HIPAA Compliance Requirements: Privacy, Security & Breaches


HIPAA Compliance Requirements: Privacy, Security & Breaches
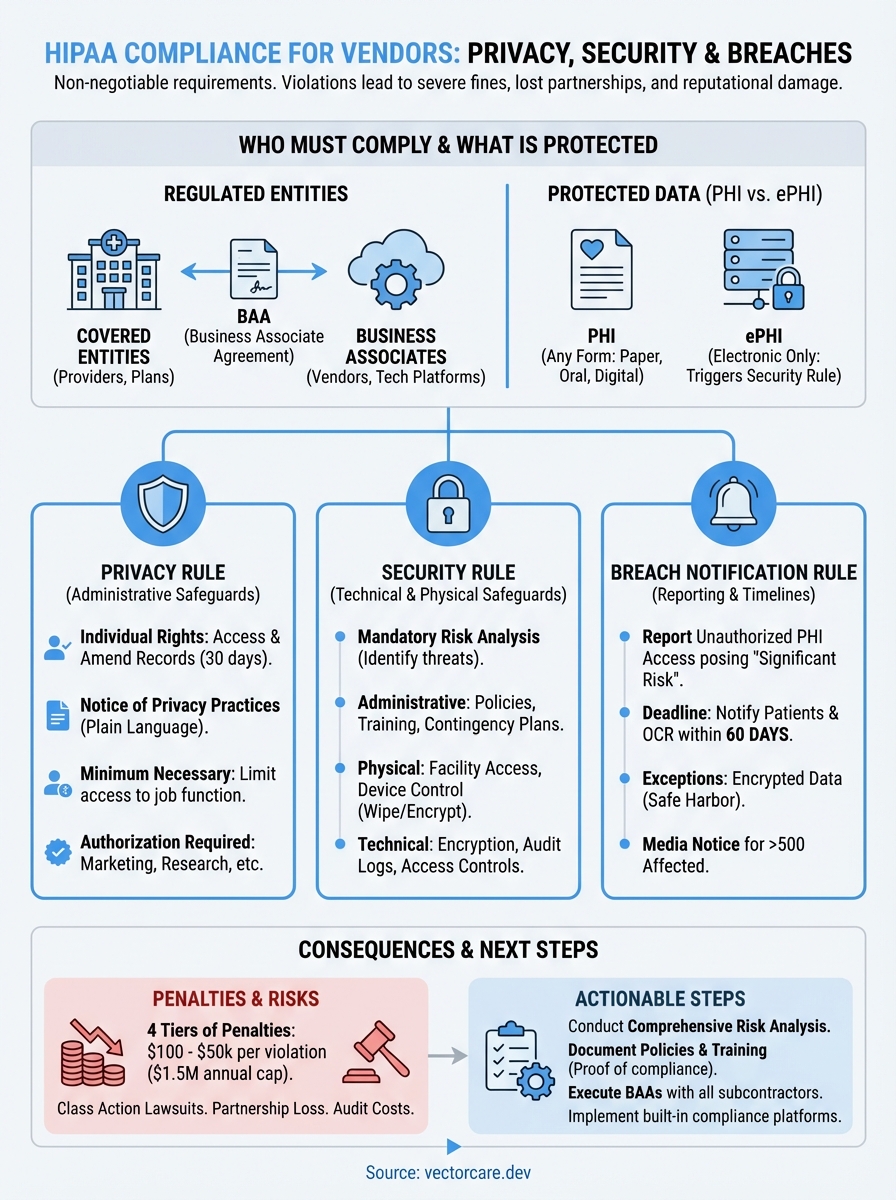
Healthcare vendors building applications that touch patient data face a non-negotiable reality: HIPAA compliance requirements aren't optional. A single violation can result in fines ranging from $100 to $50,000 per incident, with annual maximums reaching $1.5 million per violation category. Beyond the financial penalties, non-compliance can destroy partnerships with health systems before they even begin.
Whether you're developing a remote patient monitoring solution, a clinical decision support tool, or any application that integrates with electronic health records like EPIC, you need to understand three core frameworks: the Privacy Rule, the Security Rule, and the Breach Notification Rule. These aren't just bureaucratic checkboxes, they're the foundation that health systems evaluate when deciding whether to work with your company. Getting them wrong means losing contracts; getting them right opens doors.
