinations. This exception extends to patient-facing applications that allow individuals to view or download their own health information through patient portals or third-party apps they authorize.
Authorized disclosures and compliance activities
The standard does not apply when you disclose PHI pursuant to a valid patient authorization. If a patient signs an authorization form that permits you to share their records with a specific third party for a defined purpose, you can disclose the information described in that authorization without additional minimum necessary analysis. Similarly, disclosures to the Department of Health and Human Services for compliance reviews or enforcement investigations are exempt, as are uses and disclosures required by other laws or needed to comply with other HIPAA provisions.
These exceptions do not eliminate your broader obligation to implement reasonable safeguards that protect PHI from inappropriate access or disclosure.
Minimum necessary vs least privilege access
You encounter two distinct but related frameworks when building secure healthcare applications: the HIPAA minimum necessary standard and the least privilege access principle from information security. Healthcare vendors often conflate these concepts or assume compliance with one automatically satisfies the other. Understanding the differences between them helps you design systems that meet both regulatory requirements and security best practices without creating redundant controls or compliance gaps.
How the concepts differ in scope
The HIPAA minimum necessary standard governs what PHI you use, disclose, or request based on the specific purpose of that action. It operates at the data element level and asks whether you need a patient's social security number, medication history, or lab results to accomplish your stated objective. This creates a purpose-driven framework where the same user might legitimately access different data sets depending on which task they perform.
Least privilege access represents a broader information security principle that limits user permissions to only those resources required to perform job functions. It applies to all types of data and systems, not just PHI, and focuses on preventing unauthorized access through technical controls. A least privilege model restricts which databases, applications, and file systems your users can access, regardless of the specific data elements within those resources.
The minimum necessary standard asks what PHI you should access for a specific purpose, while least privilege determines whether you can access the systems containing that PHI at all.
Where the frameworks overlap in practice
Both frameworks require you to implement role-based access controls that match user permissions to job responsibilities. When you configure access for a billing coordinator in your SMART application, least privilege prevents them from accessing clinical systems they do not need, while minimum necessary limits the specific PHI fields they can view within the billing module. These controls work together to create layered protections that satisfy both HIPAA compliance and security requirements.
Your technical implementation must address both frameworks simultaneously. You need system-level permissions that enforce least privilege by controlling which applications and databases different user roles can access. Within those systems, you need field-level controls that implement minimum necessary by hiding or restricting specific PHI elements based on the user's current workflow and documented access determinations.
Implementation considerations for healthcare applications
When building EPIC integrations or other EHR connections, you must design your data access layer to support both frameworks from the start. Your FHIR requests should only retrieve the resources that least privilege policies permit for each user role, and within those resources, you should filter to only the data elements that meet minimum necessary requirements. This prevents your application from pulling complete patient records when your compliance documentation supports more limited access scopes.
Routine vs non-routine requests and disclosures
The HIPAA minimum necessary standard requires different implementation approaches based on whether your PHI disclosures occur routinely or represent one-time requests. You must establish written policies for routine disclosures that document your minimum necessary determinations in advance, while non-routine requests demand individual evaluation each time they occur. This distinction shapes how you configure your SMART applications and what documentation your compliance program needs to demonstrate regulatory adherence.
How HIPAA defines routine disclosures
Routine disclosures represent recurring, predictable uses of PHI that occur as part of your standard workflows. When your application automatically sends lab orders to a testing facility, transfers patient demographics to a scheduling system, or shares medication lists with a pharmacy network, these actions qualify as routine because they follow established patterns that you can define in advance. You must document what PHI each routine disclosure includes and why those specific data elements are necessary for the stated purpose.
Your written policies for routine disclosures should identify the types of healthcare providers or entities that receive information, the categories of PHI you disclose to each recipient type, and the conditions or purposes that trigger each disclosure. Once you establish these policies, your workforce can execute routine disclosures without conducting a minimum necessary analysis for each individual transaction. This creates operational efficiency while maintaining compliance, provided your policies accurately reflect your actual practices and undergo regular review to ensure they remain current with your workflows.
Non-routine requests require individual review
Non-routine disclosures involve unique or infrequent requests that fall outside your established policies. When a researcher requests specific patient records for a study, an attorney requests information for litigation, or a health system asks for documentation about an unusual clinical scenario, you must evaluate each request individually to determine what PHI is minimally necessary. This evaluation cannot rely on your routine disclosure policies because the circumstances differ from your standard operations.