This guide breaks down each requirement into actionable steps, covering everything from administrative safeguards to technical controls to what happens when things go wrong. At VectorCare, we build HIPAA and SOC2 compliance directly into our no-code platform for EPIC integrations, so we've seen firsthand how these requirements translate into real-world implementation. Below, you'll find the practical framework you need to achieve and maintain compliance, without the legal jargon that makes most HIPAA resources unreadable.
Why HIPAA compliance requirements matter
The Health Insurance Portability and Accountability Act creates legal obligations that carry real consequences, not theoretical ones. You face three distinct penalty tiers based on the level of negligence: unknowing violations start at $100 per incident, reasonable cause violations begin at $1,000, and willful neglect can reach $50,000 per incident. The Office for Civil Rights doesn't stop at single-incident fines. When you multiply these penalties by the number of patients affected and the duration of non-compliance, settlement amounts routinely exceed millions of dollars.
Financial exposure beyond direct penalties
Your direct penalty exposure represents only part of the financial risk. Class action lawsuits from affected patients can dwarf OCR fines, especially when breaches expose sensitive data like HIV status, mental health records, or substance abuse treatment. These lawsuits take years to resolve and require expensive legal defense regardless of the outcome. Insurance companies also respond to HIPAA violations by raising premiums or dropping coverage entirely, leaving you exposed to future incidents.
Remediation costs add another layer of expense. When OCR identifies deficiencies during an audit or investigation, they require corrective action plans that typically demand extensive technical upgrades, policy overhauls, and third-party monitoring. The 2024 settlement with a regional health system required two years of external compliance monitoring at an estimated cost of $3 million beyond the $4.3 million fine. Your engineering team gets pulled from product development to address compliance gaps, creating opportunity costs that extend far beyond the settlement check.
"The true cost of a HIPAA violation isn't the fine, it's the 18 months you spend fixing what should have been built correctly from day one."
Health system partnership requirements
Health systems evaluate your compliance posture before signing any contract, and they use it as a filtering mechanism rather than a negotiation point. Their procurement and legal teams maintain standardized questionnaires that probe every aspect of your HIPAA program, from your risk analysis methodology to your incident response procedures. You need documentation proving not just that you follow hipaa compliance requirements, but that you've built systematic processes to maintain them over time.
Business associate agreements create contractual liability that extends beyond regulatory requirements. When you sign a BAA with a health system, you accept financial responsibility for breaches caused by your systems or practices. Health systems now routinely include indemnification clauses requiring you to cover their costs if your security failure exposes their patients. This means your data breach could trigger liability for both OCR penalties and contractual damages to your covered entity partner.
Competitive positioning and market access
Your competitors who achieve compliance first capture market share while you're still building safeguards. Health systems work with vendors who can deploy immediately, not those who need six months to implement proper security controls. This timing advantage compounds because reference customers from early partnerships help you win subsequent contracts. Every month you delay compliance represents lost opportunities that your competitors secure.
The EPIC App Orchard requires verified compliance before listing applications in their showroom, where health systems discover integration solutions. Without this listing, you miss the primary discovery channel that procurement teams use when evaluating vendors. SOC2 Type II reports and attestations of HIPAA compliance have become table stakes rather than differentiators, meaning you need them just to participate in vendor selection processes.
Who must comply and how to tell
HIPAA establishes two distinct categories of regulated entities: covered entities and business associates. Your classification determines which specific obligations apply to your organization and how you structure your compliance program. The distinction matters because misclassifying your role creates compliance gaps that auditors catch immediately, and claiming you're not covered when you actually are triggers the highest penalty tier for willful neglect.

Covered entities: the starting point
Healthcare providers qualify as covered entities when they transmit health information electronically in connection with standard transactions like claims, eligibility verification, or referrals. This includes hospitals, clinics, pharmacies, and individual practitioners who bill insurance electronically. Health plans that pay for medical care, including insurers, HMOs, and employer-sponsored plans covering more than 50 participants, fall into this category automatically. Healthcare clearinghouses that process health information between non-standard and standard formats round out the three types of covered entities.
You don't need to handle claims or billing to be regulated. A telemedicine platform that stores patient consultation notes becomes a covered entity even if it never submits insurance claims, because it provides healthcare services and creates electronic health records. Similarly, an employer health plan that covers 51 employees must comply with hipaa compliance requirements regardless of whether it uses a third-party administrator.
Business associates and the chain of liability
You become a business associate when a covered entity or another business associate gives you access to protected health information to perform functions on their behalf. This includes technology vendors hosting patient data, billing companies processing claims, consultants analyzing health records, and any service provider that creates, receives, maintains, or transmits PHI. The relationship requires a business associate agreement that specifies your obligations and liability.
"If you touch PHI for someone else's healthcare operations, you're a business associate. The question isn't whether you want to comply, it's whether you want to work in healthcare."
Most healthcare software vendors operate as business associates rather than covered entities. Your remote patient monitoring platform becomes a business associate when hospitals use it to track patient vitals. Your clinical decision support tool falls under business associate requirements when it accesses patient records to generate recommendations. The key factor is whether you handle PHI on behalf of a covered entity, not whether you directly treat patients or submit claims.
Subcontractors create another layer of obligation. When you hire a cloud hosting provider to store PHI, that provider becomes your business associate, and you need a BAA with them. This chain extends indefinitely, with each link requiring proper agreements and compliance verification.
PHI vs ePHI and what HIPAA protects
The distinction between protected health information and electronic protected health information determines which specific safeguards you need to implement. Protected health information, or PHI, includes any individually identifiable health data that a covered entity or business associate creates, receives, maintains, or transmits in any form. This covers paper records, oral communications, and digital files equally. Electronic protected health information, or ePHI, represents the subset of PHI that exists in electronic form, triggering additional technical requirements under the Security Rule.
What counts as PHI
You handle PHI whenever you work with information that identifies a patient and relates to their physical or mental health, the provision of healthcare services, or payment for those services. This includes obvious identifiers like names, Social Security numbers, and medical record numbers, but extends to less apparent data points. Email addresses, IP addresses, biometric identifiers, and even full-face photographs qualify as PHI when linked to health information.
The 18 identifiers that HIPAA explicitly lists create a bright-line test for what you must protect. Geographic subdivisions smaller than a state, dates directly related to an individual (birth dates, admission dates, death dates), telephone numbers, fax numbers, and vehicle identifiers all require safeguards. Your patient intake forms that collect these data points create PHI the moment you record them, whether you store them digitally or in filing cabinets.
"PHI isn't just the diagnosis or lab result. It's any piece of information that could identify a patient combined with any health-related detail."
Electronic PHI and the digital difference
Electronic protected health information triggers the Security Rule's technical safeguards on top of the Privacy Rule's baseline protections. Your databases, backup tapes, email systems, and cloud storage all contain ePHI when they hold patient information. This includes data in motion, such as HL7 messages exchanged between systems, and data at rest, like archived patient records on a storage area network.
The Security Rule requires you to implement encryption, access controls, audit logs, and transmission security for ePHI. These technical requirements don't apply to paper records under hipaa compliance requirements, creating different compliance obligations based on the medium. Your EPIC integration that pulls patient demographics electronically needs encryption and authentication controls that a paper chart room wouldn't require.
Information HIPAA doesn't cover
HIPAA protections don't extend to employment records that covered entities maintain in their role as employers, even when those records contain health information. Your company's workers' compensation files or fitness-for-duty evaluations fall outside HIPAA's scope. Similarly, educational records protected by FERPA remain outside HIPAA jurisdiction, including health information maintained by schools about their students.
De-identified data that strips out all 18 identifiers and meets the Safe Harbor method escapes HIPAA regulation entirely. You can use, share, and analyze this anonymized information without business associate agreements or patient authorization, but the de-identification process requires rigorous documentation to withstand audit scrutiny.
HIPAA Privacy Rule requirements
The Privacy Rule establishes national standards for how you handle protected health information in any form, creating baseline protections that apply before you even touch electronic systems. You need to implement administrative controls that govern who accesses PHI, why they access it, and how you document those decisions. These requirements apply to every interaction with patient data, from scheduling appointments to sharing records with specialists, and they form the foundation that the Security Rule builds upon when you handle electronic records.
Individual rights under the Privacy Rule
Patients hold six specific rights that you must support through policies and procedures. They can request access to their complete medical records within 30 days of asking, with one 30-day extension allowed if you provide written notice of the delay. You must provide copies in the format they request, whether electronic or paper, and charge only reasonable, cost-based fees for producing those copies. When patients believe information is incorrect, they can request amendments to their records, though you can deny the request if you document why the information is accurate and complete.