Your individual review must consider the specific purpose of each non-routine request and limit the disclosure to only the PHI elements that serve that particular purpose.
The person handling non-routine requests must have training to apply the minimum necessary standard correctly. You need documented procedures that guide this decision-making process, including who within your organization has authority to approve non-routine disclosures and what factors they should consider when determining the appropriate scope of information to release.
Policy documentation requirements
Your compliance program must maintain written evidence of both your routine disclosure policies and your non-routine request procedures. These documents serve as your primary defense if regulators question whether your disclosures comply with the minimum necessary standard. You need policies that specify the PHI elements included in each type of routine disclosure, the job roles authorized to make those disclosures, and the frequency at which you review and update these determinations.
Practical examples by role and use case
Understanding how the HIPAA minimum necessary standard applies in real workflows helps you configure access controls correctly from the start. The standard operates differently depending on who accesses PHI, why they need it, and what systems they use to retrieve it. These examples demonstrate how to translate compliance requirements into specific technical configurations and policy decisions that protect patient privacy while supporting legitimate healthcare operations.
Clinical staff accessing patient records
When a nurse prepares to administer medications, they need access to current medication orders, allergy information, and recent vital signs, but they do not need the patient's complete psychotherapy notes or historical records from unrelated visits. Your application should expose only the FHIR resources that support medication administration workflows, such as MedicationRequest, AllergyIntolerance, and recent Observation resources filtered to vital signs. You configure role-based access that limits the data fields and time ranges the nurse can view based on their documented responsibilities.
Physicians treating a patient in the emergency department require broader access than nurses because they make diagnosis and treatment decisions that depend on comprehensive information. Your system can provide them with extended access to Condition resources, historical Encounters, and diagnostic results, but even this expanded scope should filter out information that does not relate to the current episode of care. A physician treating a broken arm does not need automatic access to psychiatric evaluations or genetic counseling records unless those records contain information relevant to the current treatment plan.
Administrative and billing personnel
Billing coordinators need patient demographics, insurance information, procedure codes, and diagnosis codes to submit claims, but they do not require clinical details about symptoms, treatment plans, or lab results. You implement minimum necessary by configuring their access to only the FHIR resources that contain billing-relevant data: Patient, Coverage, Claim, and ExplanationOfBenefit resources. Their interface should not display clinical narrative fields even when those fields exist in the underlying resources your application retrieves.
Your access controls must prevent administrative staff from viewing clinical information simply because it exists in the same database or resource bundle as the billing data they legitimately need.
Scheduling staff require even more limited access than billing personnel. They need patient name, contact information, and appointment history to coordinate visits, but they do not need diagnosis codes, insurance details, or treatment information. Your application should restrict their FHIR queries to specific data elements within Patient and Appointment resources, filtering out fields that serve billing or clinical purposes rather than scheduling coordination.
SMART on FHIR application scopes
When you request OAuth scopes for a referral coordination application, you should limit your request to the specific resources your workflow requires. A referral app might need patient/Condition.read, patient/MedicationRequest.read, and patient/Procedure.read scopes to share relevant clinical context with the receiving provider, but it should not request patient/*.read scope that grants access to all FHIR resources. Each scope you request must align with your documented minimum necessary determinations that explain why your referral workflow needs those specific resource types.
Population health analytics applications present unique challenges because they analyze aggregate data across many patients. You still apply the minimum necessary standard by limiting the data elements you extract from each patient record to only those required for your specific analytics purpose. An analytics app tracking diabetes outcomes needs HbA1c results and diagnosis codes, but it does not need complete laboratory panels or unrelated clinical observations. You configure your FHIR queries to retrieve specific Observation codes rather than pulling all available lab results for each patient.
Common violations and tricky gray areas
You face compliance risk when your application's data access patterns drift from your documented minimum necessary determinations or when you encounter situations where the standard's application remains unclear. Regulators frequently cite violations involving routine disclosures that include unnecessary PHI or access controls that grant broader permissions than job roles require. Understanding where organizations commonly fail helps you design systems that avoid these pitfalls from the start rather than discovering compliance gaps during audits or security incidents.
Over-scoping FHIR resource requests
The most common violation occurs when your application requests complete FHIR resource types when your documented use case only requires specific data elements within those resources. Your referral coordination app might pull entire Observation resources when your workflow only needs vital signs, inadvertently capturing lab results, imaging reports, and other clinical observations you never use. Regulators consider this a violation because you accessed and potentially stored PHI beyond what your minimum necessary determination supports, regardless of whether you display that excess data to users.