The accounting of disclosures gives patients a list of everyone who received their PHI for purposes other than treatment, payment, or operations during the past six years. You need systems that track when you shared records with public health authorities, law enforcement, or researchers. Restriction requests allow patients to ask you to limit how you use their information, and you must honor requests to restrict disclosures to health plans when they paid out-of-pocket in full for a service.
Notice of Privacy Practices and minimum necessary
Your Notice of Privacy Practices must explain in plain language how you use and disclose PHI, what rights patients have, and how they can file complaints. You distribute this notice at the first service delivery and post it prominently in your facility and on your website. Covered entities must obtain written acknowledgment that patients received the notice, though you can document good faith efforts if a patient refuses to sign.
The minimum necessary standard requires you to limit PHI access, use, and disclosure to only what's reasonably needed for the specific purpose. Your staff members get access only to the data fields their job functions require, not blanket access to all patient records. When you send records to another provider for consultation purposes, you include only the relevant portions rather than the entire chart.
"Minimum necessary isn't a suggestion. If your medical assistant can view psychiatric notes they don't need for check-in, you're violating the Privacy Rule."
Uses and disclosures requiring authorization
You need signed patient authorization before using PHI for marketing, selling patient lists, or most research activities. The authorization form must specify exactly what information you'll disclose, to whom, for what purpose, and when the authorization expires. Psychotherapy notes receive extra protection, requiring separate authorization even when other PHI can be shared for treatment. You cannot condition treatment on a patient signing an authorization, except in limited research contexts where the study protocol requires it.
HIPAA Security Rule requirements
The Security Rule focuses exclusively on electronic protected health information, establishing standards for how you protect digital patient data through administrative, physical, and technical safeguards. Unlike the Privacy Rule's broad coverage of all PHI formats, these requirements apply only when you create, receive, maintain, or transmit health information electronically. You must conduct a risk analysis to identify threats to ePHI, then implement safeguards that reduce risks to reasonable and appropriate levels based on your organization's size, complexity, and technical capabilities. This flexibility means your specific controls will differ from another organization's approach, but the underlying hipaa compliance requirements remain constant across all covered entities and business associates.

Administrative safeguards
You need documented security management processes that identify risks, implement protective measures, detect security incidents, and maintain ongoing safeguards. This includes designating a security official responsible for developing and implementing your security policies, which creates clear accountability for compliance failures. Your workforce security procedures must cover how you authorize access, establish oversight, and ensure employees understand their responsibilities through training and sanctions.
Security awareness training reaches beyond basic password hygiene. You must address malware protection, log-in monitoring, password management, and physical security of devices in regular sessions. Your contingency planning requires a data backup plan, disaster recovery procedures, an emergency mode operation plan, and testing protocols that verify you can restore ePHI access after disruptions. You document these processes and update them as your technology environment changes or risks evolve.
Physical safeguards
Physical access controls limit who enters facilities, workstations, and storage areas containing ePHI systems. You implement facility security plans that include visitor controls, door locks, security cameras, and alarm systems appropriate to your environment. Workstation security policies dictate where employees can access ePHI, whether they can use personal devices, and how you protect screens from unauthorized viewing.
"Leaving a workstation unlocked with patient records visible violates the Security Rule just as severely as a software vulnerability does."
Your device and media controls govern how you receive, remove, and dispose of hardware and electronic media containing ePHI. This means wiping hard drives before disposal, encrypting laptops that travel outside your facility, and tracking who removes backup tapes from your data center.
Technical safeguards
Access controls ensure that only authorized users reach electronic systems containing ePHI through unique user IDs, emergency access procedures, automatic logoff, and encryption where appropriate. Your audit controls create logs of system activity that let you detect unauthorized access attempts and investigate security incidents after they occur. Integrity controls verify that ePHI hasn't been altered or destroyed inappropriately through mechanisms like checksums or digital signatures.
Transmission security protects ePHI in motion between systems using encryption and integrity controls. When your application sends patient data to an EHR system or receives lab results from an interface, you need controls that prevent interception and tampering during transit.
How to run a HIPAA risk analysis
The Security Rule mandates that you conduct a comprehensive risk analysis to identify potential threats to your ePHI and implement appropriate safeguards. This isn't a one-time checkbox exercise but rather an ongoing process that you repeat whenever your organization introduces new systems, changes workflows, or experiences security incidents. Your risk analysis forms the foundation of your security program because it determines which safeguards you need based on actual threats rather than generic best practices. Health systems will request your most recent risk analysis during vendor evaluations, and OCR routinely examines the quality and thoroughness of these assessments during audits of hipaa compliance requirements.
Identify and document assets
Start by creating an inventory of all systems, applications, and locations where you store, process, or transmit ePHI. This includes your primary databases, backup systems, workstations, mobile devices, cloud services, and network infrastructure. Document who has access to each asset, what type of ePHI it contains, and how information flows between systems. Your EPIC integration might pull patient demographics into your application database, send alerts through an email service, and store logs in a separate monitoring tool, each of which needs documentation.
Physical locations matter as much as digital systems. You map where servers sit, which offices contain workstations accessing ePHI, and how backup media moves between facilities. This inventory reveals shadow IT systems that compliance teams often miss, like the laptop a developer uses to test with production data or the shared drive where staff save patient reports.
Assess threats and vulnerabilities
Examine each asset for potential threats that could compromise ePHI confidentiality, integrity, or availability. Consider both external threats like hackers, malware, and phishing attacks, and internal threats such as employee error, unauthorized access by staff, and physical theft of devices. Your vulnerabilities might include unpatched software, weak password policies, lack of encryption, or inadequate access controls that give users more permissions than their roles require.
"The biggest vulnerability in most healthcare systems isn't sophisticated hackers, it's the basic controls you never implemented because you didn't realize they were missing."
Document specific scenarios for your environment. A remote monitoring device that transmits patient vitals over Wi-Fi faces different threats than an on-premise claims processing system. Your mobile application accessing ePHI through public networks introduces vulnerabilities that desktop applications in secured facilities don't encounter.
Determine likelihood and impact
Assign a realistic probability to each threat based on your security controls and industry trends. A brute force attack against your login system becomes more likely if you don't enforce multi-factor authentication. Estimate the potential impact if each threat materializes, considering how many patients would be affected, what types of sensitive information could be exposed, and how long systems might remain unavailable.
Calculate your risk level by combining likelihood and impact ratings. High-probability, high-impact scenarios demand immediate attention, while low-probability, low-impact risks might accept current controls.
Document findings and implement controls
Create a written report that lists every identified risk, its rating, and your planned response. You either implement safeguards to reduce the risk, accept the risk with documented justification, or transfer the risk through insurance or contracts. Your implementation plan includes specific controls, responsible parties, deadlines, and how you'll verify effectiveness.
Update your risk analysis annually at minimum, and immediately after significant changes like new integrations, security incidents, or technology deployments.
Business associates and BAAs
Your relationship with covered entities hinges on a business associate agreement that creates contractual liability beyond regulatory requirements. This legally binding contract specifies exactly how you'll safeguard PHI, what you can do with that information, and what happens if you cause a breach. Without a signed BAA in place, health systems cannot legally share patient data with your organization, which means your EPIC integration or healthcare application remains useless regardless of its technical capabilities. The BAA transforms hipaa compliance requirements from abstract regulations into concrete obligations with financial consequences spelled out in dollar amounts and indemnification clauses.
What business associate agreements must include
Your BAA must define the permitted uses and disclosures of PHI that you'll receive, limiting you to only the activities necessary to perform services for the covered entity. The agreement requires you to implement appropriate safeguards preventing unauthorized use or disclosure, including the administrative, physical, and technical controls outlined in the Security Rule. You agree to report any security incidents or breaches to the covered entity according to specific timelines, typically within 24 to 72 hours of discovery depending on the contract terms.
The BAA establishes your obligation to ensure any subcontractors who access PHI also sign business associate agreements, creating a chain of liability that extends through your entire vendor ecosystem. You must return or destroy all PHI at contract termination, or if return proves infeasible, you extend protections and limit further uses. Covered entities retain the right to audit your compliance practices and terminate the contract immediately if you violate material terms, which means a single serious security lapse can end your partnership.
"A BAA doesn't just protect the covered entity. It protects you by clearly defining your obligations and limiting liability to specific breach scenarios."