Even when your user interface hides unnecessary fields, retrieving and storing that PHI in your backend systems creates a compliance violation if your policies do not justify access to those specific data elements.
Role creep in existing deployments
Your access controls become non-compliant when job responsibilities change but your permission configurations remain static. A medical assistant initially granted access to scheduling and demographic data might gradually take on billing responsibilities, leading administrators to expand their system access rather than reassigning them to a properly configured billing role. This incremental expansion creates permissions that exceed minimum necessary requirements because the user accumulates access rights from multiple roles without anyone documenting why a single person needs that broad combination of PHI.
Pre-populating forms with unnecessary data
Applications that automatically fill intake forms or assessment tools by pulling data from the EHR create gray area situations. You might retrieve a patient's complete medication list to pre-populate a surgical clearance form, but if the clearance process only requires current anticoagulants and anesthesia-relevant medications, you potentially violate the hipaa minimum necessary standard by accessing the full list. Your system should implement filtering logic that matches the specific clinical purpose of each form rather than pulling comprehensive datasets because it simplifies your engineering.
Legacy system integration challenges
Older systems that lack granular access controls create compliance dilemmas when you integrate them with modern EHR platforms. Your laboratory information system might only support all-or-nothing access to test results, preventing you from limiting specific users to only the result types their roles require. This technical limitation does not exempt you from the minimum necessary standard, but it does create a documented exception you must address through compensating controls like audit logging, user training, and access attestation processes.
How to implement minimum necessary in SMART apps
You translate the hipaa minimum necessary standard into technical reality through deliberate design choices in your SMART on FHIR application architecture. This requires you to make access limitation decisions at multiple layers of your application stack, from the initial OAuth scope requests through your backend data processing and front-end presentation logic. Each layer provides opportunities to restrict PHI access to only what your documented use case requires, and failing to implement controls at any layer creates compliance vulnerabilities.
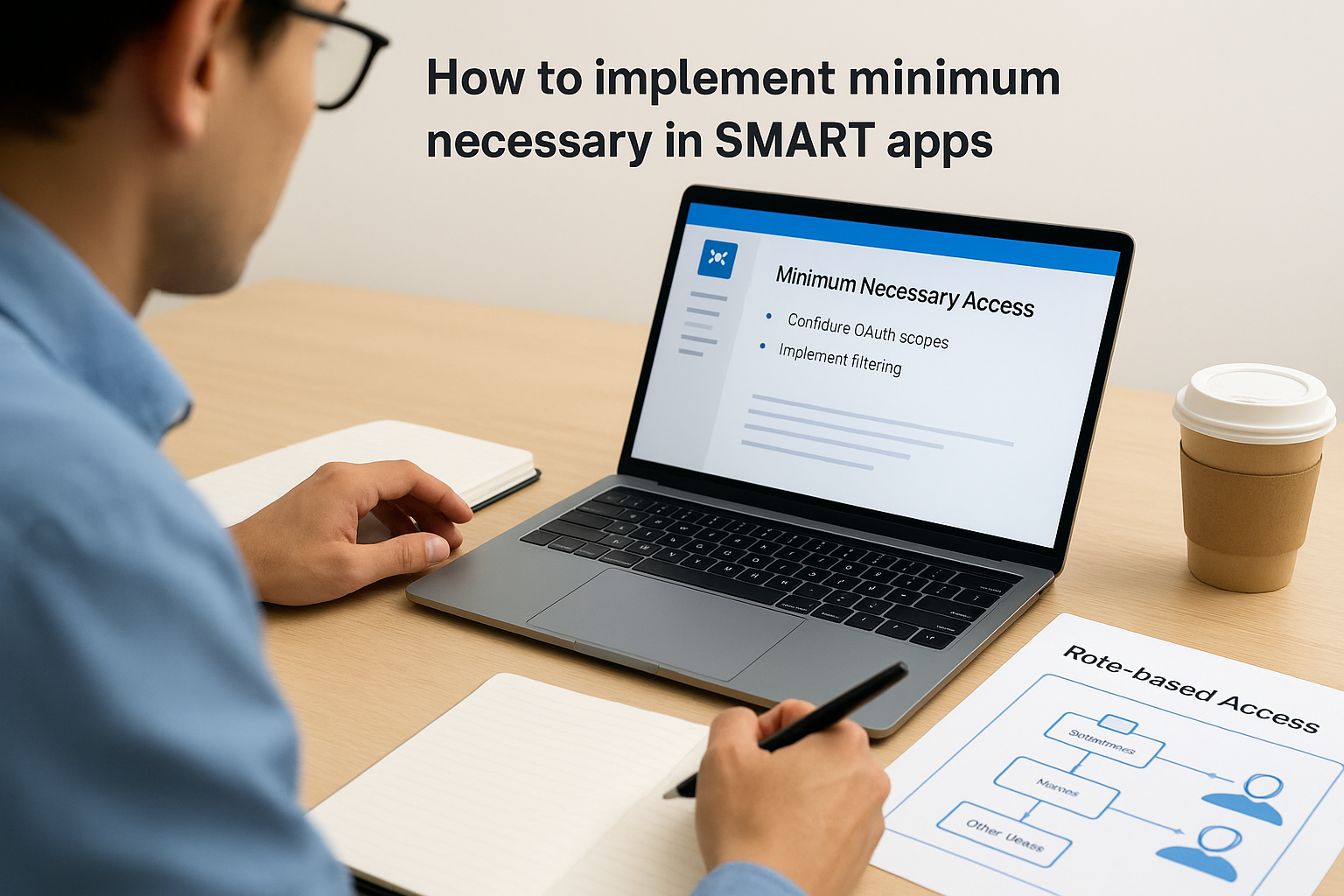
Configure OAuth scopes based on documented use cases
Your SMART app launch begins with an OAuth authorization request that specifies which FHIR resources you need to access. You must request only the scopes that align with your minimum necessary determinations rather than requesting broad wildcards like patient/*.read. A medication reconciliation app should request patient/MedicationRequest.read and patient/AllergyIntolerance.read scopes, not comprehensive access to all patient resources. This scope limitation creates your first compliance checkpoint because the authorization server will only grant access to the resource types you explicitly request.