When you need a BAA and when you don't
You need a signed BAA before receiving any PHI from a covered entity or another business associate, which means negotiating the agreement should happen during your sales process rather than after you've already begun integration work. Conduit services that merely transmit data without accessing it, like internet service providers or encrypted email services that never decrypt messages, fall under an exception and don't require BAAs. Your cloud hosting provider, however, requires a BAA because they can access systems containing ePHI even if they don't routinely view patient records.
Timing matters critically for compliance verification. You confirm that every vendor in your supply chain who touches PHI has executed BAAs before you pass them any patient data, and you maintain copies of these agreements for audit purposes. Health systems will request your BAA template and your list of subcontractor BAAs during vendor assessments.
HIPAA breach notification requirements
The Breach Notification Rule kicks in the moment you discover that unauthorized individuals have acquired, accessed, used, or disclosed protected health information in a way that compromises its security or privacy. You face strict timelines for notifying affected patients, the Office for Civil Rights, and potentially the media, with penalties escalating rapidly when you miss deadlines. These hipaa compliance requirements create specific obligations that differ based on the number of people affected and whether the breach resulted from your actions or a business associate's failure. Your notification process needs documented procedures covering discovery, investigation, notification content, and delivery methods, because OCR examines how you handled each step when they investigate complaints or audit your organization.

What qualifies as a reportable breach
A breach occurs when someone accesses PHI without authorization in a way that poses significant risk of financial, reputational, or other harm to the affected individuals. Your employee viewing records of patients they're not treating triggers the breach definition, as does losing an unencrypted laptop containing patient data or a hacker stealing your database. The breach presumption means you assume every unauthorized access qualifies as reportable unless you document a risk assessment proving the incident posed low probability of compromise.
Your risk assessment examines four factors: the nature and extent of PHI involved, who accessed the information without authorization, whether you actually recovered the PHI, and what safeguards you had in place. An encrypted device that's lost but never decrypted might pass this test, while a stolen unencrypted backup tape almost certainly fails it.
"The breach clock starts ticking when anyone in your organization should reasonably have known about the incident, not when you officially discover it."
The 60-day notification timeline
You must notify affected individuals within 60 days of discovering the breach, which means 60 days from when you first became aware or should have become aware through reasonable diligence. This timeline doesn't pause while you investigate the scope or gather contact information. Your notification to OCR happens simultaneously when the breach affects fewer than 500 people, using their web portal to submit required details. Breaches affecting 500 or more individuals require immediate OCR notification within the same 60-day window, plus you must alert prominent media outlets serving the affected area.
Who you must notify and how
Individual notifications go to each affected person at their last known address via first-class mail, or by email if they previously agreed to electronic communications. Your notice must include a brief description of what happened, the types of information involved, steps individuals should take to protect themselves, what you're doing to investigate and prevent future incidents, and contact procedures for questions. When you cannot locate contact information for 10 or more individuals, you post substitute notice on your website homepage for 90 days and in major print or broadcast media.
Exceptions to notification requirements
You skip notification only when your documented risk assessment proves low probability of compromise or when the breach falls under specific safe harbor provisions. Encryption meeting NIST standards provides safe harbor because properly encrypted data that's lost or stolen doesn't require notification if you never recovered the decryption key. Good faith access by workforce members or authorized persons doesn't count as a breach if the information wasn't further disclosed improperly.
Training, policies, and audit readiness
Your compliance program lives or dies based on whether your workforce understands their obligations and whether you can prove that understanding to auditors. You need documented training programs, comprehensive policies that cover every aspect of hipaa compliance requirements, and systems that demonstrate ongoing adherence to those standards. Health systems evaluate your audit readiness during vendor assessments by requesting policies, training records, and evidence of monitoring activities. OCR investigations similarly demand proof that you've implemented formal programs rather than informal practices, which means your documentation needs to withstand scrutiny from external reviewers who assume you're non-compliant until you prove otherwise.
Workforce training requirements
You must train every workforce member who handles PHI within a reasonable period after they join your organization, typically interpreted as within 30 days of their start date. Your training covers the Privacy Rule, Security Rule, your internal policies, and specific procedures relevant to each employee's role. Security awareness training addresses password management, phishing recognition, physical security practices, and incident reporting procedures that apply to daily activities. You document who attended each session, what topics you covered, when the training occurred, and how you verified comprehension through tests or acknowledgment forms.
Annual refresher training keeps your workforce current on policy changes, emerging threats, and lessons learned from security incidents in your organization or industry. You track completion rates and follow up with employees who miss scheduled sessions, because gaps in training records create red flags during audits.
"Training records aren't just compliance documentation. They're your primary defense when an employee's mistake leads to a breach investigation."
Policy documentation essentials
Your policy manual addresses every administrative, physical, and technical safeguard that the Security Rule requires, plus Privacy Rule procedures for patient rights, minimum necessary access, and authorized disclosures. Each policy specifies who's responsible for implementation, what steps they take, how you monitor compliance, and what sanctions apply for violations. You maintain version control showing when you updated policies, what changed, and why you made those revisions.
Preparing for audits
Your audit readiness program includes regular internal assessments that test whether actual practices match documented policies. You maintain logs of system access, incident investigations, risk analyses, BAA reviews, and training completion that auditors request during reviews. Your evidence includes dated screenshots, signed forms, and system reports that prove ongoing compliance rather than documentation created right before an audit.
Penalties, enforcement, and common violations
The Office for Civil Rights enforces hipaa compliance requirements through a four-tier penalty structure that scales based on your level of culpability and the harm caused. Your financial exposure ranges from $100 per violation for unknowing breaches to $50,000 per violation for willful neglect, with annual caps reaching $1.5 million per violation category. OCR collected over $140 million in settlements during 2024 alone, targeting organizations of all sizes from solo practitioners to major hospital systems. Understanding which violations trigger investigations helps you prioritize compliance efforts on the areas that draw the most scrutiny and carry the highest financial risk.
The four-tier penalty structure
Tier 1 applies when you didn't know and couldn't reasonably have known about the violation, starting at $100 per incident with a $25,000 annual maximum. Tier 2 covers reasonable cause violations where you should have known about the issue but lack evidence of willful neglect, ranging from $1,000 to $50,000 per violation with a $100,000 cap. Tier 3 addresses willful neglect that you corrected within 30 days, imposing $10,000 to $50,000 per violation with a $250,000 maximum. Tier 4 represents uncorrected willful neglect, the most severe category, requiring $50,000 per violation with a $1.5 million annual ceiling.
"OCR doesn't just fine you for the breach itself. They multiply the penalty by every patient affected and every day you remained non-compliant."
State attorneys general can also impose civil penalties under their own laws, and criminal prosecution becomes possible when you knowingly obtain or disclose PHI improperly. Criminal penalties reach up to $250,000 and 10 years imprisonment for offenses committed with intent to sell, transfer, or use PHI for commercial advantage or personal gain.
Most common violations that trigger penalties
Insufficient risk analyses top the list of violations OCR identifies during audits, with organizations either skipping the analysis entirely or conducting superficial assessments that miss obvious threats. Lack of business associate agreements with vendors who access PHI represents another frequent finding, particularly when organizations assume certain service providers don't need contracts. Inadequate access controls that give workforce members more permissions than necessary for their roles violate the minimum necessary standard and create unnecessary exposure.
Missing or incomplete breach notifications to OCR and affected individuals result in significant penalties because they demonstrate both the original security failure and subsequent non-compliance with reporting requirements. Organizations that fail to provide patients access to their medical records within 30 days face enforcement action, especially when they impose excessive copying fees or ignore requests entirely.
Where to go from here
You've now covered the complete framework of hipaa compliance requirements, from Privacy and Security Rules to breach notification procedures. Your next step involves conducting or updating your risk analysis, documenting your findings, and implementing the administrative, physical, and technical safeguards that address your specific vulnerabilities. Organizations that wait until health systems request compliance documentation during contract negotiations face rushed implementations that miss critical controls and create unnecessary risk.
Building HIPAA-compliant integrations with EHR systems like EPIC requires technical expertise that pulls your engineering team away from product development. VectorCare handles the compliance complexity for you, providing a no-code platform with built-in HIPAA and SOC2 compliance that lets you deploy SMART on FHIR applications in weeks rather than months. Your team focuses on your core product while we manage the security controls, BAAs, and ongoing compliance monitoring that health systems demand.
The Future of Patient Logistics
Exploring the future of all things related to patient logistics, technology and how AI is going to re-shape the way we deliver care.