Document your justification for each scope in your compliance policies before you submit your app for EPIC Showroom approval or deploy it at health systems. Reviewers will compare your requested scopes against your stated purpose, and broad scope requests without clear justification delay approvals or trigger rejections.
Implement filtering at the resource level
Once you receive authorization, your FHIR API calls must include search parameters that filter results to match your minimum necessary requirements. Instead of requesting all Observation resources for a patient, you specify _code parameters that limit results to the specific LOINC codes your workflow needs. Your referral coordination app might filter to vital signs observations using codes like 85354-9 for blood pressure rather than pulling complete laboratory and imaging results that serve no purpose in your referral workflow.
Your API queries should retrieve exactly the data elements your documented policies justify, not broader datasets that you filter out later in your application code.
Build role-based access into your application layer
Your application must implement additional access controls beyond the OAuth scopes you receive from the authorization server. Different users within the same health system have different roles that require different PHI access levels. You configure your application to check user roles on every data access request and apply filters that match their documented permissions. A scheduler viewing a patient record through your app sees only demographic and appointment information, while a nurse sees clinical data relevant to their care coordination responsibilities.
These role configurations must exist as structured policies in your system, not hardcoded logic that requires engineering work to modify. Your customers need the ability to adjust role permissions to match their specific organizational policies without depending on custom development for each implementation.
Final takeaways
The hipaa minimum necessary standard creates concrete compliance obligations that extend throughout your application's entire data lifecycle. You must document your minimum necessary determinations before you request FHIR scopes, implement filtering at both the API and application layers, and maintain role-based access controls that match each user's specific job responsibilities. These requirements apply to every PHI use and disclosure except the six specific exceptions we covered, and regulators expect you to demonstrate your compliance through written policies and technical controls that work together.
Healthcare vendors that build these protections into their architecture from the start avoid the costly retrofitting that comes with compliance gaps discovered during health system audits. Your customers will ask for evidence that your application implements the standard correctly, and your ability to demonstrate that compliance directly impacts your sales cycle and contract approval timelines.
VectorCare handles these compliance requirements as part of our no-code platform, so you can build and deploy SMART on FHIR applications that meet HIPAA standards without engineering custom access controls for every health system deployment.
The Future of Patient Logistics
Exploring the future of all things related to patient logistics, technology and how AI is going to re-shape the way we deliver care.